wudijun opened a new issue, #4559: URL: https://github.com/apache/shenyu/issues/4559
### Is there an existing issue for this? - [X] I have searched the existing issues ### Current Behavior Apache shenyu version 2.5.1 has added SPEL expressions, which allow attackers to enter malicious SPEL to execute arbitrary system commands ### Expected Behavior Security filtering is recommended for SPEL expressions ### Steps To Reproduce In version 2.5.1, the Mock plugin has been added and supports SPEL expression functionality, which creates a security issue that allows attackers to execute arbitrary system commands through SEPL expressions 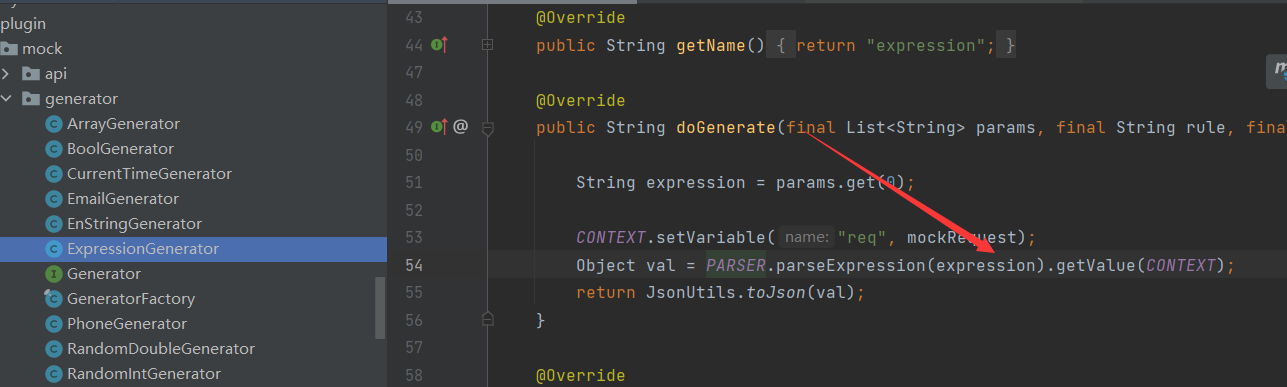 1.Create a new selector at Mock 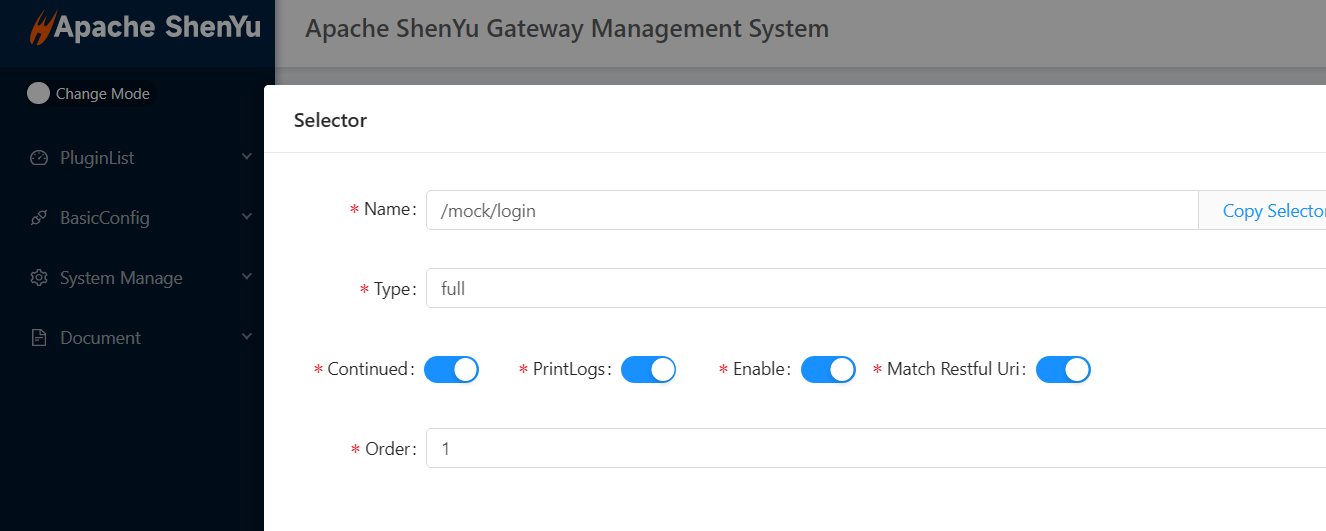 2.Create a new corresponding rule and enter a malicious SPEL expression here with the content