(apisix) branch master updated: feat: ai-proxy plugin (#11499)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new d46737fe7 feat: ai-proxy plugin (#11499)
d46737fe7 is described below
commit d46737fe70b6ce332146a9eb322e76997c8fa8ba
Author: Shreemaan Abhishek
AuthorDate: Tue Sep 17 10:08:58 2024 +0545
feat: ai-proxy plugin (#11499)
---
Makefile | 6 +
apisix/cli/config.lua | 1 +
apisix/core/request.lua| 16 +
apisix/plugins/ai-proxy.lua| 138 ++
apisix/plugins/ai-proxy/drivers/openai.lua | 85
apisix/plugins/ai-proxy/schema.lua | 154 +++
ci/common.sh | 21 +
ci/linux_openresty_common_runner.sh| 2 +
ci/redhat-ci.sh| 2 +
conf/config.yaml.example | 1 +
docs/en/latest/config.json | 3 +-
docs/en/latest/plugins/ai-proxy.md | 144 ++
t/admin/plugins.t | 1 +
t/assets/ai-proxy-response.json| 15 +
t/plugin/ai-proxy.t| 693 +
t/plugin/ai-proxy2.t | 200 +
t/sse_server_example/go.mod| 3 +
t/sse_server_example/main.go | 58 +++
18 files changed, 1542 insertions(+), 1 deletion(-)
diff --git a/Makefile b/Makefile
index 21a238963..545a21e4f 100644
--- a/Makefile
+++ b/Makefile
@@ -374,6 +374,12 @@ install: runtime
$(ENV_INSTALL) -d $(ENV_INST_LUADIR)/apisix/utils
$(ENV_INSTALL) apisix/utils/*.lua $(ENV_INST_LUADIR)/apisix/utils/
+ $(ENV_INSTALL) -d $(ENV_INST_LUADIR)/apisix/plugins/ai-proxy
+ $(ENV_INSTALL) apisix/plugins/ai-proxy/*.lua
$(ENV_INST_LUADIR)/apisix/plugins/ai-proxy
+
+ $(ENV_INSTALL) -d $(ENV_INST_LUADIR)/apisix/plugins/ai-proxy/drivers
+ $(ENV_INSTALL) apisix/plugins/ai-proxy/drivers/*.lua
$(ENV_INST_LUADIR)/apisix/plugins/ai-proxy/drivers
+
$(ENV_INSTALL) bin/apisix $(ENV_INST_BINDIR)/apisix
diff --git a/apisix/cli/config.lua b/apisix/cli/config.lua
index 6ab10c925..f5c5d8dca 100644
--- a/apisix/cli/config.lua
+++ b/apisix/cli/config.lua
@@ -219,6 +219,7 @@ local _M = {
"proxy-rewrite",
"workflow",
"api-breaker",
+"ai-proxy",
"limit-conn",
"limit-count",
"limit-req",
diff --git a/apisix/core/request.lua b/apisix/core/request.lua
index c5278b6b8..fef4bf17e 100644
--- a/apisix/core/request.lua
+++ b/apisix/core/request.lua
@@ -21,6 +21,7 @@
local lfs = require("lfs")
local log = require("apisix.core.log")
+local json = require("apisix.core.json")
local io = require("apisix.core.io")
local req_add_header
if ngx.config.subsystem == "http" then
@@ -334,6 +335,21 @@ function _M.get_body(max_size, ctx)
end
+function _M.get_json_request_body_table()
+local body, err = _M.get_body()
+if not body then
+return nil, { message = "could not get body: " .. (err or "request
body is empty") }
+end
+
+local body_tab, err = json.decode(body)
+if not body_tab then
+return nil, { message = "could not get parse JSON request body: " ..
err }
+end
+
+return body_tab
+end
+
+
function _M.get_scheme(ctx)
if not ctx then
ctx = ngx.ctx.api_ctx
diff --git a/apisix/plugins/ai-proxy.lua b/apisix/plugins/ai-proxy.lua
new file mode 100644
index 0..8a0d8fa97
--- /dev/null
+++ b/apisix/plugins/ai-proxy.lua
@@ -0,0 +1,138 @@
+--
+-- Licensed to the Apache Software Foundation (ASF) under one or more
+-- contributor license agreements. See the NOTICE file distributed with
+-- this work for additional information regarding copyright ownership.
+-- The ASF licenses this file to You under the Apache License, Version 2.0
+-- (the "License"); you may not use this file except in compliance with
+-- the License. You may obtain a copy of the License at
+--
+-- http://www.apache.org/licenses/LICENSE-2.0
+--
+-- Unless required by applicable law or agreed to in writing, software
+-- distributed under the License is distributed on an "AS IS" BASIS,
+-- WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+-- See the License for the specific language governing permissions and
+-- limitations under the License.
+--
+local core = require("apisix.core")
+local schema = require("apisix.plugins.ai-proxy.schema")
+local require = require
+local pcall = pcall
+local internal_server_error = ngx.HTTP_INTERNAL_SERVER_ERROR
+local bad_request = ngx.HTTP_BAD_REQUEST
+local ngx_req = ngx.req
+local ngx_print = ngx.print
+local ngx_f
(apisix) branch master updated: fix(ci): foo.com is no longer a bad gateway (#11570)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new b37ae50f7 fix(ci): foo.com is no longer a bad gateway (#11570)
b37ae50f7 is described below
commit b37ae50f7b92273e539810124d938fc0efdfe471
Author: Shreemaan Abhishek
AuthorDate: Thu Sep 12 13:19:32 2024 +0545
fix(ci): foo.com is no longer a bad gateway (#11570)
---
t/plugin/traffic-split3.t | 4 ++--
1 file changed, 2 insertions(+), 2 deletions(-)
diff --git a/t/plugin/traffic-split3.t b/t/plugin/traffic-split3.t
index e1cc7dd38..e7096094a 100644
--- a/t/plugin/traffic-split3.t
+++ b/t/plugin/traffic-split3.t
@@ -251,7 +251,7 @@ location /t {
name = "upstream_A",
type = "roundrobin",
nodes = {
-{host = "foo.com", port = 80,
weight = 0}
+{host = "test.com", port = 80,
weight = 0}
}
},
weight = 2
@@ -287,7 +287,7 @@ passed
GET /server_port
--- error_code: 502
--- error_log eval
-qr/dns resolver domain: foo.com to \d+.\d+.\d+.\d+/
+qr/dns resolver domain: test.com to \d+.\d+.\d+.\d+/
(apisix-docker) branch release/apisix-3.10.0 created (now b9d1be0)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/apisix-3.10.0 in repository https://gitbox.apache.org/repos/asf/apisix-docker.git at b9d1be0 fix: container name in release workflow (#568) No new revisions were added by this update.
(apisix-docker) branch master updated: fix: container name in release workflow (#568)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix-docker.git
The following commit(s) were added to refs/heads/master by this push:
new b9d1be0 fix: container name in release workflow (#568)
b9d1be0 is described below
commit b9d1be0e56630051360e9b6f65f989e5a79d9be3
Author: Shreemaan Abhishek
AuthorDate: Tue Sep 3 11:02:02 2024 +0545
fix: container name in release workflow (#568)
---
.github/workflows/apisix_push_docker_hub.yaml | 2 +-
1 file changed, 1 insertion(+), 1 deletion(-)
diff --git a/.github/workflows/apisix_push_docker_hub.yaml
b/.github/workflows/apisix_push_docker_hub.yaml
index dd80ff8..219ab54 100644
--- a/.github/workflows/apisix_push_docker_hub.yaml
+++ b/.github/workflows/apisix_push_docker_hub.yaml
@@ -24,7 +24,7 @@ jobs:
make build-on-${{ matrix.platform }}
docker compose -f ./compose/docker-compose-release.yaml up -d
sleep 30
- docker logs compose_apisix_1
+ docker logs compose-apisix-1
- name: Test route
run: |
(apisix-docker) branch release/apisix-3.10.0 deleted (was f048da4)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/apisix-3.10.0 in repository https://gitbox.apache.org/repos/asf/apisix-docker.git was f048da4 chore: release APISIX 3.10.0 (#565) The revisions that were on this branch are still contained in other references; therefore, this change does not discard any commits from the repository.
(apisix-docker) branch release/apisix-3.10.0 created (now f048da4)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/apisix-3.10.0 in repository https://gitbox.apache.org/repos/asf/apisix-docker.git at f048da4 chore: release APISIX 3.10.0 (#565) No new revisions were added by this update.
(apisix-docker) branch master updated: chore: release APISIX 3.10.0 (#565)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix-docker.git
The following commit(s) were added to refs/heads/master by this push:
new f048da4 chore: release APISIX 3.10.0 (#565)
f048da4 is described below
commit f048da4632d41e7f7be4a057c49605fd3c109126
Author: Shreemaan Abhishek
AuthorDate: Tue Sep 3 09:49:15 2024 +0545
chore: release APISIX 3.10.0 (#565)
---
.github/workflows/apisix-docker-example-test-standalone.yaml | 2 +-
.github/workflows/apisix-docker-example-test.yaml| 2 +-
.github/workflows/apisix_push_docker_hub.yaml| 2 +-
Makefile | 4 ++--
all-in-one/apisix-dashboard/Dockerfile | 2 +-
debian-dev/Dockerfile| 1 +
debian/Dockerfile| 2 +-
docs/en/latest/build.md | 2 +-
example/docker-compose-arm64.yml | 2 +-
example/docker-compose-standalone.yml| 2 +-
example/docker-compose.yml | 2 +-
redhat/Dockerfile| 2 +-
12 files changed, 13 insertions(+), 12 deletions(-)
diff --git a/.github/workflows/apisix-docker-example-test-standalone.yaml
b/.github/workflows/apisix-docker-example-test-standalone.yaml
index fdaae3f..0f1bae8 100644
--- a/.github/workflows/apisix-docker-example-test-standalone.yaml
+++ b/.github/workflows/apisix-docker-example-test-standalone.yaml
@@ -14,7 +14,7 @@ on:
- 'release/apisix-2.15.**'
env:
- APISIX_VERSION: "3.9.0"
+ APISIX_VERSION: "3.10.0"
jobs:
prepare:
diff --git a/.github/workflows/apisix-docker-example-test.yaml
b/.github/workflows/apisix-docker-example-test.yaml
index 10b77d9..d34d2aa 100644
--- a/.github/workflows/apisix-docker-example-test.yaml
+++ b/.github/workflows/apisix-docker-example-test.yaml
@@ -14,7 +14,7 @@ on:
- 'release/apisix-2.15.**'
env:
- APISIX_VERSION: "3.9.0"
+ APISIX_VERSION: "3.10.0"
jobs:
prepare:
diff --git a/.github/workflows/apisix_push_docker_hub.yaml
b/.github/workflows/apisix_push_docker_hub.yaml
index cc67383..dd80ff8 100644
--- a/.github/workflows/apisix_push_docker_hub.yaml
+++ b/.github/workflows/apisix_push_docker_hub.yaml
@@ -13,7 +13,7 @@ jobs:
- debian
- redhat
env:
- APISIX_DOCKER_TAG: 3.9.0-${{ matrix.platform }}
+ APISIX_DOCKER_TAG: 3.10.0-${{ matrix.platform }}
steps:
- name: Check out the repo
diff --git a/Makefile b/Makefile
index 0fd06a7..9369ba1 100644
--- a/Makefile
+++ b/Makefile
@@ -21,8 +21,8 @@ SHELL := bash
# APISIX ARGS
-APISIX_VERSION ?= 3.9.0
-MAX_APISIX_VERSION ?= 3.9.0
+APISIX_VERSION ?= 3.10.0
+MAX_APISIX_VERSION ?= 3.10.0
IMAGE_NAME = apache/apisix
IMAGE_TAR_NAME = apache_apisix
APISIX_REPO = https://github.com/apache/apisix
diff --git a/all-in-one/apisix-dashboard/Dockerfile
b/all-in-one/apisix-dashboard/Dockerfile
index 0699ee9..1d7d121 100644
--- a/all-in-one/apisix-dashboard/Dockerfile
+++ b/all-in-one/apisix-dashboard/Dockerfile
@@ -21,7 +21,7 @@ ARG APISIX_VERSION=master
ARG APISIX_DASHBOARD_VERSION=master
# Build Apache APISIX
-FROM openresty/openresty:1.25.3.1-2-alpine-fat AS production-stage
+FROM openresty/openresty:1.25.3.2-0-alpine-fat AS production-stage
ARG APISIX_VERSION
ARG ENABLE_PROXY
diff --git a/debian-dev/Dockerfile b/debian-dev/Dockerfile
index 5cd9c3f..39aec91 100644
--- a/debian-dev/Dockerfile
+++ b/debian-dev/Dockerfile
@@ -34,6 +34,7 @@ RUN set -x \
sudo \
unzip \
wget \
+libyaml-dev \
&& curl
https://raw.githubusercontent.com/apache/apisix/master/utils/linux-install-luarocks.sh
-sL | bash - \
&& luarocks install
https://raw.githubusercontent.com/apache/apisix/master/apisix-master-0.rockspec
--tree=/usr/local/apisix/deps PCRE_DIR=/usr/local/openresty/pcre \
&& cp -v
/usr/local/apisix/deps/lib/luarocks/rocks-5.1/apisix/master-0/bin/apisix
/usr/bin/ \
diff --git a/debian/Dockerfile b/debian/Dockerfile
index c380951..eca89c5 100644
--- a/debian/Dockerfile
+++ b/debian/Dockerfile
@@ -17,7 +17,7 @@
FROM debian:bullseye-slim
-ARG APISIX_VERSION=3.9.0
+ARG APISIX_VERSION=3.10.0
RUN set -ex; \
arch=$(dpkg --print-architecture); \
diff --git a/docs/en/latest/build.md b/docs/en/latest/build.md
index fe0fdf7..3538fea 100644
--- a/docs/en/latest/build.md
+++ b/docs/en/latest/build.md
@@ -43,7 +43,7 @@ Find an APISIX [release
version](https://github.com/apache/apisix/releases) to b
Build a Docker image from the release:
```shell
-APISIX_VERSION=3.9.0# specify release version
+APISIX_VERSION=3.10.0 # specify release version
DISTRO=debia
(apisix) branch master updated: feat: ai-prompt-decorator plugin (#11515)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 338791683 feat: ai-prompt-decorator plugin (#11515)
338791683 is described below
commit 33879168349b08ba70f5097629840dba181e1def
Author: Shreemaan Abhishek
AuthorDate: Fri Aug 30 09:24:15 2024 +0545
feat: ai-prompt-decorator plugin (#11515)
---
apisix/cli/config.lua | 1 +
apisix/plugins/ai-prompt-decorator.lua| 117 ++
apisix/plugins/ai-prompt-template.lua | 2 +-
conf/config.yaml.example | 3 +-
docs/en/latest/config.json| 1 +
docs/en/latest/plugins/ai-prompt-decorator.md | 109 ++
t/admin/plugins.t | 1 +
t/plugin/ai-prompt-decorator.t| 293 ++
8 files changed, 525 insertions(+), 2 deletions(-)
diff --git a/apisix/cli/config.lua b/apisix/cli/config.lua
index 7f15542b1..6ab10c925 100644
--- a/apisix/cli/config.lua
+++ b/apisix/cli/config.lua
@@ -214,6 +214,7 @@ local _M = {
"proxy-cache",
"body-transformer",
"ai-prompt-template",
+"ai-prompt-decorator",
"proxy-mirror",
"proxy-rewrite",
"workflow",
diff --git a/apisix/plugins/ai-prompt-decorator.lua
b/apisix/plugins/ai-prompt-decorator.lua
new file mode 100644
index 0..10b36e82c
--- /dev/null
+++ b/apisix/plugins/ai-prompt-decorator.lua
@@ -0,0 +1,117 @@
+--
+-- Licensed to the Apache Software Foundation (ASF) under one or more
+-- contributor license agreements. See the NOTICE file distributed with
+-- this work for additional information regarding copyright ownership.
+-- The ASF licenses this file to You under the Apache License, Version 2.0
+-- (the "License"); you may not use this file except in compliance with
+-- the License. You may obtain a copy of the License at
+--
+-- http://www.apache.org/licenses/LICENSE-2.0
+--
+-- Unless required by applicable law or agreed to in writing, software
+-- distributed under the License is distributed on an "AS IS" BASIS,
+-- WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+-- See the License for the specific language governing permissions and
+-- limitations under the License.
+--
+local core = require("apisix.core")
+local ngx = ngx
+local pairs = pairs
+local EMPTY = {}
+
+local prompt_schema = {
+properties = {
+role = {
+type = "string",
+enum = { "system", "user", "assistant" }
+},
+content = {
+type = "string",
+minLength = 1,
+}
+},
+required = { "role", "content" }
+}
+
+local prompts = {
+type = "array",
+items = prompt_schema
+}
+
+local schema = {
+type = "object",
+properties = {
+prepend = prompts,
+append = prompts,
+},
+anyOf = {
+{ required = { "prepend" } },
+{ required = { "append" } },
+{ required = { "append", "prepend" } },
+},
+}
+
+
+local _M = {
+version = 0.1,
+priority = 1070,
+name = "ai-prompt-decorator",
+schema = schema,
+}
+
+
+function _M.check_schema(conf)
+return core.schema.check(schema, conf)
+end
+
+
+local function get_request_body_table()
+local body, err = core.request.get_body()
+if not body then
+return nil, { message = "could not get body: " .. err }
+end
+
+local body_tab, err = core.json.decode(body)
+if not body_tab then
+return nil, { message = "could not get parse JSON request body: " ..
err }
+end
+
+return body_tab
+end
+
+
+local function decorate(conf, body_tab)
+local new_messages = conf.prepend or EMPTY
+for _, message in pairs(body_tab.messages) do
+core.table.insert_tail(new_messages, message)
+end
+
+for _, message in pairs(conf.append or EMPTY) do
+core.table.insert_tail(new_messages, message)
+end
+
+body_tab.messages = new_messages
+end
+
+
+function _M.rewrite(conf, ctx)
+local body_tab, err = get_request_body_table()
+if not body_tab then
+return 400, err
+end
+
+if not body_tab.messages then
+return 400, "messages missing from request body"
+end
+decorate(conf, body_tab) -- will decorate body_tab in place
+
+local new_jbody, err = core.json.encode(body_tab)
+if not new_jbody then
+return 500, { message = "failed to parse modified JSON request body: "
.. err }
+end
+
+ngx.req.set_body_data(new_jbody)
+end
+
+
+return _M
diff
(apisix) branch master updated: feat: ai-prompt-template plugin (#11517)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new e775640f7 feat: ai-prompt-template plugin (#11517)
e775640f7 is described below
commit e775640f79923b4480283a3aea6486c3208dff82
Author: Shreemaan Abhishek
AuthorDate: Thu Aug 29 13:28:53 2024 +0545
feat: ai-prompt-template plugin (#11517)
---
apisix/cli/config.lua| 1 +
apisix/plugins/ai-prompt-template.lua| 146 ++
conf/config.yaml.example | 1 +
docs/en/latest/config.json | 1 +
docs/en/latest/plugins/ai-prompt-template.md | 102 +++
t/admin/plugins.t| 1 +
t/plugin/ai-prompt-template.t| 403 +++
7 files changed, 655 insertions(+)
diff --git a/apisix/cli/config.lua b/apisix/cli/config.lua
index 94843621a..7f15542b1 100644
--- a/apisix/cli/config.lua
+++ b/apisix/cli/config.lua
@@ -213,6 +213,7 @@ local _M = {
"authz-keycloak",
"proxy-cache",
"body-transformer",
+"ai-prompt-template",
"proxy-mirror",
"proxy-rewrite",
"workflow",
diff --git a/apisix/plugins/ai-prompt-template.lua
b/apisix/plugins/ai-prompt-template.lua
new file mode 100644
index 0..0a092c3f7
--- /dev/null
+++ b/apisix/plugins/ai-prompt-template.lua
@@ -0,0 +1,146 @@
+--
+-- Licensed to the Apache Software Foundation (ASF) under one or more
+-- contributor license agreements. See the NOTICE file distributed with
+-- this work for additional information regarding copyright ownership.
+-- The ASF licenses this file to You under the Apache License, Version 2.0
+-- (the "License"); you may not use this file except in compliance with
+-- the License. You may obtain a copy of the License at
+--
+-- http://www.apache.org/licenses/LICENSE-2.0
+--
+-- Unless required by applicable law or agreed to in writing, software
+-- distributed under the License is distributed on an "AS IS" BASIS,
+-- WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+-- See the License for the specific language governing permissions and
+-- limitations under the License.
+--
+local core = require("apisix.core")
+local body_transformer = require("apisix.plugins.body-transformer")
+local ipairs= ipairs
+
+local prompt_schema = {
+properties = {
+role = {
+type = "string",
+enum = { "system", "user", "assistant" }
+},
+content = {
+type = "string",
+minLength = 1,
+}
+},
+required = { "role", "content" }
+}
+
+local prompts = {
+type = "array",
+minItems = 1,
+items = prompt_schema
+}
+
+local schema = {
+type = "object",
+properties = {
+templates = {
+type = "array",
+minItems = 1,
+items = {
+type = "object",
+properties = {
+name = {
+type = "string",
+minLength = 1,
+},
+template = {
+type = "object",
+properties = {
+model = {
+type = "string",
+minLength = 1,
+},
+messages = prompts
+}
+}
+},
+required = {"name", "template"}
+}
+},
+},
+required = {"templates"},
+}
+
+
+local _M = {
+version = 0.1,
+priority = 1060,
+name = "ai-prompt-template",
+schema = schema,
+}
+
+local templates_lrucache = core.lrucache.new({
+ttl = 300, count = 256
+})
+
+local templates_json_lrucache = core.lrucache.new({
+ttl = 300, count = 256
+})
+
+function _M.check_schema(conf)
+return core.schema.check(schema, conf)
+end
+
+
+local function get_request_body_table()
+local body, err = core.request.get_body()
+if not body then
+return nil, { message = "could not get body: " .. err }
+end
+
+local body_tab, err = core.json.decode(body)
+if not body_tab then
+return nil, { message = "could not get parse JSON request body: ", err
}
+end
+
+return body_tab
+end
+
+
+local function find_template(conf, template_name)
+for _, template in ipairs(conf.templates) do
+if template.name == template_name th
(apisix-docker) branch master updated: fix: remove empty apisix folder (#563)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix-docker.git The following commit(s) were added to refs/heads/master by this push: new a62dcd2 fix: remove empty apisix folder (#563) a62dcd2 is described below commit a62dcd241203654257037bd37bac3bd124d5933a Author: Shubhendra Kushwaha AuthorDate: Mon Aug 19 11:31:19 2024 +0530 fix: remove empty apisix folder (#563) --- apisix | 1 - 1 file changed, 1 deletion(-) diff --git a/apisix b/apisix deleted file mode 16 index e746746..000 --- a/apisix +++ /dev/null @@ -1 +0,0 @@ -Subproject commit e74674649fde29cc59ae70be1f8a6f2266b3ba40
(apisix-website) branch master updated: docs: release APISIX 3.10.0 (#1818)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix-website.git
The following commit(s) were added to refs/heads/master by this push:
new 36e458f09b1 docs: release APISIX 3.10.0 (#1818)
36e458f09b1 is described below
commit 36e458f09b1f0a89a30b7cbee74c216b54ebbb2e
Author: Shreemaan Abhishek
AuthorDate: Thu Aug 15 08:41:38 2024 +0545
docs: release APISIX 3.10.0 (#1818)
---
config/apisix-versions.js | 2 +-
config/docs.js| 4 ++--
config/downloads.js | 6 +++---
3 files changed, 6 insertions(+), 6 deletions(-)
diff --git a/config/apisix-versions.js b/config/apisix-versions.js
index a757d157c0e..4bb8785e6fe 100644
--- a/config/apisix-versions.js
+++ b/config/apisix-versions.js
@@ -3,7 +3,7 @@
/**
* @type {Array} version list
*/
-const versions = ['2.13', '2.14', '2.15', '3.0', '3.1', '3.2', '3.3', '3.4',
'3.5', '3.6', '3.7', '3.8', '3.9'];
+const versions = ['2.13', '2.14', '2.15', '3.0', '3.1', '3.2', '3.3', '3.4',
'3.5', '3.6', '3.7', '3.8', '3.9', '3.10'];
/**
* @type {Array} LTS version list
diff --git a/config/docs.js b/config/docs.js
index 82dbf261a49..e75609550a6 100644
--- a/config/docs.js
+++ b/config/docs.js
@@ -6,8 +6,8 @@ module.exports = [
shape: 'triangle',
color: '#e8433e',
githubRepo: 'apache/apisix',
-version: '3.9.1',
-releaseDate: '2024-04-29',
+version: '3.10.0',
+releaseDate: '2024-08-14',
firstDocPath: '/getting-started',
},
{
diff --git a/config/downloads.js b/config/downloads.js
index b16861c8881..0d928e4d038 100644
--- a/config/downloads.js
+++ b/config/downloads.js
@@ -7,12 +7,12 @@ module.exports = [
color: '#e8433e',
githubRepo: 'apache/apisix',
githubBranch: 'master',
-downloadPath: 'apisix/3.9.1/apache-apisix-3.9.1-src',
+downloadPath: 'apisix/3.10.0/apache-apisix-3.10.0-src',
dockerhubPath: 'apisix',
-version: '3.9.1',
+version: '3.10.0',
LTSDownloadPath: 'apisix/3.2.2/apache-apisix-3.2.2-src',
LTSVersion: '3.2.2',
-releaseDate: '2024-04-29',
+releaseDate: '2024-08-14',
firstDocPath: '/getting-started',
},
{
(apisix) tag 3.10.0 created (now 45aa74718)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to tag 3.10.0 in repository https://gitbox.apache.org/repos/asf/apisix.git at 45aa74718 (commit) No new revisions were added by this update.
(apisix) branch release/3.10 deleted (was 45aa74718)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/3.10 in repository https://gitbox.apache.org/repos/asf/apisix.git was 45aa74718 add # The revisions that were on this branch are still contained in other references; therefore, this change does not discard any commits from the repository.
(apisix) branch master updated: chore: release 3.10.0 (#11472)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new a6b0d0076 chore: release 3.10.0 (#11472) a6b0d0076 is described below commit a6b0d0076f10ed1d5006e179c2283d4048c18256 Author: Shreemaan Abhishek AuthorDate: Wed Aug 14 11:58:28 2024 +0545 chore: release 3.10.0 (#11472) --- .asf.yaml | 4 +++ CHANGELOG.md | 53 +++ apisix/core/version.lua | 2 +- docs/en/latest/building-apisix.md | 2 +- docs/en/latest/config.json| 2 +- docs/zh/latest/building-apisix.md | 2 +- docs/zh/latest/config.json| 2 +- 7 files changed, 62 insertions(+), 5 deletions(-) diff --git a/.asf.yaml b/.asf.yaml index ef0571a9a..5d657124b 100644 --- a/.asf.yaml +++ b/.asf.yaml @@ -53,6 +53,10 @@ github: dismiss_stale_reviews: true require_code_owner_reviews: true required_approving_review_count: 3 + release/3.10: +required_pull_request_reviews: + require_code_owner_reviews: true + required_approving_review_count: 3 release/3.9: required_pull_request_reviews: require_code_owner_reviews: true diff --git a/CHANGELOG.md b/CHANGELOG.md index 62e13fb88..b173ca6ef 100644 --- a/CHANGELOG.md +++ b/CHANGELOG.md @@ -23,6 +23,7 @@ title: Changelog ## Table of Contents +- [3.10.0](#3100) - [3.9.0](#390) - [3.8.0](#380) - [3.7.0](#370) @@ -76,6 +77,58 @@ title: Changelog - [0.7.0](#070) - [0.6.0](#060) +## 3.10.0 + +### Change + +- remove `core.grpc` module [#11427](https://github.com/apache/apisix/pull/11427) +- add max req/resp body size attributes [#11133](https://github.com/apache/apisix/pull/11133) +- autogenerate admin api key if not passed [#11080](https://github.com/apache/apisix/pull/11080) +- enable sensitive fields encryption by default [#11076](https://github.com/apache/apisix/pull/11076) +- support more sensitive fields for encryption [#11095](https://github.com/apache/apisix/pull/11095) + +### Plugins + +- allow set headers in introspection request [#11090](https://github.com/apache/apisix/pull/11090) + +### Bugfixes + +- Fix: etcd sync data checker should work [#11457](https://github.com/apache/apisix/pull/11457) +- Fix: plugin metadata add id value for etcd checker [#11452](https://github.com/apache/apisix/pull/11452) +- Fix: allow trailing period in SNI and CN for SSL [#11414](https://github.com/apache/apisix/pull/11414) +- Fix: filter out illegal INT(string) formats [#11367](https://github.com/apache/apisix/pull/11367) +- Fix: make the message clearer when API key is missing [#11370](https://github.com/apache/apisix/pull/11370) +- Fix: report consumer username tag in datadog [#11354](https://github.com/apache/apisix/pull/11354) +- Fix: after updating the header, get the old value from the ctx.var [#11329](https://github.com/apache/apisix/pull/11329) +- Fix: ssl key rotation caused request failure [#11305](https://github.com/apache/apisix/pull/11305) +- Fix: validation fails causing etcd events not to be handled correctly [#11268](https://github.com/apache/apisix/pull/11268) +- Fix: stream route matcher is nil after first match [#11269](https://github.com/apache/apisix/pull/11269) +- Fix: rectify the way to fetch secret resource by id [#11164](https://github.com/apache/apisix/pull/11164) +- Fix: multi-auth raise 500 error when use default conf [#11145](https://github.com/apache/apisix/pull/11145) +- Fix: avoid overwriting `Access-Control-Expose-Headers` response header [#11136](https://github.com/apache/apisix/pull/11136) +- Fix: close session in case of error to avoid blocked session [#11089](https://github.com/apache/apisix/pull/11089) +- Fix: restore `pb.state` appropriately [#11135](https://github.com/apache/apisix/pull/11135) +- Fix: add a default limit of 100 for `get_headers()` [#11140](https://github.com/apache/apisix/pull/11140) +- Fix: disable features when prometheus plugin is turned off [#7](https://github.com/apache/apisix/pull/7) +- Fix: add post request headers only if auth request method is POST [#11021](https://github.com/apache/apisix/pull/11021) +- Fix: core.request.header return strings instead of table [#11127](https://github.com/apache/apisix/pull/11127) +- Fix: brotli partial response [#11087](https://github.com/apache/apisix/pull/11087) +- Fix: the port value greater than 65535 should not be allowed [#11043](https://github.com/apache/apisix/pull/11043) + +### Core + +- upgrade openresty version to 1.25.3.2 [#11419](https://github.com/apache/apisix/pull/11419) +- move config-default.yaml to hardcoded lua file [#11343](https://github.com/apache/apisix/pull/11343) +- warn log when sending requests to external services insecurely [#11403](https
(apisix) branch release/3.10 created (now 45aa74718)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/3.10 in repository https://gitbox.apache.org/repos/asf/apisix.git at 45aa74718 add # No new revisions were added by this update.
(apisix-docker) branch master updated: ci: include libyaml in image and use docker compose (#562)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix-docker.git
The following commit(s) were added to refs/heads/master by this push:
new 2993386 ci: include libyaml in image and use docker compose (#562)
2993386 is described below
commit 29933866930ab01e3b0b2a2c484b7bca22a0b225
Author: Shubhendra Kushwaha
AuthorDate: Wed Aug 14 10:05:59 2024 +0530
ci: include libyaml in image and use docker compose (#562)
---
.github/workflows/apisix-docker-example-test-standalone.yaml | 2 +-
.github/workflows/apisix-docker-example-test.yaml| 2 +-
.github/workflows/apisix_dev_docker_local_test.yaml | 4 ++--
.github/workflows/apisix_dev_push_docker_hub.yaml| 2 +-
.github/workflows/apisix_push_docker_hub.yaml| 2 +-
.github/workflows/dashboard_push_docker_hub.yaml | 2 +-
all-in-one/apisix-dashboard/Dockerfile | 12 +++-
apisix | 1 +
debian-dev/Dockerfile.local | 2 ++
9 files changed, 21 insertions(+), 8 deletions(-)
diff --git a/.github/workflows/apisix-docker-example-test-standalone.yaml
b/.github/workflows/apisix-docker-example-test-standalone.yaml
index 140c102..fdaae3f 100644
--- a/.github/workflows/apisix-docker-example-test-standalone.yaml
+++ b/.github/workflows/apisix-docker-example-test-standalone.yaml
@@ -55,7 +55,7 @@ jobs:
env:
APISIX_IMAGE_TAG: ${{ format('{0}-{1}', env.APISIX_VERSION,
matrix.platform) }}
APISIX_STAND_ALONE: true
-run: docker-compose -p docker-apisix -f
example/docker-compose-standalone.yml up -d
+run: docker compose -p docker-apisix -f
example/docker-compose-standalone.yml up -d
- name: Test APISIX
run: |
diff --git a/.github/workflows/apisix-docker-example-test.yaml
b/.github/workflows/apisix-docker-example-test.yaml
index 3f11473..10b77d9 100644
--- a/.github/workflows/apisix-docker-example-test.yaml
+++ b/.github/workflows/apisix-docker-example-test.yaml
@@ -54,7 +54,7 @@ jobs:
- name: use docker-compose
env:
APISIX_IMAGE_TAG: ${{ format('{0}-{1}', env.APISIX_VERSION,
matrix.platform) }}
-run: docker-compose -p docker-apisix -f example/docker-compose.yml up
-d
+run: docker compose -p docker-apisix -f example/docker-compose.yml up
-d
- name: Test APISIX
run: |
diff --git a/.github/workflows/apisix_dev_docker_local_test.yaml
b/.github/workflows/apisix_dev_docker_local_test.yaml
index ca8f58d..1af6818 100644
--- a/.github/workflows/apisix_dev_docker_local_test.yaml
+++ b/.github/workflows/apisix_dev_docker_local_test.yaml
@@ -42,12 +42,12 @@ jobs:
make build-on-debian-local-dev
- name: use docker-compose
-run: docker-compose -p docker-apisix -f example/docker-compose.yml up
-d
+run: docker compose -p docker-apisix -f example/docker-compose.yml up
-d
- name: Test APISIX
run: |
sleep 2
- docker logs docker-apisix_apisix_1
+ docker logs docker-apisix-apisix-1
sleep 30
diff --git a/.github/workflows/apisix_dev_push_docker_hub.yaml
b/.github/workflows/apisix_dev_push_docker_hub.yaml
index 82fe243..ca1b777 100644
--- a/.github/workflows/apisix_dev_push_docker_hub.yaml
+++ b/.github/workflows/apisix_dev_push_docker_hub.yaml
@@ -26,7 +26,7 @@ jobs:
- name: Build and run
run: |
make build-on-debian-dev
- docker-compose -f ./compose/docker-compose-master.yaml up -d
+ docker compose -f ./compose/docker-compose-master.yaml up -d
sleep 30
docker logs compose_apisix_1
diff --git a/.github/workflows/apisix_push_docker_hub.yaml
b/.github/workflows/apisix_push_docker_hub.yaml
index f0f05a3..cc67383 100644
--- a/.github/workflows/apisix_push_docker_hub.yaml
+++ b/.github/workflows/apisix_push_docker_hub.yaml
@@ -22,7 +22,7 @@ jobs:
- name: Build and run
run: |
make build-on-${{ matrix.platform }}
- docker-compose -f ./compose/docker-compose-release.yaml up -d
+ docker compose -f ./compose/docker-compose-release.yaml up -d
sleep 30
docker logs compose_apisix_1
diff --git a/.github/workflows/dashboard_push_docker_hub.yaml
b/.github/workflows/dashboard_push_docker_hub.yaml
index e1b9296..db680ca 100644
--- a/.github/workflows/dashboard_push_docker_hub.yaml
+++ b/.github/workflows/dashboard_push_docker_hub.yaml
@@ -23,7 +23,7 @@ jobs:
- name: Build and run
run: |
make build-dashboard-${{ matrix.os }}
- docker-compose -f ./compose/dashboard-compose.yaml up -d
+ docker compose -f ./compose/dashboard-compose.yaml up -d
sleep 30
(apisix) branch release/3.10 updated (35a9a9f0b -> 45aa74718)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/3.10 in repository https://gitbox.apache.org/repos/asf/apisix.git from 35a9a9f0b remove trailing hyphens add 8cb082c59 fix changes add 45aa74718 add # No new revisions were added by this update. Summary of changes: CHANGELOG.md | 78 ++-- 1 file changed, 39 insertions(+), 39 deletions(-)
(apisix) branch release/3.10 updated (0cecbcbf6 -> 35a9a9f0b)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/3.10 in repository https://gitbox.apache.org/repos/asf/apisix.git from 0cecbcbf6 asf add 35a9a9f0b remove trailing hyphens No new revisions were added by this update. Summary of changes: CHANGELOG.md | 2 +- 1 file changed, 1 insertion(+), 1 deletion(-)
(apisix) branch release/3.10 updated (0e7adb59d -> 0cecbcbf6)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/3.10 in repository https://gitbox.apache.org/repos/asf/apisix.git from 0e7adb59d chore: release 3.10.0 add 0cecbcbf6 asf No new revisions were added by this update. Summary of changes: .asf.yaml | 4 1 file changed, 4 insertions(+)
(apisix) branch release/3.10 updated: chore: release 3.10.0
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch release/3.10 in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/release/3.10 by this push: new 0e7adb59d chore: release 3.10.0 0e7adb59d is described below commit 0e7adb59d69640724eeb9a6d11f24955c5b2de0d Author: Abhishek Choudhary AuthorDate: Mon Aug 5 10:55:31 2024 +0545 chore: release 3.10.0 --- CHANGELOG.md | 53 +++ apisix/core/version.lua | 2 +- docs/en/latest/building-apisix.md | 2 +- docs/en/latest/config.json| 2 +- docs/zh/latest/building-apisix.md | 2 +- docs/zh/latest/config.json| 2 +- 6 files changed, 58 insertions(+), 5 deletions(-) diff --git a/CHANGELOG.md b/CHANGELOG.md index 62e13fb88..9bd10bd43 100644 --- a/CHANGELOG.md +++ b/CHANGELOG.md @@ -23,6 +23,7 @@ title: Changelog ## Table of Contents +- [3.10.0] (#3100) - [3.9.0](#390) - [3.8.0](#380) - [3.7.0](#370) @@ -76,6 +77,58 @@ title: Changelog - [0.7.0](#070) - [0.6.0](#060) +## 3.10.0 + +### Change + +- remove `core.grpc` module [11427](https://github.com/apache/apisix/pull/11427) +- add max req/resp body size attributes [11133](https://github.com/apache/apisix/pull/11133) + +### Plugins + +- allow set headers in introspection request [11090](https://github.com/apache/apisix/pull/11090)-- + +### Bugfixes + +- Fix: etcd sync data checker should work [11457](https://github.com/apache/apisix/pull/11457) +- Fix: plugin metadata add id value for etcd checker [11452](https://github.com/apache/apisix/pull/11452) +- Fix: allow trailing period in SNI and CN for SSL [11414](https://github.com/apache/apisix/pull/11414) +- Fix: filter out illegal INT(string) formats [11367](https://github.com/apache/apisix/pull/11367) +- Fix: make the message clearer when API key is missing [11370](https://github.com/apache/apisix/pull/11370) +- Fix: report consumer username tag in datadog [11354](https://github.com/apache/apisix/pull/11354) +- Fix: after updating the header, get the old value from the ctx.var [11329](https://github.com/apache/apisix/pull/11329) +- Fix: ssl key rotation caused request failure [11305](https://github.com/apache/apisix/pull/11305) +- Fix: validation fails causing etcd events not to be handled correctly [11268](https://github.com/apache/apisix/pull/11268) +- Fix: stream route matcher is nil after first match [11269](https://github.com/apache/apisix/pull/11269) +- Fix: rectify the way to fetch secret resource by id [11164](https://github.com/apache/apisix/pull/11164) +- Fix: multi-auth raise 500 error when use default conf [11145](https://github.com/apache/apisix/pull/11145) +- Fix: avoid overwriting `Access-Control-Expose-Headers` response header [11136](https://github.com/apache/apisix/pull/11136) +- Fix: close session in case of error to avoid blocked session [11089](https://github.com/apache/apisix/pull/11089) +- Fix: restore `pb.state` appropriately [11135](https://github.com/apache/apisix/pull/11135) +- Fix: add a default limit of 100 for `get_headers()` [11140](https://github.com/apache/apisix/pull/11140) +- Fix: disable features when prometheus plugin is turned off [7](https://github.com/apache/apisix/pull/7) +- Fix: add post request headers only if auth request method is POST [11021](https://github.com/apache/apisix/pull/11021) +- Fix: core.request.header return strings instead of table [11127](https://github.com/apache/apisix/pull/11127) +- Fix: brotli partial response [11087](https://github.com/apache/apisix/pull/11087) +- Fix: the port value greater than 65535 should not be allowed [11043](https://github.com/apache/apisix/pull/11043) + +### Core + +- upgrade openresty version to 1.25.3.2 [11419](https://github.com/apache/apisix/pull/11419) +- move config-default.yaml to hardcoded lua file [11343](https://github.com/apache/apisix/pull/11343) +- warn log when sending requests to external services insecurely [11403](https://github.com/apache/apisix/pull/11403) +- update casbin to 1.41.9 [11400](https://github.com/apache/apisix/pull/11400) +- update lua-resty-t1k to 1.1.5 [11391](https://github.com/apache/apisix/pull/11391) +- support store ssl.keys ssl.certs in secrets mamager [11339](https://github.com/apache/apisix/pull/11339) +- move tinyyaml to lyaml [11312](https://github.com/apache/apisix/pull/11312) +- support hcv namespace [11277](https://github.com/apache/apisix/pull/11277) +- add discovery k8s dump data interface [1](https://github.com/apache/apisix/pull/1) +- autogenerate admin api key if not passed [11080](https://github.com/apache/apisix/pull/11080) +- support more sensitive fields for encryption [11095](https://github.com/apache/apisix/pull/11095) +- enable sensitive fields encryption by default [11076](https://github.com/apache/apisix/pull/11076) +- make
(apisix) branch release/3.10 created (now 060372674)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/3.10 in repository https://gitbox.apache.org/repos/asf/apisix.git at 060372674 docs: correct the `status_on_error` data type in the zh `forward-auth` plugin doc (#11470) No new revisions were added by this update.