of ${expression | T (java. lang. Runtime). getRuntime(). exec ("calc. exe")} 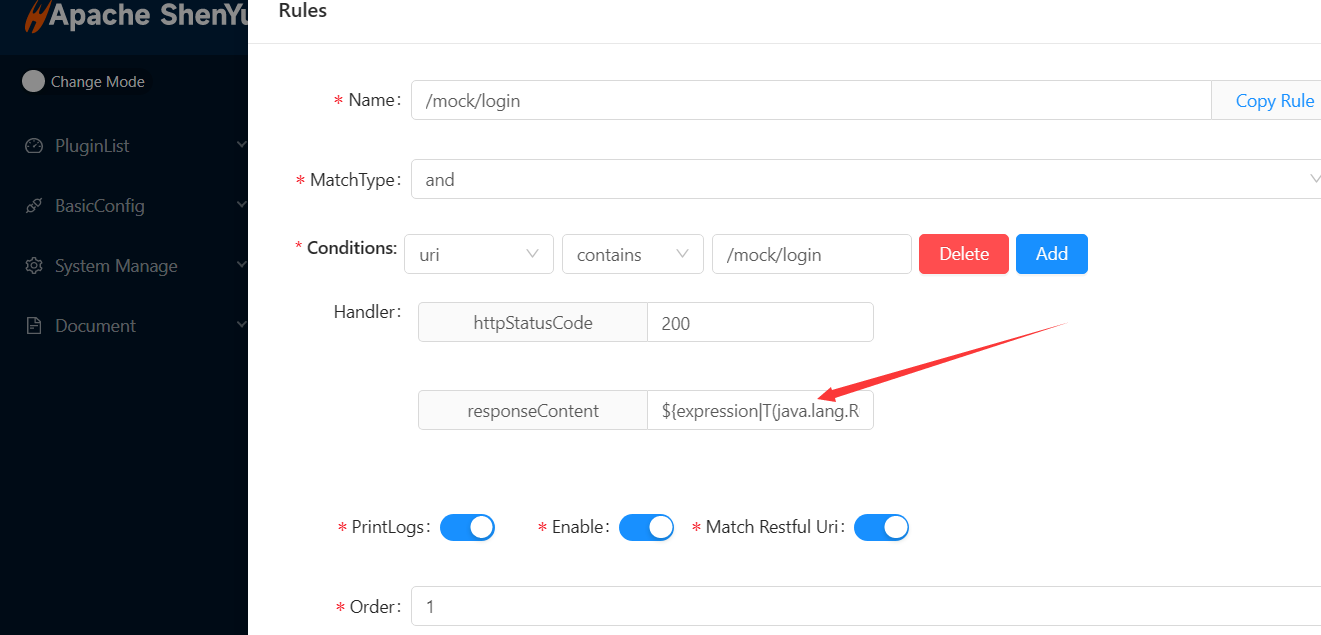 3.Click to confirm and access the corresponding URL Click the Confirm button, and after visiting the corresponding path, you can see that the calculator has successfully popped up. The same is true for Linux systems, attackers can execute arbitrary system commands in this way,It is recommended to filter here   ### Environment ```markdown ShenYu version(s):2.5.1 ``` ### Debug logs _No response_ ### Anything else? _No response_ -- This is an automated message from the Apache Git Service. To respond to the message, please log on to GitHub and use the URL above to go to the specific comment. To unsubscribe, e-mail: [email protected] For queries about this service, please contact Infrastructure at: [email protected]