(apisix) branch release3.9.2 deleted (was e34e5cf3f)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release3.9.2 in repository https://gitbox.apache.org/repos/asf/apisix.git was e34e5cf3f Merge branch 'master' of github.com:apache/apisix into release3.9.2 The revisions that were on this branch are still contained in other references; therefore, this change does not discard any commits from the repository.
(apisix) branch revert-11171-dependabot/go_modules/ci/pod/openfunction/function-example/test-uri/golang.org/x/net-0.23.0 deleted (was 63bc0d3dc)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch revert-11171-dependabot/go_modules/ci/pod/openfunction/function-example/test-uri/golang.org/x/net-0.23.0 in repository https://gitbox.apache.org/repos/asf/apisix.git was 63bc0d3dc Revert "chore(deps): bump golang.org/x/net (#11169)" The revisions that were on this branch are still contained in other references; therefore, this change does not discard any commits from the repository.
(apisix-helm-chart) branch dev updated: feat: override nginx http lua shared dict configurations (#690)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch dev
in repository https://gitbox.apache.org/repos/asf/apisix-helm-chart.git
The following commit(s) were added to refs/heads/dev by this push:
new 9660fe3 feat: override nginx http lua shared dict configurations
(#690)
9660fe3 is described below
commit 9660fe35cc5fd662c708df934909006d62254b9b
Author: Junyeong Jang
AuthorDate: Sun Aug 4 17:13:22 2024 +0900
feat: override nginx http lua shared dict configurations (#690)
---
charts/apisix/README.md| 3 ++-
charts/apisix/templates/configmap.yaml | 3 +++
charts/apisix/values.yaml | 7 ++-
3 files changed, 11 insertions(+), 2 deletions(-)
diff --git a/charts/apisix/README.md b/charts/apisix/README.md
index f39508d..17d2a9e 100644
--- a/charts/apisix/README.md
+++ b/charts/apisix/README.md
@@ -89,7 +89,7 @@ The command removes all the Kubernetes components associated
with the chart and
| apisix.luaModuleHook.hookPoint | string | `""` | the hook module which will
be used to inject third party code into APISIX use the lua require style like:
"module.say_hello" |
| apisix.luaModuleHook.luaPath | string | `""` | extend lua_package_path to
load third party code |
| apisix.nginx.configurationSnippet | object |
`{"httpAdmin":"","httpEnd":"","httpSrv":"","httpStart":"","main":"","stream":""}`
| Custom configuration snippet. |
-| apisix.nginx.customLuaSharedDicts | list | `[]` | Add custom
[lua_shared_dict](https://github.com/openresty/lua-nginx-module#toc88)
settings, click
[here](https://github.com/apache/apisix-helm-chart/blob/master/charts/apisix/values.yaml#L27-L30)
to learn the format of a shared dict |
+| apisix.nginx.customLuaSharedDicts | list | `[]` | Add custom
[lua_shared_dict](https://github.com/openresty/lua-nginx-module#toc88)
settings, click
[here](https://github.com/apache/apisix-helm-chart/blob/master/charts/apisix/values.yaml#L48-L51)
to learn the format of a shared dict |
| apisix.nginx.enableCPUAffinity | bool | `true` | |
| apisix.nginx.envs | list | `[]` | |
| apisix.nginx.keepaliveTimeout | string | `"60s"` | Timeout during which a
keep-alive client connection will stay open on the server side. |
@@ -99,6 +99,7 @@ The command removes all the Kubernetes components associated
with the chart and
| apisix.nginx.logs.enableAccessLog | bool | `true` | Enable access log or
not, default true |
| apisix.nginx.logs.errorLog | string | `"/dev/stderr"` | Error log path |
| apisix.nginx.logs.errorLogLevel | string | `"warn"` | Error log level |
+| apisix.nginx.luaSharedDictsOverride | object | `{}` | Overrides
[lua_shared_dict](https://github.com/openresty/lua-nginx-module#toc88)
settings, click
[here](https://github.com/apache/apisix/blob/master/conf/config-default.yaml#L258)
to view the default values. |
| apisix.nginx.workerConnections | string | `"10620"` | |
| apisix.nginx.workerProcesses | string | `"auto"` | |
| apisix.nginx.workerRlimitNofile | string | `"20480"` | |
diff --git a/charts/apisix/templates/configmap.yaml
b/charts/apisix/templates/configmap.yaml
index e3917c6..2864e5b 100644
--- a/charts/apisix/templates/configmap.yaml
+++ b/charts/apisix/templates/configmap.yaml
@@ -198,6 +198,9 @@ data:
{{ $dict.name }}: {{ $dict.size }}
{{- end }}
{{- end }}
+{{- if .Values.apisix.nginx.luaSharedDictsOverride }}
+lua_shared_dict: {{- toYaml
.Values.apisix.nginx.luaSharedDictsOverride | nindent 10 }}
+{{- end }}
{{- if .Values.apisix.nginx.configurationSnippet.main }}
main_configuration_snippet: {{- toYaml
.Values.apisix.nginx.configurationSnippet.main | indent 6 }}
{{- end }}
diff --git a/charts/apisix/values.yaml b/charts/apisix/values.yaml
index 6c7cd9c..a3aea93 100644
--- a/charts/apisix/values.yaml
+++ b/charts/apisix/values.yaml
@@ -392,13 +392,18 @@ apisix:
stream: |
# -- Add custom
[lua_shared_dict](https://github.com/openresty/lua-nginx-module#toc88) settings,
-# click
[here](https://github.com/apache/apisix-helm-chart/blob/master/charts/apisix/values.yaml#L27-L30)
to learn the format of a shared dict
+# click
[here](https://github.com/apache/apisix-helm-chart/blob/master/charts/apisix/values.yaml#L48-L51)
to learn the format of a shared dict
customLuaSharedDicts: []
# - name: foo
# size: 10k
# - name: bar
# size: 1m
+# -- Overrides
[lua_shared_dict](https://github.com/openresty/lua-nginx-module#toc88) settings,
+# click
[here](https://github.com/apache/apisix/blob/master/conf/config-default.yaml#L258)
to view the default values.
+luaSharedDictsOverride: {}
+ # prometheus-metrics: 100m
+
discovery:
# -- Enable or disable Apache APISIX integration service discovery
enabled: false
(apisix) branch release3.9.2 updated (a6c2572d2 -> e34e5cf3f)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release3.9.2 in repository https://gitbox.apache.org/repos/asf/apisix.git from a6c2572d2 chore: release 3.9.2 add c0e3d9150 fix(schema): the port value greater than 65535 should not be allowed (#11043) add 7e4a69c56 perf(ssl): replace 'string.len' with '#' (#11078) add 538b9480f docs: correct consumer restriction type (#11082) add cca94f103 feat: enable sensitive fields encryption by default (#11076) add 71ad87d06 fix(ci): free disk space (#11081) add a7a5a2be5 feat: support more sensitive fields for encryption (#11095) add 531950329 brotli partial response fix (#11087) add b19fdcf34 fix: rectify the warning printed when `admin_key_required` == `false` (#11105) add e36db170f fix(request.header): core.request.header return string instead of table (#11127) add 4df549c21 fix: add post request headers only if auth request method is post (#11021) add c6b9f9931 feat: autogenerate admin api key if not passed (#11080) add 6edd86313 fix(prometheus): disable features when prometheus plugin is turned off (#7) add 25da64204 fix(request.headers): No longer returns all http headers, but limited to the default 100. (#11140) add c7c70e4b3 fix(kafka-pubsub): restore `pb.state` appropriately (#11135) add 1dfce2b73 chore(deps): bump apache/skywalking-eyes from 0.5.0 to 0.6.0 (#11128) add ea691046e feat(kafka-logger): add max req/resp body size attributes (#11133) add 59b50b64f feat(openid-connect): allow set headers in introspection request (#11090) add dd35c951a feat: add discovery k8s dump data interface (#1) add 07b3cc3f6 fix: close session in case of error to avoid blocked session (#11089) add 8096caa77 chore(deps): bump golang.org/x/net (#11171) add 0cad3295d chore(deps): bump golang.org/x/net (#11169) add 005281c13 chore: release/3.9 branch is invalid and the protection should be removed. (#11182) add e40a9d18a chore: restore release/3.9 branch protection #11183 add 53661eaeb fix(cors): avoid overwriting `Access-Control-Expose-Headers` response header (#11136) add 987d33d16 fix: multi-auth raise 500 error when use default conf (#11145) add f8ccc11e1 fix(ci): rollback golang.org/x/net version upgrade made by dependabot (#11202) add 77258c4fb fix(secret): rectify the way to fetch secret resource by id (#11164) add 64b81c48e perf: make fetch_secrets use cache for performance (#11201) add 114a08821 docs: improve `aws-lambda` plugin docs (#11211) add e193439e4 fix: stream route matcher is nil after first match (#11269) add 693d2aa91 fix: validation fails causing etcd events not to be handled correctly (#11268) add 0468d7891 feat: support hcv namespace (#11277) add b88cf9dd6 infra: Increase PR reviewers to 3 when merge to master. (#11280) add 55eeb6b19 docs: correct the default collector config apisix actually used for opentelemetry plugin (#11247) add c2ba478e8 docs: added Write a Review link (#11313) add 08cb3ad4a docs: add http3 docs (#11302) add cf8429249 feat: move tinyyaml to lyaml (#11312) add d106de5c6 fix(ssl): ssl key rotation caused request failure (#11305) add d77d67227 fix: add libyaml-dev dependency for apt. (#11291) add 953be46c3 fix: after updating the header, get the old value from the ctx.var (#11329) add 0cacb9072 docs: add plugin config to standalone deployment doc (#11332) add fec3137c2 docs: add http/3 in README.md. (#11318) add 3ad9c28a1 build(undeps): remove all rocks before remove openresty (#11333) add 5e383e0aa feat(secret): support store ssl.keys ssl.certs in secrets mamager (#11339) add 1a45d1da8 fix(datadog): report consumer username tag (#11354) add de1669dd1 docs: improve debug mode yaml comments (#11373) add 6d2de7ee2 fix: make the message clearer when API key is missing (#11370) add 4dbecfd56 docs: add http-dubbo docs (#11322) add 7f649bc4e ci: removed centos, chaos, fuzzing and fips CIs. (#11394) add 11643744e fix(grpc-transcode): filter out illegal INT(string) formats (#11367) add 54ebd05a2 chore(chaitin-waf): update dep lua-resty-t1k to 1.1.5 (#11391) add a17655bb7 chore(deps): update casbin to 1.41.9 (#11400) add 85a6348a1 fix: allow trailing period in SNI and CN for SSL (#11414) add c4a917bdd docs: fix broken example in body-transformer (#11409) add da5039da4 feat: move config-default.yaml to hardcoded lua file (#11343) add 36b2b8365 chore: warn log when sending requests to external services insecurely (#11403) add 507df1262 chore: remove `core.grpc` module (#11427) add 9980cb375 chore: upgrade openresty version to 1.25.3.2 (#11419) add d0af27b10 fix: plugin metadata add id value for etcd checker (#11452) add 8728863c8
(apisix) 01/01: Merge branch 'master' of github.com:apache/apisix into release3.9.2
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch release3.9.2 in repository https://gitbox.apache.org/repos/asf/apisix.git commit e34e5cf3f7eed05b7e9d26610a121ef5f173c473 Merge: a6c2572d2 8728863c8 Author: Abhishek Choudhary AuthorDate: Fri Aug 2 16:28:03 2024 +0545 Merge branch 'master' of github.com:apache/apisix into release3.9.2 .asf.yaml | 2 +- .github/workflows/centos7-ci.yml | 181 - .github/workflows/chaos.yml.disabled | 88 --- .github/workflows/fips.yml| 136 .github/workflows/fuzzing-ci.yaml | 86 --- .github/workflows/license-checker.yml | 2 +- .github/workflows/source-install.yml | 30 +- .requirements | 2 +- Makefile | 16 +- README.md | 21 +- apisix-master-0.rockspec | 8 +- apisix/admin/init.lua | 4 +- apisix/admin/resource.lua | 2 + apisix/cli/config.lua | 364 + apisix/cli/file.lua | 31 +- apisix/cli/ops.lua| 9 +- apisix/consumer.lua | 3 +- apisix/core/config_etcd.lua | 45 +- apisix/core/config_yaml.lua | 4 +- apisix/core/env.lua | 1 + apisix/core/grpc.lua | 27 - apisix/core/id.lua| 79 +- apisix/core/pubsub.lua| 12 +- apisix/core/request.lua | 15 +- apisix/core/response.lua | 16 +- apisix/core/utils.lua | 84 +++ apisix/debug.lua | 4 +- apisix/discovery/kubernetes/init.lua | 42 ++ apisix/init.lua | 7 - apisix/plugin.lua | 15 +- apisix/plugins/authz-casdoor.lua | 2 + apisix/plugins/authz-keycloak.lua | 7 +- apisix/plugins/brotli.lua | 3 +- apisix/plugins/cas-auth.lua | 2 + apisix/plugins/clickhouse-logger.lua | 4 + apisix/plugins/cors.lua | 12 +- apisix/plugins/datadog.lua| 4 +- apisix/plugins/elasticsearch-logger.lua | 4 + apisix/plugins/error-log-logger.lua | 5 + apisix/plugins/forward-auth.lua | 4 + apisix/plugins/http-logger.lua| 4 + apisix/plugins/jwe-decrypt.lua| 30 +- apisix/plugins/kafka-logger.lua | 30 + apisix/plugins/key-auth.lua | 2 +- apisix/plugins/ldap-auth.lua | 1 + apisix/plugins/limit-count.lua| 2 +- apisix/plugins/loki-logger.lua| 4 + apisix/plugins/multi-auth.lua | 4 + apisix/plugins/opa.lua| 3 + apisix/plugins/openid-connect.lua | 39 +- apisix/plugins/opentelemetry.lua | 2 + apisix/plugins/openwhisk.lua | 7 +- apisix/plugins/prometheus/exporter.lua| 16 + apisix/plugins/real-ip.lua| 4 +- apisix/plugins/rocketmq-logger.lua| 1 + apisix/plugins/skywalking-logger.lua | 2 + apisix/plugins/skywalking.lua | 2 + apisix/plugins/sls-logger.lua | 17 +- apisix/plugins/syslog.lua | 1 + apisix/plugins/tcp-logger.lua | 1 + apisix/plugins/ua-restriction.lua | 4 +- apisix/plugins/wolf-rbac.lua | 2 + apisix/plugins/zipkin.lua | 2 + apisix/schema_def.lua | 29 +- apisix/secret.lua | 41 +- apisix/secret/vault.lua | 16 +- apisix/ssl.lua| 21 +- apisix/ssl/router/radixtree_sni.lua | 5 +- apisix/stream/router/ip_port.lua | 4 - apisix/upstream.lua | 12 + apisix/utils/log-util.lua | 67 +- benchmark/run.sh | 8 +- ci/centos7-ci.sh | 1 + ci/common.sh | 3 + ci/free_disk_space.sh | 21 +- ci/redhat-ci.sh | 2 +- conf/c
(apisix) branch release3.9.2 created (now a6c2572d2)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release3.9.2 in repository https://gitbox.apache.org/repos/asf/apisix.git at a6c2572d2 chore: release 3.9.2 This branch includes the following new commits: new a6c2572d2 chore: release 3.9.2 The 1 revisions listed above as "new" are entirely new to this repository and will be described in separate emails. The revisions listed as "add" were already present in the repository and have only been added to this reference.
(apisix) 01/01: chore: release 3.9.2
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch release3.9.2 in repository https://gitbox.apache.org/repos/asf/apisix.git commit a6c2572d2c5354f516ec37670c302cde83a77b06 Author: Abhishek Choudhary AuthorDate: Fri Aug 2 16:08:52 2024 +0545 chore: release 3.9.2 --- CHANGELOG.md | 53 +++ apisix/core/version.lua | 2 +- docs/en/latest/building-apisix.md | 2 +- docs/en/latest/config.json| 2 +- docs/zh/latest/config.json| 2 +- 5 files changed, 57 insertions(+), 4 deletions(-) diff --git a/CHANGELOG.md b/CHANGELOG.md index 987559f9e..59e3f3c6f 100644 --- a/CHANGELOG.md +++ b/CHANGELOG.md @@ -23,6 +23,7 @@ title: Changelog ## Table of Contents +- [3.9.2](#392) - [3.9.1](#391) - [3.9.0](#390) - [3.8.0](#380) @@ -77,6 +78,58 @@ title: Changelog - [0.7.0](#070) - [0.6.0](#060) +## 3.9.2 + +### Change + +- Remove `core.grpc` module [11427](https://github.com/apache/apisix/pull/11427) +- Move config-default.yaml to hardcoded lua file [11343](https://github.com/apache/apisix/pull/11343) +- Add max req/resp body size attributes [11133](https://github.com/apache/apisix/pull/11133) + +### Plugins + +- Allow set headers in introspection request [11090](https://github.com/apache/apisix/pull/11090) + +### Bug Fixes + +- Fix: etcd sync data checker should work [11457](https://github.com/apache/apisix/pull/11457) +- Fix: plugin metadata add id value for etcd checker [11452](https://github.com/apache/apisix/pull/11452) +- Fix: allow trailing period in SNI and CN for SSL [11414](https://github.com/apache/apisix/pull/11414) +- Fix: filter out illegal INT(string) formats [11367](https://github.com/apache/apisix/pull/11367) +- Fix: make the message clearer when API key is missing [11370](https://github.com/apache/apisix/pull/11370) +- Fix: report consumer username tag in datadog [11354](https://github.com/apache/apisix/pull/11354) +- Fix: after updating the header, get the old value from the ctx.var [11329](https://github.com/apache/apisix/pull/11329) +- Fix: ssl key rotation caused request failure [11305](https://github.com/apache/apisix/pull/11305) +- Fix: validation fails causing etcd events not to be handled correctly [11268](https://github.com/apache/apisix/pull/11268) +- Fix: stream route matcher is nil after first match [11269](https://github.com/apache/apisix/pull/11269) +- Fix: rectify the way to fetch secret resource by id [11164](https://github.com/apache/apisix/pull/11164) +- Fix: multi-auth raise 500 error when use default conf [11145](https://github.com/apache/apisix/pull/11145) +- Fix: avoid overwriting `Access-Control-Expose-Headers` response header [11136](https://github.com/apache/apisix/pull/11136) +- Fix: close session in case of error to avoid blocked session [11089](https://github.com/apache/apisix/pull/11089) +- Fix: restore `pb.state` appropriately [11135](https://github.com/apache/apisix/pull/11135) +- Fix: add a default limit of 100 for `get_headers()` [11140](https://github.com/apache/apisix/pull/11140) +- Fix: disable features when prometheus plugin is turned off [7](https://github.com/apache/apisix/pull/7) +- Fix: add post request headers only if auth request method is POST [11021](https://github.com/apache/apisix/pull/11021) +- Fix: core.request.header return strings instead of table [11127](https://github.com/apache/apisix/pull/11127) +- Fix: brotli partial response [11087](https://github.com/apache/apisix/pull/11087) +- Fix: the port value greater than 65535 should not be allowed [11043](https://github.com/apache/apisix/pull/11043) + +### Core + +- Upgrade openresty version to 1.25.3.2 [11419](https://github.com/apache/apisix/pull/11419) +- Warn log when sending requests to external services insecurely [11403](https://github.com/apache/apisix/pull/11403) +- Update casbin to 1.41.9 [11400](https://github.com/apache/apisix/pull/11400) +- Update lua-resty-t1k to 1.1.5 [11391](https://github.com/apache/apisix/pull/11391) +- Support store ssl.keys ssl.certs in secrets mamager [11339](https://github.com/apache/apisix/pull/11339) +- Move tinyyaml to lyaml [11312](https://github.com/apache/apisix/pull/11312) +- Support hcv namespace [11277](https://github.com/apache/apisix/pull/11277) +- Add discovery k8s dump data interface [1](https://github.com/apache/apisix/pull/1) +- Autogenerate admin api key if not passed [11080](https://github.com/apache/apisix/pull/11080) +- Support more sensitive fields for encryption [11095](https://github.com/apache/apisix/pull/11095) +- Enable sensitive fields encryption by default [11076](https://github.com/apache/apisix/pull/11076) +- Make fetch_secrets use cache for performance [11201](https://github.com/apache/apisix/pull/11201) +- Replace 'string.len' with '#' [11078](https://github.com/apache/apisix/pull/11078) + ## 3.9.1
(apisix) branch master updated: chore: upgrade openresty version to 1.25.3.2 (#11419)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new 9980cb375 chore: upgrade openresty version to 1.25.3.2 (#11419) 9980cb375 is described below commit 9980cb3754720676f0c774fb59c19a5465d500f4 Author: Shreemaan Abhishek AuthorDate: Tue Jul 30 13:42:05 2024 +0545 chore: upgrade openresty version to 1.25.3.2 (#11419) --- .requirements | 2 +- 1 file changed, 1 insertion(+), 1 deletion(-) diff --git a/.requirements b/.requirements index bbfa42c49..6c393209f 100644 --- a/.requirements +++ b/.requirements @@ -17,4 +17,4 @@ APISIX_PACKAGE_NAME=apisix -APISIX_RUNTIME=1.2.0 +APISIX_RUNTIME=1.2.1
(apisix) branch master updated: fix: allow trailing period in SNI and CN for SSL (#11414)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new 85a6348a1 fix: allow trailing period in SNI and CN for SSL (#11414) 85a6348a1 is described below commit 85a6348a1eb9b2009d60a6dd9590bafeed70249a Author: Abhishek Choudhary AuthorDate: Thu Jul 18 14:59:52 2024 +0545 fix: allow trailing period in SNI and CN for SSL (#11414) --- apisix/ssl.lua | 2 + apisix/ssl/router/radixtree_sni.lua | 2 + t/certs/test-dot.crt| 18 +++ t/certs/test-dot.key| 28 t/router/radixtree-sni3.t | 283 5 files changed, 333 insertions(+) diff --git a/apisix/ssl.lua b/apisix/ssl.lua index ad820822c..412c9b86b 100644 --- a/apisix/ssl.lua +++ b/apisix/ssl.lua @@ -29,6 +29,7 @@ local str_byte = string.byte local assert = assert local type = type local ipairs = ipairs +local ngx_sub = ngx.re.sub ffi.cdef[[ unsigned long ERR_peek_error(void); @@ -66,6 +67,7 @@ function _M.server_name(clienthello) end end +sni = ngx_sub(sni, "\\.$", "", "jo") sni = str_lower(sni) return sni end diff --git a/apisix/ssl/router/radixtree_sni.lua b/apisix/ssl/router/radixtree_sni.lua index aab6aafe8..caa69194e 100644 --- a/apisix/ssl/router/radixtree_sni.lua +++ b/apisix/ssl/router/radixtree_sni.lua @@ -285,9 +285,11 @@ local function ssl_filter(ssl) end if ssl.value.sni then +ssl.value.sni = ngx.re.sub(ssl.value.sni, "\\.$", "", "jo") ssl.value.sni = str_lower(ssl.value.sni) elseif ssl.value.snis then for i, v in ipairs(ssl.value.snis) do +v = ngx.re.sub(v, "\\.$", "", "jo") ssl.value.snis[i] = str_lower(v) end end diff --git a/t/certs/test-dot.crt b/t/certs/test-dot.crt new file mode 100644 index 0..a9dfd3326 --- /dev/null +++ b/t/certs/test-dot.crt @@ -0,0 +1,18 @@ +-BEGIN CERTIFICATE- +MIIC+zCCAeOgAwIBAgIUWUtIDbrU8QF90OXlMKyClPRNRcgwDQYJKoZIhvcNAQEL +BQAwETEPMA0GA1UEAwwGUk9PVENBMCAXDTI0MDcxNzE2MDcyM1oYDzIxMjQwNjIz +MTYwNzIzWjAYMRYwFAYDVQQDDA13d3cudGVzdC5jb20uMIIBIjANBgkqhkiG9w0B +AQEFAAOCAQ8AMIIBCgKCAQEApkX5NgwwEC/brmrUAfxSMGMaYOzjx+3BlCC23sLR +0uQ1+KMXt/Pd2QJVqREjEAiwXCMuHbB0qWD5985SfsjeRJJ8rc8CzJfcb7QESKfK +GdLaD8LsyAAg+Rxm0QyVFGrLJ82sjbEimLGCkLMpYsePxEDEifKPp3Z9bRUFT0zm +xcUEXojw5pzjrjIvfqVenWNP716s7bSdOFoc4RBlAdEI3pFUasLF9Lovz7BJLvtY +aoqgCNfb78C6zreDLswET5/338AVf9yPYc5HOthmygxkYTniK47/fOW64RQKXQ2X +EtBiIzN6dSXfTCXSpvow5XIR02rLoxsVEEwM9ODgUAJg6QIDAQABo0IwQDAdBgNV +HQ4EFgQUAHYNW6/hFM+Bqd2KNBXbLgJLaxcwHwYDVR0jBBgwFoAUjwSzlti+ag+f +BzoRa0wZbMaGh10wDQYJKoZIhvcNAQELBQADggEBAA1HfiDtHZV8sxJjasnNSM9f +6XTRCjT+DcABXm7k/Dmb8q5rpyqYwkUfadgAbmPx6T/dC4z7LblkcTkwD7azpkNE +fXY3Hx4qxSVSbSOHWnaSOX/8BRiPbSQNWGyTGh9AK/Vp/VJU2cDPqFbjQKHFq3ZI +w3GnRDerdA8vm5qzJ5/9wMF2ZsmnMiV3zX0Xisbzx/dponz6ktfygE3bk8Pb4wKt +D0EjbnLIXwyHv1czJrcRq0Y8irWaTY97vdff/J2aO9582zFNx6AnsU3+6fGsDyrO +ss+ggKDLK+aOBKroTNb3TgdPyPOgobUwLByFdKT/zTtWbkqyYMZzBme2SD4TWok= +-END CERTIFICATE- diff --git a/t/certs/test-dot.key b/t/certs/test-dot.key new file mode 100644 index 0..5ed8aba21 --- /dev/null +++ b/t/certs/test-dot.key @@ -0,0 +1,28 @@ +-BEGIN PRIVATE KEY- +MIIEvQIBADANBgkqhkiG9w0BAQEFAASCBKcwggSjAgEAAoIBAQCmRfk2DDAQL9uu +atQB/FIwYxpg7OPH7cGUILbewtHS5DX4oxe3893ZAlWpESMQCLBcIy4dsHSpYPn3 +zlJ+yN5EknytzwLMl9xvtARIp8oZ0toPwuzIACD5HGbRDJUUassnzayNsSKYsYKQ +sylix4/EQMSJ8o+ndn1tFQVPTObFxQReiPDmnOOuMi9+pV6dY0/vXqzttJ04Whzh +EGUB0QjekVRqwsX0ui/PsEku+1hqiqAI19vvwLrOt4MuzARPn/ffwBV/3I9hzkc6 +2GbKDGRhOeIrjv985brhFApdDZcS0GIjM3p1Jd9MJdKm+jDlchHTasujGxUQTAz0 +4OBQAmDpAgMBAAECggEAD84ctm8h5fYApDOWJ8Kp9tzCwgYekE94vEmATIw5CPqF +qVbqbyNUmhdTWGzvN+vVhMqYzHxsmHmmBTDU7WWPYDYK+TQRbGx+iRUz54qghsQg +04j4PDor6DYTjWlMZfqRSV0u+vCErP5JnpLTOyckUrfD3ueCUX0tRsBN5wf0s0WD +7AiUIdVBesQwIuIin3MyhGFtQC0PNta3NdSBVbnUA69OL3QNxPoai5LACrAf1hkf +wPD/y6y2CswdER+j+obPChjTcnJFjRCkqqO+66QZWmMmVxq4ymCQg9IOgLRWtfhI +6Ts5RxVn12kEuPULk9oHHOjC+MVh3BmWFLb58G/gwQKBgQDUCSd/2uswTVlTYpw6 +XO3iVyoZVeo/BIiOm/kjmqmr5U/D7ZO27ElKBTe9CDQ4WB5PuisCy0/SnsJJsPpf +pWif2v0mVs3T9K7J1M1yQU2iMs+Z2stzLGe5AASImYpw9091v57A/1jI4VUoodOr +7sMo+9ROqx6dTG/tJgUa+VZaKQKBgQDIv8CZHv4LqvQEQrGoTcKOxQP47nsbfEPW +B0GQscykvRTWxlTfFdfFM4VG2ApERZDwjPFU84n4dH8J7P14iy2ty70krzHWNfjY +y52CXUb295HsdcQ0bP8wztuvM/Jfh1mKKynmezvAZlTSb+GMAAMrReuG2Ga1/gp1 +5daCd4IowQKBgG//md6eCybLZIh4CN+HIJwywGj7iazZvyvc1T9qPX8vs+9g+Wpg +6uFvWh6+S58LZI9mXbuvGq288BEuq0GERHxTlu3+YeA4WW8AubhFKDWpsyCogliG +tw7wJHTm7Up4R3+BxOBawFHzPCEnQYCKsIlgY6deGeCqdGCGeaHi3CrpAoGAdWam +xSW53qr4j/FNIqdvK72OaCtX9agDqAyQTIWer40gvcY5ZknI6TwLKnY38ttYO0XB +8TOIMbQ3g1+EkNWcPjKTh/upQqRHxsm1cMMKOG5qeYYZ26sOxsWC9oCDs1hdhg9e +LrtNI2T1IChsGEr9j3YRmse9sZtDFNX4UE6B4UEC
(apisix-website) branch master updated: blog: add april monthly-report.md (#1793)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix-website.git The following commit(s) were added to refs/heads/master by this push: new 5f5dfa341ba blog: add april monthly-report.md (#1793) 5f5dfa341ba is described below commit 5f5dfa341ba3edb0536221e473e47a6254c95d7b Author: Yilia Lin <114121331+yilial...@users.noreply.github.com> AuthorDate: Tue Apr 30 16:45:45 2024 +0800 blog: add april monthly-report.md (#1793) --- blog/en/blog/2024/04/30/monthly-report.md | 37 +++ blog/zh/blog/2024/04/30/monthly-report.md | 36 ++ 2 files changed, 73 insertions(+) diff --git a/blog/en/blog/2024/04/30/monthly-report.md b/blog/en/blog/2024/04/30/monthly-report.md new file mode 100644 index 000..0490906dbf6 --- /dev/null +++ b/blog/en/blog/2024/04/30/monthly-report.md @@ -0,0 +1,37 @@ +--- +title: "Monthly Report (April 01 - April 30)" +keywords: ["Apache APISIX", "API Gateway", "Monthly Report", "Contributor"] +description: Our monthly Apache APISIX community report generates insights into the project's monthly developments. The reports provide a pathway into the Apache APISIX community, ensuring that you stay well-informed and actively involved. +tags: [Community] +image: https://static.apiseven.com/uploads/2024/04/30/XvSXCOav_monthly-report-apr-en.png +--- + +> We have recently made some additions and improvements to specific features within Apache APISIX. These include adding discovery k8s dump data interface, adding max req/resp body size attributes (`max_resp_body_bytes` and `max_req_body_bytes`) in the `kafka-logger` plugin, and autogenerating the admin API key if they are not configured in the configuration file. For detailed information, please read the monthly report. + +## Introduction + +From its inception, the Apache APISIX project has embraced the ethos of open-source community collaboration, propelling it into the ranks of the most active global open-source API gateway projects. The proverbial wisdom of 'teamwork makes the dream work' rings true in our way and is made possible by the collective effort of our community. + +From 04.01 to 04.30, a total of 16 contributors made 43 commits to Apache APISIX. We sincerely appreciate your contributions to Apache APISIX. + +## Contributor Statistics + +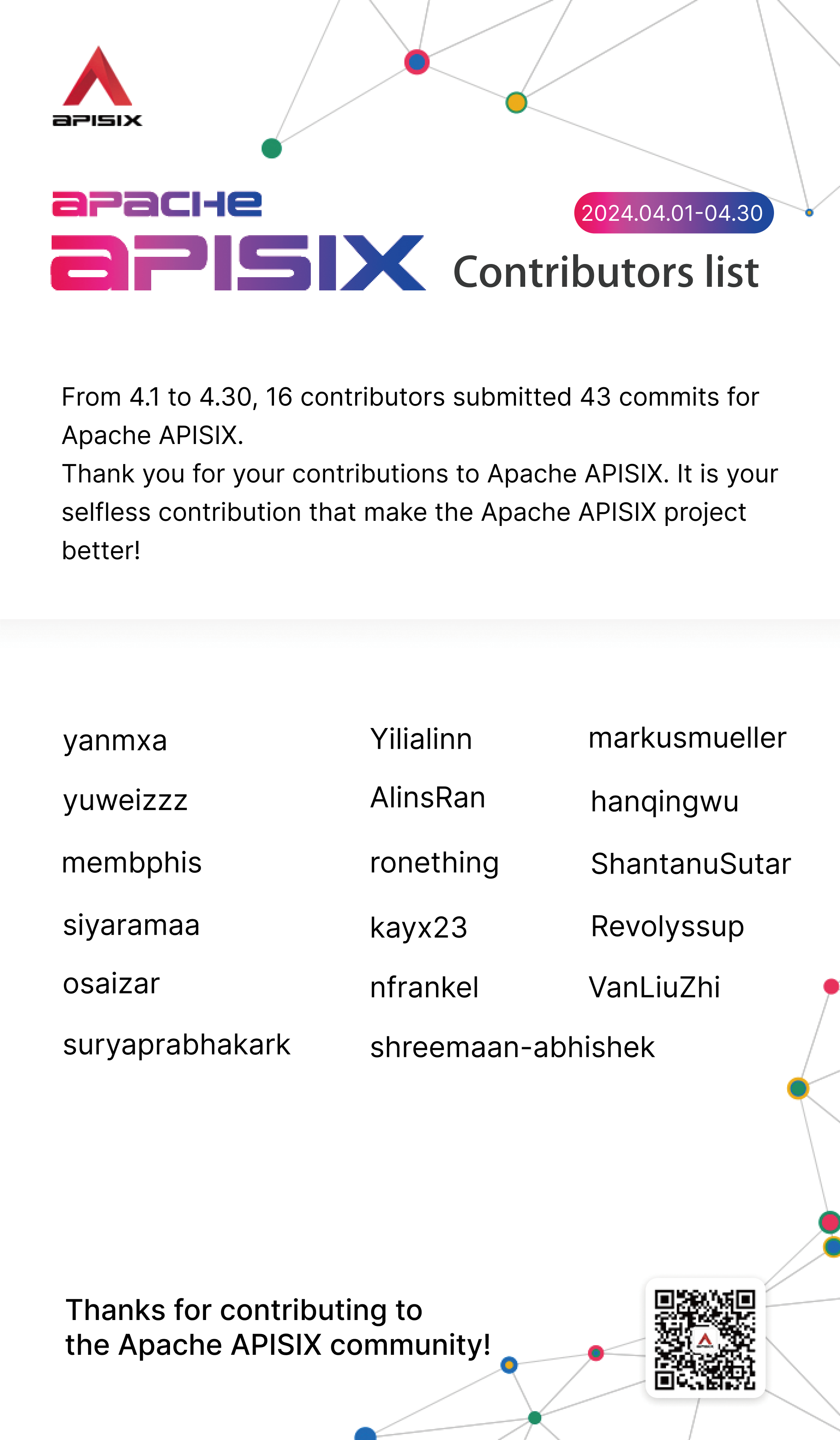 + + + +## Recent Feature Highlights + +- [Add discovery k8s dump data interface](https://github.com/apache/apisix/pull/1)(Contributor: [hanqingwu](https://github.com/hanqingwu)) + +- [Add max req/resp body size attributes (`max_resp_body_bytes` and `max_req_body_bytes`) in the `kafka-logger` plugin](https://github.com/apache/apisix/pull/11133)(Contributor: [shreemaan-abhishek](https://github.com/shreemaan-abhishek)) + +- [Autogenerate the admin API key if not configured in the configuration file](https://github.com/apache/apisix/pull/11080)(Contributor: [Revolyssup](https://github.com/Revolyssup)) + +## Recent Blog Recommendations + +- [Release Apache APISIX 3.8.1](https://apisix.apache.org/blog/2024/04/29/release-apache-apisix-3.8.1/) + +- [Release Apache APISIX 3.9.1](https://apisix.apache.org/blog/2024/04/29/release-apache-apisix-3.9.1/) + +The official website and GitHub Issues of Apache APISIX provide a wealth of documentation of tutorials and real-world use cases. If you encounter any issues, you can refer to the documentation, search for keywords in Issues, or participate in discussions on Issues to share your ideas and practical experiences. diff --git a/blog/zh/blog/2024/04/30/monthly-report.md b/blog/zh/blog/2024/04/30/monthly-report.md new file mode 100644 index 000..1c1aa382abe --- /dev/null +++ b/blog/zh/blog/2024/04/30/monthly-report.md @@ -0,0 +1,36 @@ +--- +title: "社区月报 (04.01 - 04.30)" +keywords: ["Apache APISIX", "API 网关", "社区月报", "贡献者"] +description: Apache APISIX 社区的月报旨在帮助社区成员更全面地了解社区的最新动态,方便大家参与到 Apache APISIX 社区中来。 +tags: [Community] +image: https://static.apiseven.com/uploads/2024/04/30/0133BTQL_monthly-report-apr-cn.png +--- +> 最近,我们新增并改进了 Apache APISIX 的部分功能,包含新增 Kubernetes 服务的转存数据接口、在 `kafka-logger` 插件中引入新属性 `max_resp_body_bytes` 和 `max_req_body_bytes` 以降低 CPU 使用率,和自动生成 Admin API 密钥以删除 API 密钥的硬编码等。有关更多功能新亮点,请阅读本期月报。 + +## 导语 + +Apache APISIX 项目始终秉承着开源社区协作的精神,自问世起便崭露头角,如今已经成为全球最活跃的开源 API 网关项目之一。正如谚语所言,“众人拾柴火焰高”,这一辉煌成就,得益于整个社区伙伴的协同努力。 + +从 2024.04.01 至 2024.04.30,有 16 名开发者提交了 43 个 commit,为 Apache APISIX 做出了重要贡献。感谢这些伙伴们对 Apache APISIX 的无私支持!正是因为你们的付出,才能让 Apache APISIX 项目不断改进、提升和壮
(apisix) branch master updated (77258c4fb -> 64b81c48e)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git from 77258c4fb fix(secret): rectify the way to fetch secret resource by id (#11164) add 64b81c48e perf: make fetch_secrets use cache for performance (#11201) No new revisions were added by this update. Summary of changes: apisix/consumer.lua | 3 ++- apisix/plugins/authz-keycloak.lua | 2 +- apisix/plugins/limit-count.lua | 2 +- apisix/ssl/router/radixtree_sni.lua | 3 ++- 4 files changed, 6 insertions(+), 4 deletions(-)
(apisix) branch master updated: fix(secret): rectify the way to fetch secret resource by id (#11164)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 77258c4fb fix(secret): rectify the way to fetch secret resource by id
(#11164)
77258c4fb is described below
commit 77258c4fb4b15ec194cb9adb33b23314ace4b696
Author: Abhishek Choudhary
AuthorDate: Thu Apr 25 19:02:50 2024 +0545
fix(secret): rectify the way to fetch secret resource by id (#11164)
---
apisix/secret.lua | 40 ++--
1 file changed, 6 insertions(+), 34 deletions(-)
diff --git a/apisix/secret.lua b/apisix/secret.lua
index 90a99d321..6ba02768d 100644
--- a/apisix/secret.lua
+++ b/apisix/secret.lua
@@ -26,7 +26,6 @@ local byte = string.byte
local type = type
local pcall = pcall
local pairs = pairs
-local ipairs= ipairs
local _M = {}
@@ -50,36 +49,6 @@ local function check_secret(conf)
end
-local secret_kv_lrucache = core.lrucache.new({
-ttl = 300, count = 512
-})
-
-local function create_secret_kvs(values)
-local secret_managers = {}
-
-for _, v in ipairs(values) do
-if v then
-local path = v.value.id
-local idx = find(path, "/")
-if not idx then
-core.log.error("no secret id")
-return nil
-end
-
-local manager = sub(path, 1, idx - 1)
-local id = sub(path, idx + 1)
-
-if not secret_managers[manager] then
-secret_managers[manager] = {}
-end
-secret_managers[manager][id] = v.value
-end
-end
-
-return secret_managers
-end
-
-
local function secret_kv(manager, confid)
local secret_values
secret_values = core.config.fetch_created_obj("/secrets")
@@ -87,9 +56,12 @@ end
return nil
end
-local secret_managers = secret_kv_lrucache("secret_kv",
secret_values.conf_version,
-create_secret_kvs, secret_values.values)
-return secret_managers[manager] and secret_managers[manager][confid]
+local secret = secret_values:get(manager .. "/" .. confid)
+if not secret then
+return nil
+end
+
+return secret.value
end
(apisix) branch master updated: fix(ci): rollback golang.org/x/net version upgrade made by dependabot (#11202)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new f8ccc11e1 fix(ci): rollback golang.org/x/net version upgrade made by dependabot (#11202) f8ccc11e1 is described below commit f8ccc11e193fabde23fb4651debd7caeb17056dc Author: Abhishek Choudhary AuthorDate: Thu Apr 25 18:48:43 2024 +0545 fix(ci): rollback golang.org/x/net version upgrade made by dependabot (#11202) --- .../openfunction/function-example/test-body/go.mod | 6 ++-- .../openfunction/function-example/test-body/go.sum | 34 ++ .../openfunction/function-example/test-uri/go.mod | 6 ++-- .../openfunction/function-example/test-uri/go.sum | 32 ++-- 4 files changed, 12 insertions(+), 66 deletions(-) diff --git a/ci/pod/openfunction/function-example/test-body/go.mod b/ci/pod/openfunction/function-example/test-body/go.mod index 41af08abd..bf571e0ba 100644 --- a/ci/pod/openfunction/function-example/test-body/go.mod +++ b/ci/pod/openfunction/function-example/test-body/go.mod @@ -19,9 +19,9 @@ require ( go.uber.org/atomic v1.9.0 // indirect go.uber.org/multierr v1.7.0 // indirect go.uber.org/zap v1.19.1 // indirect - golang.org/x/net v0.23.0 // indirect - golang.org/x/sys v0.18.0 // indirect - golang.org/x/text v0.14.0 // indirect + golang.org/x/net v0.0.0-20211015210444-4f30a5c0130f // indirect + golang.org/x/sys v0.0.0-20211019181941-9d821ace8654 // indirect + golang.org/x/text v0.3.7 // indirect google.golang.org/genproto v0.0.0-20210831024726-fe130286e0e2 // indirect google.golang.org/grpc v1.40.0 // indirect google.golang.org/protobuf v1.33.0 // indirect diff --git a/ci/pod/openfunction/function-example/test-body/go.sum b/ci/pod/openfunction/function-example/test-body/go.sum index 0e3260547..f51a5304a 100644 --- a/ci/pod/openfunction/function-example/test-body/go.sum +++ b/ci/pod/openfunction/function-example/test-body/go.sum @@ -1094,7 +1094,6 @@ github.com/yuin/goldmark v1.1.30/go.mod h1:3hX8gzYuyVAZsxl0MRgGTJEmQBFcNTphYh9de github.com/yuin/goldmark v1.1.32/go.mod h1:3hX8gzYuyVAZsxl0MRgGTJEmQBFcNTphYh9decYSb74= github.com/yuin/goldmark v1.2.1/go.mod h1:3hX8gzYuyVAZsxl0MRgGTJEmQBFcNTphYh9decYSb74= github.com/yuin/goldmark v1.3.5/go.mod h1:mwnBkeHKe2W/ZEtQ+71ViKU8L12m81fl3OWwC1Zlc8k= -github.com/yuin/goldmark v1.4.13/go.mod h1:6yULJ656Px+3vBD8DxQVa3kxgyrAnzto9xy5taEt/CY= github.com/yuin/gopher-lua v0.0.0-20191220021717-ab39c6098bdb/go.mod h1:gqRgreBUhTSL0GeU64rtZ3Uq3wtjOa/TB2YfrtkCbVQ= github.com/yuin/gopher-lua v0.0.0-20200603152657-dc2b0ca8b37e/go.mod h1:gqRgreBUhTSL0GeU64rtZ3Uq3wtjOa/TB2YfrtkCbVQ= github.com/zenazn/goji v0.9.0/go.mod h1:7S9M489iMyHBNxwZnk9/EHS098H4/F6TATF2mIxtB1Q= @@ -1182,8 +1181,6 @@ golang.org/x/crypto v0.0.0-20210220033148-5ea612d1eb83/go.mod h1:jdWPYTVW3xRLrWP golang.org/x/crypto v0.0.0-20210314154223-e6e6c4f2bb5b/go.mod h1:T9bdIzuCu7OtxOm1hfPfRQxPLYneinmdGuTeoZ9dtd4= golang.org/x/crypto v0.0.0-20210513164829-c07d793c2f9a/go.mod h1:P+XmwS30IXTQdn5tA2iutPOUgjI07+tq3H3K9MVA1s8= golang.org/x/crypto v0.0.0-20210921155107-089bfa567519/go.mod h1:GvvjBRRGRdwPK5ydBHafDWAxML/pGHZbMvKqRZ5+Abc= -golang.org/x/crypto v0.19.0/go.mod h1:Iy9bg/ha4yyC70EfRS8jz+B6ybOBKMaSxLj6P6oBDfU= -golang.org/x/crypto v0.21.0/go.mod h1:0BP7YvVV9gBbVKyeTG0Gyn+gZm94bibOW5BjDEYAOMs= golang.org/x/exp v0.0.0-20190121172915-509febef88a4/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA= golang.org/x/exp v0.0.0-20190306152737-a1d7652674e8/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA= golang.org/x/exp v0.0.0-20190510132918-efd6b22b2522/go.mod h1:ZjyILWgesfNpC6sMxTJOJm9Kp84zZh5NQWvqDGG3Qr8= @@ -1221,8 +1218,6 @@ golang.org/x/mod v0.3.0/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= golang.org/x/mod v0.4.0/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= golang.org/x/mod v0.4.1/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= golang.org/x/mod v0.4.2/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= -golang.org/x/mod v0.6.0-dev.0.20220419223038-86c51ed26bb4/go.mod h1:jJ57K6gSWd91VN4djpZkiMVwK6gcyfeH4XE8wZrZaV4= -golang.org/x/mod v0.8.0/go.mod h1:iBbtSCu2XBx23ZKBPSOrRkjjQPZFPuis4dIYUhu/chs= golang.org/x/net v0.0.0-20180724234803-3673e40ba225/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= golang.org/x/net v0.0.0-20180826012351-8a410e7b638d/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= golang.org/x/net v0.0.0-20180906233101-161cd47e91fd/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= @@ -1285,13 +1280,8 @@ golang.org/x/net v0.0.0-20210525063256-abc453219eb5/go.mod h1:9nx3DQGgdP8bBQD5qx golang.org/x/net v0.0.0-20210610132358-84b48f89b13b/go.mod h1:9nx3DQGgdP8bBQD5qxJ1jj9UTztislL4KSBs9R2vV5Y= golang.org/x/net v0.0.0
(apisix) branch revert-11171-dependabot/go_modules/ci/pod/openfunction/function-example/test-uri/golang.org/x/net-0.23.0 updated (ec8059eb7 -> 63bc0d3dc)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch revert-11171-dependabot/go_modules/ci/pod/openfunction/function-example/test-uri/golang.org/x/net-0.23.0 in repository https://gitbox.apache.org/repos/asf/apisix.git from ec8059eb7 Revert "chore(deps): bump golang.org/x/net (#11171)" add 63bc0d3dc Revert "chore(deps): bump golang.org/x/net (#11169)" No new revisions were added by this update. Summary of changes: .../openfunction/function-example/test-body/go.mod | 6 ++-- .../openfunction/function-example/test-body/go.sum | 34 ++ 2 files changed, 6 insertions(+), 34 deletions(-)
(apisix) branch revert-11171-dependabot/go_modules/ci/pod/openfunction/function-example/test-uri/golang.org/x/net-0.23.0 created (now ec8059eb7)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch revert-11171-dependabot/go_modules/ci/pod/openfunction/function-example/test-uri/golang.org/x/net-0.23.0 in repository https://gitbox.apache.org/repos/asf/apisix.git at ec8059eb7 Revert "chore(deps): bump golang.org/x/net (#11171)" This branch includes the following new commits: new ec8059eb7 Revert "chore(deps): bump golang.org/x/net (#11171)" The 1 revisions listed above as "new" are entirely new to this repository and will be described in separate emails. The revisions listed as "add" were already present in the repository and have only been added to this reference.
(apisix) 01/01: Revert "chore(deps): bump golang.org/x/net (#11171)"
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch revert-11171-dependabot/go_modules/ci/pod/openfunction/function-example/test-uri/golang.org/x/net-0.23.0 in repository https://gitbox.apache.org/repos/asf/apisix.git commit ec8059eb773e20b5d787e917d327eecb78d029c6 Author: Abhishek Choudhary AuthorDate: Thu Apr 25 12:49:47 2024 +0545 Revert "chore(deps): bump golang.org/x/net (#11171)" This reverts commit 8096caa775cd49ee2fcbcd2f4d2c832083b5387f. --- .../openfunction/function-example/test-uri/go.mod | 6 ++-- .../openfunction/function-example/test-uri/go.sum | 32 ++ 2 files changed, 6 insertions(+), 32 deletions(-) diff --git a/ci/pod/openfunction/function-example/test-uri/go.mod b/ci/pod/openfunction/function-example/test-uri/go.mod index 444fbb65e..046483f1e 100644 --- a/ci/pod/openfunction/function-example/test-uri/go.mod +++ b/ci/pod/openfunction/function-example/test-uri/go.mod @@ -20,9 +20,9 @@ require ( go.uber.org/atomic v1.9.0 // indirect go.uber.org/multierr v1.7.0 // indirect go.uber.org/zap v1.21.0 // indirect - golang.org/x/net v0.23.0 // indirect - golang.org/x/sys v0.18.0 // indirect - golang.org/x/text v0.14.0 // indirect + golang.org/x/net v0.0.0-20220621193019-9d032be2e588 // indirect + golang.org/x/sys v0.0.0-20220520151302-bc2c85ada10a // indirect + golang.org/x/text v0.3.7 // indirect google.golang.org/genproto v0.0.0-20220622171453-ea41d75dfa0f // indirect google.golang.org/grpc v1.47.0 // indirect google.golang.org/protobuf v1.33.0 // indirect diff --git a/ci/pod/openfunction/function-example/test-uri/go.sum b/ci/pod/openfunction/function-example/test-uri/go.sum index 7c6d60879..7aaa3ce33 100644 --- a/ci/pod/openfunction/function-example/test-uri/go.sum +++ b/ci/pod/openfunction/function-example/test-uri/go.sum @@ -1656,7 +1656,6 @@ github.com/yuin/goldmark v1.2.1/go.mod h1:3hX8gzYuyVAZsxl0MRgGTJEmQBFcNTphYh9dec github.com/yuin/goldmark v1.3.5/go.mod h1:mwnBkeHKe2W/ZEtQ+71ViKU8L12m81fl3OWwC1Zlc8k= github.com/yuin/goldmark v1.4.0/go.mod h1:mwnBkeHKe2W/ZEtQ+71ViKU8L12m81fl3OWwC1Zlc8k= github.com/yuin/goldmark v1.4.1/go.mod h1:mwnBkeHKe2W/ZEtQ+71ViKU8L12m81fl3OWwC1Zlc8k= -github.com/yuin/goldmark v1.4.13/go.mod h1:6yULJ656Px+3vBD8DxQVa3kxgyrAnzto9xy5taEt/CY= github.com/yuin/gopher-lua v0.0.0-20191220021717-ab39c6098bdb/go.mod h1:gqRgreBUhTSL0GeU64rtZ3Uq3wtjOa/TB2YfrtkCbVQ= github.com/yuin/gopher-lua v0.0.0-20200603152657-dc2b0ca8b37e/go.mod h1:gqRgreBUhTSL0GeU64rtZ3Uq3wtjOa/TB2YfrtkCbVQ= github.com/yvasiyarov/go-metrics v0.0.0-20140926110328-57bccd1ccd43/go.mod h1:aX5oPXxHm3bOH+xeAttToC8pqch2ScQN/JoXYupl6xs= @@ -1814,8 +1813,6 @@ golang.org/x/crypto v0.0.0-20211215153901-e495a2d5b3d3/go.mod h1:IxCIyHEi3zRg3s0 golang.org/x/crypto v0.0.0-20220112180741-5e0467b6c7ce/go.mod h1:IxCIyHEi3zRg3s0A5j5BB6A9Jmi73HwBIUl50j+osU4= golang.org/x/crypto v0.0.0-20220131195533-30dcbda58838/go.mod h1:IxCIyHEi3zRg3s0A5j5BB6A9Jmi73HwBIUl50j+osU4= golang.org/x/crypto v0.0.0-20220511200225-c6db032c6c88/go.mod h1:IxCIyHEi3zRg3s0A5j5BB6A9Jmi73HwBIUl50j+osU4= -golang.org/x/crypto v0.19.0/go.mod h1:Iy9bg/ha4yyC70EfRS8jz+B6ybOBKMaSxLj6P6oBDfU= -golang.org/x/crypto v0.21.0/go.mod h1:0BP7YvVV9gBbVKyeTG0Gyn+gZm94bibOW5BjDEYAOMs= golang.org/x/exp v0.0.0-20180321215751-8460e604b9de/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA= golang.org/x/exp v0.0.0-20180807140117-3d87b88a115f/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA= golang.org/x/exp v0.0.0-20190121172915-509febef88a4/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA= @@ -1858,8 +1855,6 @@ golang.org/x/mod v0.4.1/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= golang.org/x/mod v0.4.2/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= golang.org/x/mod v0.5.0/go.mod h1:5OXOZSfqPIIbmVBIIKWRFfZjPR0E5r58TLhUjH0a2Ro= golang.org/x/mod v0.5.1/go.mod h1:5OXOZSfqPIIbmVBIIKWRFfZjPR0E5r58TLhUjH0a2Ro= -golang.org/x/mod v0.6.0-dev.0.20220419223038-86c51ed26bb4/go.mod h1:jJ57K6gSWd91VN4djpZkiMVwK6gcyfeH4XE8wZrZaV4= -golang.org/x/mod v0.8.0/go.mod h1:iBbtSCu2XBx23ZKBPSOrRkjjQPZFPuis4dIYUhu/chs= golang.org/x/net v0.0.0-20180530234432-1e491301e022/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= golang.org/x/net v0.0.0-20180724234803-3673e40ba225/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= golang.org/x/net v0.0.0-20180826012351-8a410e7b638d/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= @@ -1944,13 +1939,8 @@ golang.org/x/net v0.0.0-20220127200216-cd36cc0744dd/go.mod h1:CfG3xpIq0wQ8r1q4Su golang.org/x/net v0.0.0-20220225172249-27dd8689420f/go.mod h1:CfG3xpIq0wQ8r1q4Su4UZFWDARRcnwPjda9FqA0JpMk= golang.org/x/net v0.0.0-20220325170049-de3da57026de/go.mod h1:CfG3xpIq0wQ8r1q4Su4UZFWDARRcnwPjda9FqA0JpMk= golang.org/x/net v0.0.0-20220425223048-2871e0cb64e4/
(apisix) branch master updated (e40a9d18a -> 53661eaeb)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git from e40a9d18a chore: restore release/3.9 branch protection #11183 add 53661eaeb fix(cors): avoid overwriting `Access-Control-Expose-Headers` response header (#11136) No new revisions were added by this update. Summary of changes: apisix/plugins/cors.lua| 12 ++--- docs/en/latest/plugins/cors.md | 3 +- docs/zh/latest/plugins/cors.md | 3 +- t/plugin/cors.t| 2 +- t/plugin/cors3.t | 12 ++--- t/plugin/cors4.t | 110 + 6 files changed, 125 insertions(+), 17 deletions(-)
(apisix) branch release/3.8 updated: fix: add post request headers only if auth request method is post (#11174)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch release/3.8
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/release/3.8 by this push:
new 8944307db fix: add post request headers only if auth request method is
post (#11174)
8944307db is described below
commit 8944307db26a6d61fc6c4487b8f3d2c1bff74491
Author: YuanSheng Wang
AuthorDate: Mon Apr 22 18:55:16 2024 +0800
fix: add post request headers only if auth request method is post (#11174)
---
apisix/plugins/forward-auth.lua | 10 +-
t/plugin/forward-auth2.t| 185
t/plugin/grpc-web/package-lock.json | 4 +-
3 files changed, 194 insertions(+), 5 deletions(-)
diff --git a/apisix/plugins/forward-auth.lua b/apisix/plugins/forward-auth.lua
index 6d4454a58..efb2466ce 100644
--- a/apisix/plugins/forward-auth.lua
+++ b/apisix/plugins/forward-auth.lua
@@ -88,11 +88,15 @@ function _M.access(conf, ctx)
["X-Forwarded-Host"] = core.request.get_host(ctx),
["X-Forwarded-Uri"] = ctx.var.request_uri,
["X-Forwarded-For"] = core.request.get_remote_client_ip(ctx),
-["Expect"] = core.request.header(ctx, "expect"),
-["Content-Length"] = core.request.header(ctx, "content-length"),
-["Transfer-Encoding"] = core.request.header(ctx, "transfer-encoding")
}
+if conf.request_method == "POST" then
+auth_headers["Content-Length"] = core.request.header(ctx,
"content-length")
+auth_headers["Expect"] = core.request.header(ctx, "expect")
+auth_headers["Transfer-Encoding"] = core.request.header(ctx,
"transfer-encoding")
+auth_headers["Content-Encoding"] = core.request.header(ctx,
"content-encoding")
+end
+
-- append headers that need to be get from the client request header
if #conf.request_headers > 0 then
for _, header in ipairs(conf.request_headers) do
diff --git a/t/plugin/forward-auth2.t b/t/plugin/forward-auth2.t
new file mode 100644
index 0..f90841ede
--- /dev/null
+++ b/t/plugin/forward-auth2.t
@@ -0,0 +1,185 @@
+#
+# Licensed to the Apache Software Foundation (ASF) under one or more
+# contributor license agreements. See the NOTICE file distributed with
+# this work for additional information regarding copyright ownership.
+# The ASF licenses this file to You under the Apache License, Version 2.0
+# (the "License"); you may not use this file except in compliance with
+# the License. You may obtain a copy of the License at
+#
+# http://www.apache.org/licenses/LICENSE-2.0
+#
+# Unless required by applicable law or agreed to in writing, software
+# distributed under the License is distributed on an "AS IS" BASIS,
+# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+# See the License for the specific language governing permissions and
+# limitations under the License.
+#
+use t::APISIX 'no_plan';
+
+repeat_each(1);
+no_long_string();
+no_root_location();
+
+add_block_preprocessor(sub {
+my ($block) = @_;
+
+if (!defined $block->request) {
+$block->set_value("request", "GET /t");
+}
+});
+
+run_tests();
+
+__DATA__
+
+=== TEST 1: setup route with plugin
+--- config
+location /t {
+content_by_lua_block {
+local data = {
+{
+url = "/apisix/admin/upstreams/u1",
+data = [[{
+"nodes": {
+"127.0.0.1:1984": 1
+},
+"type": "roundrobin"
+}]],
+},
+{
+url = "/apisix/admin/routes/auth",
+data = {
+plugins = {
+["serverless-pre-function"] = {
+phase = "rewrite",
+functions = {
+[[return function(conf, ctx)
+local core = require("apisix.core");
+local token = "token-headers-test";
+if core.request.header(ctx,
"Authorization") == token then
+if core.request.get_method() ==
"POST" then
+if core.request.header(ctx,
"Content-Length") or
+core.request.header(ctx,
"Transfer-
(apisix) branch dependabot/go_modules/ci/pod/openfunction/function-example/test-body/golang.org/x/net-0.23.0 deleted (was a2d4506c9)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch dependabot/go_modules/ci/pod/openfunction/function-example/test-body/golang.org/x/net-0.23.0 in repository https://gitbox.apache.org/repos/asf/apisix.git was a2d4506c9 chore(deps): bump golang.org/x/net The revisions that were on this branch are still contained in other references; therefore, this change does not discard any commits from the repository.
(apisix) branch master updated: chore(deps): bump golang.org/x/net (#11169)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new 0cad3295d chore(deps): bump golang.org/x/net (#11169) 0cad3295d is described below commit 0cad3295d38de0270b5f8905fbee74a79fc5559c Author: dependabot[bot] <49699333+dependabot[bot]@users.noreply.github.com> AuthorDate: Mon Apr 22 11:23:28 2024 +0545 chore(deps): bump golang.org/x/net (#11169) --- .../openfunction/function-example/test-body/go.mod | 6 ++-- .../openfunction/function-example/test-body/go.sum | 34 -- 2 files changed, 34 insertions(+), 6 deletions(-) diff --git a/ci/pod/openfunction/function-example/test-body/go.mod b/ci/pod/openfunction/function-example/test-body/go.mod index bf571e0ba..41af08abd 100644 --- a/ci/pod/openfunction/function-example/test-body/go.mod +++ b/ci/pod/openfunction/function-example/test-body/go.mod @@ -19,9 +19,9 @@ require ( go.uber.org/atomic v1.9.0 // indirect go.uber.org/multierr v1.7.0 // indirect go.uber.org/zap v1.19.1 // indirect - golang.org/x/net v0.0.0-20211015210444-4f30a5c0130f // indirect - golang.org/x/sys v0.0.0-20211019181941-9d821ace8654 // indirect - golang.org/x/text v0.3.7 // indirect + golang.org/x/net v0.23.0 // indirect + golang.org/x/sys v0.18.0 // indirect + golang.org/x/text v0.14.0 // indirect google.golang.org/genproto v0.0.0-20210831024726-fe130286e0e2 // indirect google.golang.org/grpc v1.40.0 // indirect google.golang.org/protobuf v1.33.0 // indirect diff --git a/ci/pod/openfunction/function-example/test-body/go.sum b/ci/pod/openfunction/function-example/test-body/go.sum index f51a5304a..0e3260547 100644 --- a/ci/pod/openfunction/function-example/test-body/go.sum +++ b/ci/pod/openfunction/function-example/test-body/go.sum @@ -1094,6 +1094,7 @@ github.com/yuin/goldmark v1.1.30/go.mod h1:3hX8gzYuyVAZsxl0MRgGTJEmQBFcNTphYh9de github.com/yuin/goldmark v1.1.32/go.mod h1:3hX8gzYuyVAZsxl0MRgGTJEmQBFcNTphYh9decYSb74= github.com/yuin/goldmark v1.2.1/go.mod h1:3hX8gzYuyVAZsxl0MRgGTJEmQBFcNTphYh9decYSb74= github.com/yuin/goldmark v1.3.5/go.mod h1:mwnBkeHKe2W/ZEtQ+71ViKU8L12m81fl3OWwC1Zlc8k= +github.com/yuin/goldmark v1.4.13/go.mod h1:6yULJ656Px+3vBD8DxQVa3kxgyrAnzto9xy5taEt/CY= github.com/yuin/gopher-lua v0.0.0-20191220021717-ab39c6098bdb/go.mod h1:gqRgreBUhTSL0GeU64rtZ3Uq3wtjOa/TB2YfrtkCbVQ= github.com/yuin/gopher-lua v0.0.0-20200603152657-dc2b0ca8b37e/go.mod h1:gqRgreBUhTSL0GeU64rtZ3Uq3wtjOa/TB2YfrtkCbVQ= github.com/zenazn/goji v0.9.0/go.mod h1:7S9M489iMyHBNxwZnk9/EHS098H4/F6TATF2mIxtB1Q= @@ -1181,6 +1182,8 @@ golang.org/x/crypto v0.0.0-20210220033148-5ea612d1eb83/go.mod h1:jdWPYTVW3xRLrWP golang.org/x/crypto v0.0.0-20210314154223-e6e6c4f2bb5b/go.mod h1:T9bdIzuCu7OtxOm1hfPfRQxPLYneinmdGuTeoZ9dtd4= golang.org/x/crypto v0.0.0-20210513164829-c07d793c2f9a/go.mod h1:P+XmwS30IXTQdn5tA2iutPOUgjI07+tq3H3K9MVA1s8= golang.org/x/crypto v0.0.0-20210921155107-089bfa567519/go.mod h1:GvvjBRRGRdwPK5ydBHafDWAxML/pGHZbMvKqRZ5+Abc= +golang.org/x/crypto v0.19.0/go.mod h1:Iy9bg/ha4yyC70EfRS8jz+B6ybOBKMaSxLj6P6oBDfU= +golang.org/x/crypto v0.21.0/go.mod h1:0BP7YvVV9gBbVKyeTG0Gyn+gZm94bibOW5BjDEYAOMs= golang.org/x/exp v0.0.0-20190121172915-509febef88a4/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA= golang.org/x/exp v0.0.0-20190306152737-a1d7652674e8/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA= golang.org/x/exp v0.0.0-20190510132918-efd6b22b2522/go.mod h1:ZjyILWgesfNpC6sMxTJOJm9Kp84zZh5NQWvqDGG3Qr8= @@ -1218,6 +1221,8 @@ golang.org/x/mod v0.3.0/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= golang.org/x/mod v0.4.0/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= golang.org/x/mod v0.4.1/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= golang.org/x/mod v0.4.2/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= +golang.org/x/mod v0.6.0-dev.0.20220419223038-86c51ed26bb4/go.mod h1:jJ57K6gSWd91VN4djpZkiMVwK6gcyfeH4XE8wZrZaV4= +golang.org/x/mod v0.8.0/go.mod h1:iBbtSCu2XBx23ZKBPSOrRkjjQPZFPuis4dIYUhu/chs= golang.org/x/net v0.0.0-20180724234803-3673e40ba225/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= golang.org/x/net v0.0.0-20180826012351-8a410e7b638d/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= golang.org/x/net v0.0.0-20180906233101-161cd47e91fd/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= @@ -1280,8 +1285,13 @@ golang.org/x/net v0.0.0-20210525063256-abc453219eb5/go.mod h1:9nx3DQGgdP8bBQD5qx golang.org/x/net v0.0.0-20210610132358-84b48f89b13b/go.mod h1:9nx3DQGgdP8bBQD5qxJ1jj9UTztislL4KSBs9R2vV5Y= golang.org/x/net v0.0.0-20210614182718-04defd469f4e/go.mod h1:9nx3DQGgdP8bBQD5qxJ1jj9UTztislL4KSBs9R2vV5Y= golang.org/x/net v0.0.0-20210825183410-e898025ed96a/go.m
(apisix) branch master updated: chore(deps): bump golang.org/x/net (#11171)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new 8096caa77 chore(deps): bump golang.org/x/net (#11171) 8096caa77 is described below commit 8096caa775cd49ee2fcbcd2f4d2c832083b5387f Author: dependabot[bot] <49699333+dependabot[bot]@users.noreply.github.com> AuthorDate: Mon Apr 22 10:21:49 2024 +0545 chore(deps): bump golang.org/x/net (#11171) --- .../openfunction/function-example/test-uri/go.mod | 6 ++-- .../openfunction/function-example/test-uri/go.sum | 32 -- 2 files changed, 32 insertions(+), 6 deletions(-) diff --git a/ci/pod/openfunction/function-example/test-uri/go.mod b/ci/pod/openfunction/function-example/test-uri/go.mod index 046483f1e..444fbb65e 100644 --- a/ci/pod/openfunction/function-example/test-uri/go.mod +++ b/ci/pod/openfunction/function-example/test-uri/go.mod @@ -20,9 +20,9 @@ require ( go.uber.org/atomic v1.9.0 // indirect go.uber.org/multierr v1.7.0 // indirect go.uber.org/zap v1.21.0 // indirect - golang.org/x/net v0.0.0-20220621193019-9d032be2e588 // indirect - golang.org/x/sys v0.0.0-20220520151302-bc2c85ada10a // indirect - golang.org/x/text v0.3.7 // indirect + golang.org/x/net v0.23.0 // indirect + golang.org/x/sys v0.18.0 // indirect + golang.org/x/text v0.14.0 // indirect google.golang.org/genproto v0.0.0-20220622171453-ea41d75dfa0f // indirect google.golang.org/grpc v1.47.0 // indirect google.golang.org/protobuf v1.33.0 // indirect diff --git a/ci/pod/openfunction/function-example/test-uri/go.sum b/ci/pod/openfunction/function-example/test-uri/go.sum index 7aaa3ce33..7c6d60879 100644 --- a/ci/pod/openfunction/function-example/test-uri/go.sum +++ b/ci/pod/openfunction/function-example/test-uri/go.sum @@ -1656,6 +1656,7 @@ github.com/yuin/goldmark v1.2.1/go.mod h1:3hX8gzYuyVAZsxl0MRgGTJEmQBFcNTphYh9dec github.com/yuin/goldmark v1.3.5/go.mod h1:mwnBkeHKe2W/ZEtQ+71ViKU8L12m81fl3OWwC1Zlc8k= github.com/yuin/goldmark v1.4.0/go.mod h1:mwnBkeHKe2W/ZEtQ+71ViKU8L12m81fl3OWwC1Zlc8k= github.com/yuin/goldmark v1.4.1/go.mod h1:mwnBkeHKe2W/ZEtQ+71ViKU8L12m81fl3OWwC1Zlc8k= +github.com/yuin/goldmark v1.4.13/go.mod h1:6yULJ656Px+3vBD8DxQVa3kxgyrAnzto9xy5taEt/CY= github.com/yuin/gopher-lua v0.0.0-20191220021717-ab39c6098bdb/go.mod h1:gqRgreBUhTSL0GeU64rtZ3Uq3wtjOa/TB2YfrtkCbVQ= github.com/yuin/gopher-lua v0.0.0-20200603152657-dc2b0ca8b37e/go.mod h1:gqRgreBUhTSL0GeU64rtZ3Uq3wtjOa/TB2YfrtkCbVQ= github.com/yvasiyarov/go-metrics v0.0.0-20140926110328-57bccd1ccd43/go.mod h1:aX5oPXxHm3bOH+xeAttToC8pqch2ScQN/JoXYupl6xs= @@ -1813,6 +1814,8 @@ golang.org/x/crypto v0.0.0-20211215153901-e495a2d5b3d3/go.mod h1:IxCIyHEi3zRg3s0 golang.org/x/crypto v0.0.0-20220112180741-5e0467b6c7ce/go.mod h1:IxCIyHEi3zRg3s0A5j5BB6A9Jmi73HwBIUl50j+osU4= golang.org/x/crypto v0.0.0-20220131195533-30dcbda58838/go.mod h1:IxCIyHEi3zRg3s0A5j5BB6A9Jmi73HwBIUl50j+osU4= golang.org/x/crypto v0.0.0-20220511200225-c6db032c6c88/go.mod h1:IxCIyHEi3zRg3s0A5j5BB6A9Jmi73HwBIUl50j+osU4= +golang.org/x/crypto v0.19.0/go.mod h1:Iy9bg/ha4yyC70EfRS8jz+B6ybOBKMaSxLj6P6oBDfU= +golang.org/x/crypto v0.21.0/go.mod h1:0BP7YvVV9gBbVKyeTG0Gyn+gZm94bibOW5BjDEYAOMs= golang.org/x/exp v0.0.0-20180321215751-8460e604b9de/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA= golang.org/x/exp v0.0.0-20180807140117-3d87b88a115f/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA= golang.org/x/exp v0.0.0-20190121172915-509febef88a4/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA= @@ -1855,6 +1858,8 @@ golang.org/x/mod v0.4.1/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= golang.org/x/mod v0.4.2/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA= golang.org/x/mod v0.5.0/go.mod h1:5OXOZSfqPIIbmVBIIKWRFfZjPR0E5r58TLhUjH0a2Ro= golang.org/x/mod v0.5.1/go.mod h1:5OXOZSfqPIIbmVBIIKWRFfZjPR0E5r58TLhUjH0a2Ro= +golang.org/x/mod v0.6.0-dev.0.20220419223038-86c51ed26bb4/go.mod h1:jJ57K6gSWd91VN4djpZkiMVwK6gcyfeH4XE8wZrZaV4= +golang.org/x/mod v0.8.0/go.mod h1:iBbtSCu2XBx23ZKBPSOrRkjjQPZFPuis4dIYUhu/chs= golang.org/x/net v0.0.0-20180530234432-1e491301e022/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= golang.org/x/net v0.0.0-20180724234803-3673e40ba225/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= golang.org/x/net v0.0.0-20180826012351-8a410e7b638d/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4= @@ -1939,8 +1944,13 @@ golang.org/x/net v0.0.0-20220127200216-cd36cc0744dd/go.mod h1:CfG3xpIq0wQ8r1q4Su golang.org/x/net v0.0.0-20220225172249-27dd8689420f/go.mod h1:CfG3xpIq0wQ8r1q4Su4UZFWDARRcnwPjda9FqA0JpMk= golang.org/x/net v0.0.0-20220325170049-de3da57026de/go.mod h1:CfG3xpIq0wQ8r1q4Su4UZFWDARRcnwPjda9FqA0JpMk= golang.org/x/net v0.0.0-20220425223048-2871e0cb64e4/
(apisix) branch master updated: fix: close session in case of error to avoid blocked session (#11089)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 07b3cc3f6 fix: close session in case of error to avoid blocked session
(#11089)
07b3cc3f6 is described below
commit 07b3cc3f63db8fc4ae3706baa324a76ee3049338
Author: Markus
AuthorDate: Mon Apr 22 06:02:55 2024 +0200
fix: close session in case of error to avoid blocked session (#11089)
---
apisix/plugins/openid-connect.lua | 3 ++
t/plugin/openid-connect5.t| 93 +++
2 files changed, 96 insertions(+)
diff --git a/apisix/plugins/openid-connect.lua
b/apisix/plugins/openid-connect.lua
index c3d79fa45..db8d01bfb 100644
--- a/apisix/plugins/openid-connect.lua
+++ b/apisix/plugins/openid-connect.lua
@@ -571,6 +571,9 @@ function _M.rewrite(plugin_conf, ctx)
response, err, _, session = openidc.authenticate(conf, nil,
unauth_action, conf.session)
if err then
+if session then
+session:close()
+end
if err == "unauthorized request" then
if conf.unauth_action == "pass" then
return nil
diff --git a/t/plugin/openid-connect5.t b/t/plugin/openid-connect5.t
index a506a3180..53d16edb1 100644
--- a/t/plugin/openid-connect5.t
+++ b/t/plugin/openid-connect5.t
@@ -138,3 +138,96 @@ __DATA__
}
--- response_body_like
hello world
+
+
+
+=== TEST 2: Call to route with locking session storage, no authentication and
unauth_action 'deny' should not block subsequent requests on same session
+--- config
+set $session_storage redis;
+set $session_redis_uselocking on;
+
+location /t {
+content_by_lua_block {
+local t = require("lib.test_admin").test
+local http = require "resty.http"
+local login_keycloak = require("lib.keycloak").login_keycloak
+local concatenate_cookies =
require("lib.keycloak").concatenate_cookies
+
+local code, body = t('/apisix/admin/routes/1',
+ ngx.HTTP_PUT,
+ [[{
+"plugins": {
+"openid-connect": {
+"discovery":
"http://127.0.0.1:8080/realms/University/.well-known/openid-configuration";,
+"realm": "University",
+"client_id": "course_management",
+"client_secret":
"d1ec69e9-55d2-4109-a3ea-befa071579d5",
+"redirect_uri": "http://127.0.0.1:]] ..
ngx.var.server_port .. [[/authenticated",
+"ssl_verify": false,
+"unauth_action": "deny"
+}
+},
+"upstream": {
+"nodes": {
+"127.0.0.1:1980": 1
+},
+"type": "roundrobin"
+},
+"uri": "/*"
+}]]
+)
+
+local uri = "http://127.0.0.1:"; .. ngx.var.server_port .. "/hello"
+
+-- Make the final call to protected route WITHOUT cookie
+local httpc = http.new()
+local res, err = httpc:request_uri(uri, {method = "GET"})
+
+-- Extract cookie which is not authenticated
+local cookie_str = concatenate_cookies(res.headers['Set-Cookie'])
+
+-- Make the call to protected route with cookie
+local function firstRequest()
+ local httpc = http.new()
+
+ local res, err = httpc:request_uri(uri, {
+method = "GET",
+headers = {
+["Cookie"] = cookie_str
+}
+})
+
+if not res then
+ngx.log(ngx.ERR, "request failed with err: ", err)
+return
+end
+return res
+end
+
+local thread = ngx.thread.spawn(firstRequest)
+ok, res = ngx.thread.wait(thread)
+
+if not ok then
+ngx.log(ngx.ERR, "First request did not complete: ", res)
+return
+end
+
+if res.status ~= 401 then
+ngx.log(ngx.ERR, "Expected statu
(apisix) branch master updated: chore(deps): bump apache/skywalking-eyes from 0.5.0 to 0.6.0 (#11128)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 1dfce2b73 chore(deps): bump apache/skywalking-eyes from 0.5.0 to 0.6.0
(#11128)
1dfce2b73 is described below
commit 1dfce2b731ddea1abda9eda25ff412b6caafb913
Author: dependabot[bot] <49699333+dependabot[bot]@users.noreply.github.com>
AuthorDate: Fri Apr 12 18:14:22 2024 +0545
chore(deps): bump apache/skywalking-eyes from 0.5.0 to 0.6.0 (#11128)
---
.github/workflows/license-checker.yml | 2 +-
1 file changed, 1 insertion(+), 1 deletion(-)
diff --git a/.github/workflows/license-checker.yml
b/.github/workflows/license-checker.yml
index 830f1a180..bae5d6c77 100644
--- a/.github/workflows/license-checker.yml
+++ b/.github/workflows/license-checker.yml
@@ -32,6 +32,6 @@ jobs:
steps:
- uses: actions/checkout@v4
- name: Check License Header
-uses: apache/skywalking-eyes@v0.5.0
+uses: apache/skywalking-eyes@v0.6.0
env:
GITHUB_TOKEN: ${{ secrets.GITHUB_TOKEN }}
(apisix) branch master updated: fix(kafka-pubsub): restore `pb.state` appropriately (#11135)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new c7c70e4b3 fix(kafka-pubsub): restore `pb.state` appropriately (#11135)
c7c70e4b3 is described below
commit c7c70e4b392b0e7ff8b69fae78978a96cf19ffa0
Author: Abhishek Choudhary
AuthorDate: Wed Apr 10 23:08:01 2024 +0545
fix(kafka-pubsub): restore `pb.state` appropriately (#11135)
---
apisix/core/pubsub.lua | 12
t/pubsub/kafka.t | 3 +++
2 files changed, 11 insertions(+), 4 deletions(-)
diff --git a/apisix/core/pubsub.lua b/apisix/core/pubsub.lua
index 18bb88700..5b36b0cc9 100644
--- a/apisix/core/pubsub.lua
+++ b/apisix/core/pubsub.lua
@@ -66,6 +66,10 @@ end
-- send generic response to client
local function send_resp(ws, sequence, data)
data.sequence = sequence
+-- only restore state if it has changed
+if pb_state ~= pb.state() then
+pb.state(pb_state)
+end
local ok, encoded = pcall(pb.encode, "PubSubResp", data)
if not ok or not encoded then
log.error("failed to encode response message, err: ", encoded)
@@ -184,11 +188,11 @@ function _M.wait(self)
goto continue
end
--- recovery of stored pb_store
-local pb_old_state = pb.state(pb_state)
-
+-- only recover state if it has changed
+if pb.state() ~= pb_state then
+pb.state(pb_state)
+end
local data, err = pb.decode("PubSubReq", raw_data)
-pb.state(pb_old_state)
if not data then
log.error("pubsub server receives undecodable data, err: ", err)
send_error(ws, 0, "wrong command")
diff --git a/t/pubsub/kafka.t b/t/pubsub/kafka.t
index b61af6f0c..b779a4846 100644
--- a/t/pubsub/kafka.t
+++ b/t/pubsub/kafka.t
@@ -159,6 +159,7 @@ failed to initialize pubsub module, err: bad "upgrade"
request header: nil
# script that prepares the CI environment
location /t {
content_by_lua_block {
+local pb = require("pb")
local lib_pubsub = require("lib.pubsub")
local test_pubsub = lib_pubsub.new_ws("ws://127.0.0.1:1984/kafka")
local data = {
@@ -235,6 +236,8 @@ failed to initialize pubsub module, err: bad "upgrade"
request header: nil
}
for i = 1, #data do
+-- force clear state
+pb.state(nil)
local data = test_pubsub:send_recv_ws_binary(data[i])
if data.error_resp then
ngx.say(data.sequence..data.error_resp.message)
(apisix) branch master updated: fix: add post request headers only if auth request method is post (#11021)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 4df549c21 fix: add post request headers only if auth request method is
post (#11021)
4df549c21 is described below
commit 4df549c21278fbb99a1efba160b2ac9119ce4e1f
Author: Surya <3763515+suryaprabhak...@users.noreply.github.com>
AuthorDate: Mon Apr 8 21:32:16 2024 +0530
fix: add post request headers only if auth request method is post (#11021)
---
apisix/plugins/forward-auth.lua | 10 ++-
t/plugin/forward-auth2.t| 185
2 files changed, 192 insertions(+), 3 deletions(-)
diff --git a/apisix/plugins/forward-auth.lua b/apisix/plugins/forward-auth.lua
index 69dc48de6..95f04994c 100644
--- a/apisix/plugins/forward-auth.lua
+++ b/apisix/plugins/forward-auth.lua
@@ -89,11 +89,15 @@ function _M.access(conf, ctx)
["X-Forwarded-Host"] = core.request.get_host(ctx),
["X-Forwarded-Uri"] = ctx.var.request_uri,
["X-Forwarded-For"] = core.request.get_remote_client_ip(ctx),
-["Expect"] = core.request.header(ctx, "expect"),
-["Content-Length"] = core.request.header(ctx, "content-length"),
-["Transfer-Encoding"] = core.request.header(ctx, "transfer-encoding")
}
+if conf.request_method == "POST" then
+auth_headers["Content-Length"] = core.request.header(ctx,
"content-length")
+auth_headers["Expect"] = core.request.header(ctx, "expect")
+auth_headers["Transfer-Encoding"] = core.request.header(ctx,
"transfer-encoding")
+auth_headers["Content-Encoding"] = core.request.header(ctx,
"content-encoding")
+end
+
-- append headers that need to be get from the client request header
if #conf.request_headers > 0 then
for _, header in ipairs(conf.request_headers) do
diff --git a/t/plugin/forward-auth2.t b/t/plugin/forward-auth2.t
new file mode 100644
index 0..f90841ede
--- /dev/null
+++ b/t/plugin/forward-auth2.t
@@ -0,0 +1,185 @@
+#
+# Licensed to the Apache Software Foundation (ASF) under one or more
+# contributor license agreements. See the NOTICE file distributed with
+# this work for additional information regarding copyright ownership.
+# The ASF licenses this file to You under the Apache License, Version 2.0
+# (the "License"); you may not use this file except in compliance with
+# the License. You may obtain a copy of the License at
+#
+# http://www.apache.org/licenses/LICENSE-2.0
+#
+# Unless required by applicable law or agreed to in writing, software
+# distributed under the License is distributed on an "AS IS" BASIS,
+# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+# See the License for the specific language governing permissions and
+# limitations under the License.
+#
+use t::APISIX 'no_plan';
+
+repeat_each(1);
+no_long_string();
+no_root_location();
+
+add_block_preprocessor(sub {
+my ($block) = @_;
+
+if (!defined $block->request) {
+$block->set_value("request", "GET /t");
+}
+});
+
+run_tests();
+
+__DATA__
+
+=== TEST 1: setup route with plugin
+--- config
+location /t {
+content_by_lua_block {
+local data = {
+{
+url = "/apisix/admin/upstreams/u1",
+data = [[{
+"nodes": {
+"127.0.0.1:1984": 1
+},
+"type": "roundrobin"
+}]],
+},
+{
+url = "/apisix/admin/routes/auth",
+data = {
+plugins = {
+["serverless-pre-function"] = {
+phase = "rewrite",
+functions = {
+[[return function(conf, ctx)
+local core = require("apisix.core");
+local token = "token-headers-test";
+if core.request.header(ctx,
"Authorization") == token then
+if core.request.get_method() ==
"POST" then
+if core.request.header(ctx,
"Content-Length") or
+core.request.header(ctx,
"Tra
(apisix-website) branch master updated: blog: add monthly-report.md (#1784)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix-website.git The following commit(s) were added to refs/heads/master by this push: new 4cfdd61f2c6 blog: add monthly-report.md (#1784) 4cfdd61f2c6 is described below commit 4cfdd61f2c6b0a1d1a0f214979abd733317fcc57 Author: Yilia Lin <114121331+yilial...@users.noreply.github.com> AuthorDate: Tue Apr 2 16:57:59 2024 +0800 blog: add monthly-report.md (#1784) --- blog/en/blog/2024/04/01/monthly-report.md | 37 +++ blog/zh/blog/2024/04/01/monthly-report.md | 36 ++ 2 files changed, 73 insertions(+) diff --git a/blog/en/blog/2024/04/01/monthly-report.md b/blog/en/blog/2024/04/01/monthly-report.md new file mode 100644 index 000..1d4add6c65c --- /dev/null +++ b/blog/en/blog/2024/04/01/monthly-report.md @@ -0,0 +1,37 @@ +--- +title: "Monthly Report (March 01 - March 31)" +keywords: ["Apache APISIX", "API Gateway", "Monthly Report", "Contributor"] +description: Our monthly Apache APISIX community report is your window into the project's monthly developments. It is a tool to facilitate your seamless integration into the Apache APISIX community, ensuring that you stay well-informed and actively involved. +tags: [Community] +image: https://static.apiseven.com/uploads/2024/04/01/5Uvc7aZb_en-cover-202403.png +--- + +> We have recently made some additions and improvements to specific features within Apache APISIX. For detailed information, please read the monthly report. + +## Introduction + +From its inception, the Apache APISIX project has embraced the ethos of open-source community collaboration, propelling it into the ranks of the most active global open-source API gateway projects. The proverbial wisdom of 'Many hands make light work' rings true in our way, made possible by the collective dedication of our community. + +From 03.01 to 03.31, a total of 18 contributors made 48 commits to Apache APISIX. We sincerely appreciate your contributions to Apache APISIX. + +## Contributor Statistics + +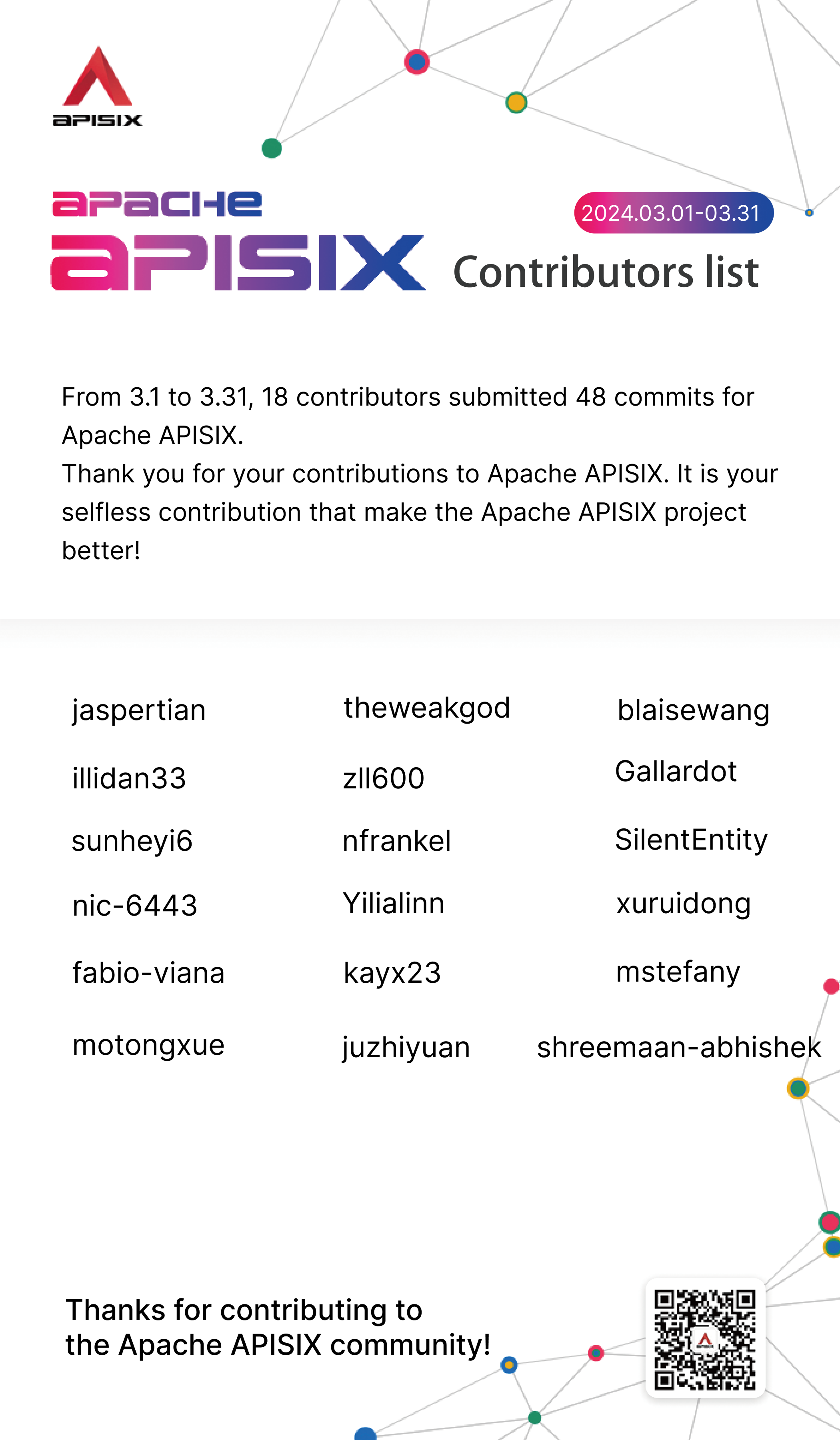 + + + +## Recent Highlights Features + +- [Support more sensitive fields for encryption](https://github.com/apache/apisix/pull/11095)(Contributor: [shreemaan-abhishek](https://github.com/shreemaan-abhishek)) + +- [Enable sensitive fields encryption by default](https://github.com/apache/apisix/pull/11076)(Contributor: [shreemaan-abhishek](https://github.com/shreemaan-abhishek)) + +- [Release 3.9.0](https://github.com/apache/apisix/pull/11061)(Contributor: [shreemaan-abhishek](https://github.com/shreemaan-abhishek)) + +- [Update lua-resty-t1k to 1.1.3 for chaitin-waf plugin](https://github.com/apache/apisix/pull/11029)(Contributor: [blaisewang](https://github.com/blaisewang)) + +- [Support to enable quic](https://github.com/apache/apisix/pull/10989)(Contributor: [zll600](https://github.com/zll600)) + +- [Add session.cookie configuration for openid-conect plugin](https://github.com/apache/apisix/pull/10919)(Contributor: [illidan33](https://github.com/illidan33)) + +The official website and GitHub Issues of Apache APISIX have accumulated rich documentation tutorials and usage experiences. If you encounter any issues, you can refer to the documentation, search for keywords in Issues, or participate in discussions on Issues to share your ideas and practical experiences. diff --git a/blog/zh/blog/2024/04/01/monthly-report.md b/blog/zh/blog/2024/04/01/monthly-report.md new file mode 100644 index 000..7dbe86598f5 --- /dev/null +++ b/blog/zh/blog/2024/04/01/monthly-report.md @@ -0,0 +1,36 @@ +--- +title: "社区月报 (03.01 - 03.31)" +keywords: ["Apache APISIX", "API 网关", "社区月报", "贡献者"] +description: Apache APISIX 社区的月报旨在帮助社区成员更全面地了解社区的最新动态,方便大家参与到 Apache APISIX 社区中来。 +tags: [Community] +image: https://static.apiseven.com/uploads/2024/04/01/VaWBqFRY_cn-cover-202403.png +--- +> 最近,我们新增并改进了 Apache APISIX 的部分功能,如支持加密更多敏感字段、支持 QUIC 协议和支持在 openid-connect 插件中设置 session cookie 生命周期等。有关更多功能新亮点,请阅读本期月报。 + +## 导语 + +Apache APISIX 项目始终秉承着开源社区协作的精神,自问世起便崭露头角,如今已经成为全球最活跃的开源 API 网关项目之一。正如谚语所言,“众人拾柴火焰高”,这一辉煌成就,得益于整个社区伙伴的协同努力。 + +从 2024.03.01 至 2024.03.31,有 18 名开发者提交了 48 个 commit,为 Apache APISIX 做出了重要贡献。感谢这些伙伴们对 Apache APISIX 的无私支持!正是因为你们的付出,才能让 Apache APISIX 项目不断改进、提升和壮大。 + +## 贡献者统计 + + + + + +## 近期亮点功能 + +- [支持加密更多敏感字段](https:/
(apisix-docker) branch release/apisix-3.9.0 created (now 5c2d8f4)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/apisix-3.9.0 in repository https://gitbox.apache.org/repos/asf/apisix-docker.git at 5c2d8f4 chore: release APISIX 3.9.0 (#549) No new revisions were added by this update.
(apisix-docker) branch master updated: chore: release APISIX 3.9.0 (#549)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix-docker.git
The following commit(s) were added to refs/heads/master by this push:
new 5c2d8f4 chore: release APISIX 3.9.0 (#549)
5c2d8f4 is described below
commit 5c2d8f4e3f9e54bf1ee6453efbd24dec5a8e9672
Author: Abhishek Choudhary
AuthorDate: Mon Apr 1 15:16:07 2024 +0545
chore: release APISIX 3.9.0 (#549)
---
.github/workflows/apisix-docker-example-test-standalone.yaml | 2 +-
.github/workflows/apisix-docker-example-test.yaml| 2 +-
.github/workflows/apisix_push_docker_hub.yaml| 2 +-
Makefile | 4 ++--
all-in-one/apisix-dashboard/Dockerfile | 7 +--
debian/Dockerfile| 2 +-
docs/en/latest/build.md | 2 +-
example/docker-compose-arm64.yml | 2 +-
example/docker-compose-standalone.yml| 2 +-
example/docker-compose.yml | 2 +-
redhat/Dockerfile| 2 +-
11 files changed, 12 insertions(+), 17 deletions(-)
diff --git a/.github/workflows/apisix-docker-example-test-standalone.yaml
b/.github/workflows/apisix-docker-example-test-standalone.yaml
index 229f3c3..140c102 100644
--- a/.github/workflows/apisix-docker-example-test-standalone.yaml
+++ b/.github/workflows/apisix-docker-example-test-standalone.yaml
@@ -14,7 +14,7 @@ on:
- 'release/apisix-2.15.**'
env:
- APISIX_VERSION: "3.8.0"
+ APISIX_VERSION: "3.9.0"
jobs:
prepare:
diff --git a/.github/workflows/apisix-docker-example-test.yaml
b/.github/workflows/apisix-docker-example-test.yaml
index c508a45..3f11473 100644
--- a/.github/workflows/apisix-docker-example-test.yaml
+++ b/.github/workflows/apisix-docker-example-test.yaml
@@ -14,7 +14,7 @@ on:
- 'release/apisix-2.15.**'
env:
- APISIX_VERSION: "3.8.0"
+ APISIX_VERSION: "3.9.0"
jobs:
prepare:
diff --git a/.github/workflows/apisix_push_docker_hub.yaml
b/.github/workflows/apisix_push_docker_hub.yaml
index 799af83..f0f05a3 100644
--- a/.github/workflows/apisix_push_docker_hub.yaml
+++ b/.github/workflows/apisix_push_docker_hub.yaml
@@ -13,7 +13,7 @@ jobs:
- debian
- redhat
env:
- APISIX_DOCKER_TAG: 3.8.0-${{ matrix.platform }}
+ APISIX_DOCKER_TAG: 3.9.0-${{ matrix.platform }}
steps:
- name: Check out the repo
diff --git a/Makefile b/Makefile
index 8bb88c1..0fd06a7 100644
--- a/Makefile
+++ b/Makefile
@@ -21,8 +21,8 @@ SHELL := bash
# APISIX ARGS
-APISIX_VERSION ?= 3.8.0
-MAX_APISIX_VERSION ?= 3.8.0
+APISIX_VERSION ?= 3.9.0
+MAX_APISIX_VERSION ?= 3.9.0
IMAGE_NAME = apache/apisix
IMAGE_TAR_NAME = apache_apisix
APISIX_REPO = https://github.com/apache/apisix
diff --git a/all-in-one/apisix-dashboard/Dockerfile
b/all-in-one/apisix-dashboard/Dockerfile
index 7daa82a..bf906d0 100644
--- a/all-in-one/apisix-dashboard/Dockerfile
+++ b/all-in-one/apisix-dashboard/Dockerfile
@@ -21,7 +21,7 @@ ARG APISIX_VERSION=master
ARG APISIX_DASHBOARD_VERSION=master
# Build Apache APISIX
-FROM openresty/openresty:1.21.4.2-alpine-fat AS production-stage
+FROM openresty/openresty:1.25.3.1-2-alpine-fat AS production-stage
ARG APISIX_VERSION
ARG ENABLE_PROXY
@@ -42,11 +42,6 @@ RUN set -x \
&& luarocks config variables.OPENSSL_LIBDIR
/usr/local/openresty/openssl/lib \
&& luarocks config variables.OPENSSL_INCDIR
/usr/local/openresty/openssl/include \
&& git config --global url.https://github.com/.insteadOf git://github.com/
\
-&& curl --proto '=https' --tlsv1.2 -sSf https://sh.rustup.rs | sudo sh -s
-- -y \
-&& source "$HOME/.cargo/env" \
-&& export CARGO_REGISTRIES_CRATES_IO_PROTOCOL=sparse \
-# next line is for rust cdylib compile on musl
-&& export RUSTFLAGS="-C target-feature=-crt-static" \
&& luarocks install
https://raw.githubusercontent.com/apache/apisix/master/apisix-master-0.rockspec
--tree=/usr/local/apisix/deps PCRE_DIR=/usr/local/openresty/pcre \
&& cp -v
/usr/local/apisix/deps/lib/luarocks/rocks-5.1/apisix/${APISIX_VERSION}-0/bin/apisix
/usr/bin/ \
&& (if [ "$APISIX_VERSION" = "master" ] || [ "$APISIX_VERSION" \> "2.2" ];
then echo 'use shell ';else bin='#!
/usr/local/openresty/luajit/bin/luajit\npackage.path =
"/usr/local/apisix/?.lua;" .. package.path'; sed -i "1s@.*@$bin@"
/usr/bin/apisix ; fi;) \
diff --git a/debian/Dockerfile b/debian/Dockerfile
index 818e28a..c380951 100644
--- a/debian/Dockerfile
+++ b/de
(apisix-website) branch master updated: doc: release APISIX 3.9.0 (#1780)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix-website.git
The following commit(s) were added to refs/heads/master by this push:
new c3460cc520d doc: release APISIX 3.9.0 (#1780)
c3460cc520d is described below
commit c3460cc520de98a34ff42f460c2f3c61c65dd5e1
Author: Abhishek Choudhary
AuthorDate: Mon Apr 1 13:38:58 2024 +0545
doc: release APISIX 3.9.0 (#1780)
---
config/apisix-versions.js | 2 +-
config/docs.js| 4 ++--
config/downloads.js | 6 +++---
3 files changed, 6 insertions(+), 6 deletions(-)
diff --git a/config/apisix-versions.js b/config/apisix-versions.js
index 538856c8896..a757d157c0e 100644
--- a/config/apisix-versions.js
+++ b/config/apisix-versions.js
@@ -3,7 +3,7 @@
/**
* @type {Array} version list
*/
-const versions = ['2.13', '2.14', '2.15', '3.0', '3.1', '3.2', '3.3', '3.4',
'3.5', '3.6', '3.7', '3.8'];
+const versions = ['2.13', '2.14', '2.15', '3.0', '3.1', '3.2', '3.3', '3.4',
'3.5', '3.6', '3.7', '3.8', '3.9'];
/**
* @type {Array} LTS version list
diff --git a/config/docs.js b/config/docs.js
index 3baedba83e7..7ef18d563ab 100644
--- a/config/docs.js
+++ b/config/docs.js
@@ -6,8 +6,8 @@ module.exports = [
shape: 'triangle',
color: '#e8433e',
githubRepo: 'apache/apisix',
-version: '3.8.0',
-releaseDate: '2024-01-15',
+version: '3.9.0',
+releaseDate: '2024-03-29',
firstDocPath: '/getting-started',
},
{
diff --git a/config/downloads.js b/config/downloads.js
index ee4a619c893..b47d09253fe 100644
--- a/config/downloads.js
+++ b/config/downloads.js
@@ -7,12 +7,12 @@ module.exports = [
color: '#e8433e',
githubRepo: 'apache/apisix',
githubBranch: 'master',
-downloadPath: 'apisix/3.8.0/apache-apisix-3.8.0-src',
+downloadPath: 'apisix/3.9.0/apache-apisix-3.9.0-src',
dockerhubPath: 'apisix',
-version: '3.8.0',
+version: '3.9.0',
LTSDownloadPath: 'apisix/3.2.2/apache-apisix-3.2.2-src',
LTSVersion: '3.2.2',
-releaseDate: '2024-01-15',
+releaseDate: '2024-03-29',
firstDocPath: '/getting-started',
},
{
(apisix) branch master updated: brotli partial response fix (#11087)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new 531950329 brotli partial response fix (#11087) 531950329 is described below commit 5319503293c41cf41a2caa5cb944a12d40686c83 Author: Silent AuthorDate: Fri Mar 29 21:55:08 2024 +0530 brotli partial response fix (#11087) --- apisix/plugins/brotli.lua | 3 ++- 1 file changed, 2 insertions(+), 1 deletion(-) diff --git a/apisix/plugins/brotli.lua b/apisix/plugins/brotli.lua index 4482fc0cd..031bd8ea9 100644 --- a/apisix/plugins/brotli.lua +++ b/apisix/plugins/brotli.lua @@ -239,7 +239,8 @@ function _M.body_filter(conf, ctx) end if eof then -ngx.arg[1] = ctx.compressor:finish() +-- overwriting the arg[1], results into partial response +ngx.arg[1] = ngx.arg[1] .. ctx.compressor:finish() end end
(apisix) branch master updated: feat: support more sensitive fields for encryption (#11095)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new a7a5a2be5 feat: support more sensitive fields for encryption (#11095)
a7a5a2be5 is described below
commit a7a5a2be54bc252f0ff2492928c2643710cbefad
Author: Abhishek Choudhary
AuthorDate: Fri Mar 29 09:57:34 2024 +0545
feat: support more sensitive fields for encryption (#11095)
---
apisix/plugins/jwe-decrypt.lua| 30 +
apisix/plugins/openid-connect.lua | 2 +-
apisix/plugins/openwhisk.lua | 3 +-
t/plugin/jwe-decrypt.t| 66
t/plugin/openid-connect.t | 91 ---
t/plugin/openwhisk.t | 52 +++---
6 files changed, 163 insertions(+), 81 deletions(-)
diff --git a/apisix/plugins/jwe-decrypt.lua b/apisix/plugins/jwe-decrypt.lua
index 0e4447e02..b0d1e16f6 100644
--- a/apisix/plugins/jwe-decrypt.lua
+++ b/apisix/plugins/jwe-decrypt.lua
@@ -51,6 +51,7 @@ local consumer_schema = {
is_base64_encoded = { type = "boolean" },
},
required = { "key", "secret" },
+encrypt_fields = { "key", "secret" },
}
@@ -71,15 +72,26 @@ function _M.check_schema(conf, schema_type)
return false, err
end
--- restrict the length of secret, we use A256GCM for encryption,
--- so the length should be 32 chars only
-if conf.is_base64_encoded then
-if #base64.decode_base64url(conf.secret) ~= 32 then
- return false, "the secret length after base64 decode should
be 32 chars"
-end
-else
-if #conf.secret ~= 32 then
-return false, "the secret length should be 32 chars"
+local local_conf, err = core.config.local_conf(true)
+if not local_conf then
+return false, "failed to load the configuration file: " .. err
+end
+
+local encrypted = core.table.try_read_attr(local_conf, "apisix",
"data_encryption",
+"enable_encrypt_fields") and (core.config.type == "etcd")
+
+-- if encrypted, the secret length will exceed 32 so don't check
+if not encrypted then
+-- restrict the length of secret, we use A256GCM for encryption,
+-- so the length should be 32 chars only
+if conf.is_base64_encoded then
+if #base64.decode_base64url(conf.secret) ~= 32 then
+return false, "the secret length after base64 decode
should be 32 chars"
+end
+else
+if #conf.secret ~= 32 then
+return false, "the secret length should be 32 chars"
+end
end
end
diff --git a/apisix/plugins/openid-connect.lua
b/apisix/plugins/openid-connect.lua
index 435cf6363..da334ebfb 100644
--- a/apisix/plugins/openid-connect.lua
+++ b/apisix/plugins/openid-connect.lua
@@ -268,7 +268,7 @@ local schema = {
}
}
},
-encrypt_fields = {"client_secret"},
+encrypt_fields = {"client_secret", "client_rsa_private_key"},
required = {"client_id", "client_secret", "discovery"}
}
diff --git a/apisix/plugins/openwhisk.lua b/apisix/plugins/openwhisk.lua
index 7043f14f5..718513adc 100644
--- a/apisix/plugins/openwhisk.lua
+++ b/apisix/plugins/openwhisk.lua
@@ -49,7 +49,8 @@ local schema = {
keepalive_timeout = {type = "integer", minimum = 1000, default =
6},
keepalive_pool = {type = "integer", minimum = 1, default = 5}
},
-required = {"api_host", "service_token", "namespace", "action"}
+required = {"api_host", "service_token", "namespace", "action"},
+encrypt_fields = {"service_token"}
}
diff --git a/t/plugin/jwe-decrypt.t b/t/plugin/jwe-decrypt.t
index e7fcf7756..af2af3291 100644
--- a/t/plugin/jwe-decrypt.t
+++ b/t/plugin/jwe-decrypt.t
@@ -95,6 +95,10 @@ done
=== TEST 4: secret length too long
+--- yaml_config
+apisix:
+ data_encryption:
+enable_encrypt_fields: false
--- config
location /t {
content_by_lua_block {
@@ -115,6 +119,10 @@ done
=== TEST 5: secret length too long(base64 encode)
+--- yaml_config
+apisix:
+ data_encryption:
+enable_encrypt_fields: false
--- config
location /t {
content_by_lua_block {
@@ -163,7 +171,27 @@ passed
-=== TEST 7: enable jwe-decrypt plugin using admin api
+=== TEST 7: verify encrypted field
+--- config
+location /t {
+content_by_lua_block
(apisix) branch master updated (538b9480f -> cca94f103)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git from 538b9480f docs: correct consumer restriction type (#11082) add cca94f103 feat: enable sensitive fields encryption by default (#11076) No new revisions were added by this update. Summary of changes: apisix/plugin.lua | 2 +- conf/config-default.yaml | 2 +- t/admin/consumers.t| 2 +- t/node/chash-hashon.t | 4 ++-- t/plugin/error-log-logger-clickhouse.t | 4 ++-- t/plugin/key-auth.t| 13 + 6 files changed, 20 insertions(+), 7 deletions(-)
(apisix) tag 3.9.0 created (now 9bcabaf12)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to tag 3.9.0 in repository https://gitbox.apache.org/repos/asf/apisix.git at 9bcabaf12 (commit) No new revisions were added by this update.
(apisix) branch master updated: fix(schema): the port value greater than 65535 should not be allowed (#11043)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new c0e3d9150 fix(schema): the port value greater than 65535 should not be
allowed (#11043)
c0e3d9150 is described below
commit c0e3d9150f06c3140a52d145782085d26bc1ea67
Author: 徐瑞东
AuthorDate: Thu Mar 21 19:15:07 2024 +0800
fix(schema): the port value greater than 65535 should not be allowed
(#11043)
---
apisix/schema_def.lua | 4 ++
apisix/upstream.lua | 12 ++
t/node/invalid-port.t | 105 ++
3 files changed, 121 insertions(+)
diff --git a/apisix/schema_def.lua b/apisix/schema_def.lua
index fa6852a94..f32074448 100644
--- a/apisix/schema_def.lua
+++ b/apisix/schema_def.lua
@@ -309,6 +309,7 @@ local nodes_schema = {
description = "port of node",
type = "integer",
minimum = 1,
+maximum = 65535
},
weight = {
description = "weight of node",
@@ -342,6 +343,7 @@ _M.discovery_nodes = {
description = "port of node",
type = "integer",
minimum = 1,
+maximum = 65535
},
weight = {
description = "weight of node",
@@ -901,6 +903,8 @@ _M.stream_route = {
server_port = {
description = "server port",
type = "integer",
+minimum = 1,
+maximum = 65535
},
sni = {
description = "server name indication",
diff --git a/apisix/upstream.lua b/apisix/upstream.lua
index 603c66589..eb5e467da 100644
--- a/apisix/upstream.lua
+++ b/apisix/upstream.lua
@@ -451,6 +451,18 @@ local function check_upstream_conf(in_dp, conf)
return false, "invalid configuration: " .. err
end
+if conf.nodes and not core.table.isarray(conf.nodes) then
+local port
+for addr,_ in pairs(conf.nodes) do
+_, port = core.utils.parse_addr(addr)
+if port then
+if port < 1 or port > 65535 then
+return false, "invalid port " .. tostring(port)
+end
+end
+end
+end
+
local ssl_id = conf.tls and conf.tls.client_cert_id
if ssl_id then
local key = "/ssls/" .. ssl_id
diff --git a/t/node/invalid-port.t b/t/node/invalid-port.t
new file mode 100755
index 0..a058769e9
--- /dev/null
+++ b/t/node/invalid-port.t
@@ -0,0 +1,105 @@
+#
+# Licensed to the Apache Software Foundation (ASF) under one or more
+# contributor license agreements. See the NOTICE file distributed with
+# this work for additional information regarding copyright ownership.
+# The ASF licenses this file to You under the Apache License, Version 2.0
+# (the "License"); you may not use this file except in compliance with
+# the License. You may obtain a copy of the License at
+#
+# http://www.apache.org/licenses/LICENSE-2.0
+#
+# Unless required by applicable law or agreed to in writing, software
+# distributed under the License is distributed on an "AS IS" BASIS,
+# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+# See the License for the specific language governing permissions and
+# limitations under the License.
+#
+use t::APISIX 'no_plan';
+
+no_root_location();
+
+run_tests();
+
+__DATA__
+
+=== TEST 1: set upstream with a invalid node port
+--- config
+location /t {
+content_by_lua_block {
+local t = require("lib.test_admin").test
+local code, body = t('/apisix/admin/upstreams/1',
+ ngx.HTTP_PUT,
+ [[{
+ "nodes": [{
+"port": 65536,
+"host": "127.0.0.1",
+"weight": 1
+}],
+"type": "roundrobin"
+}]]
+)
+
+ngx.status = code
+
+ngx.say(body)
+}
+}
+--- request
+GET /t
+--- error_code: 400
+--- response_body_like
+{"error_msg":"invalid configuration: property \\\"nodes\\\" validation failed:
object matches none of the required"}
+
+
+
+=== TEST 2: set upstream with a node port greater than 65535
+--- config
+location /t {
+content_by_lua_block {
+local t = require("lib.test_admin").test
+local code, body
(apisix) branch release/3.9.0 created (now 9bcabaf12)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/3.9.0 in repository https://gitbox.apache.org/repos/asf/apisix.git at 9bcabaf12 feat: release 3.9.0 (#11061) No new revisions were added by this update.
(apisix) branch master updated: feat: release 3.9.0 (#11061)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new 9bcabaf12 feat: release 3.9.0 (#11061) 9bcabaf12 is described below commit 9bcabaf12769bb3ce4fcfa73e51bafb9d40c3bd9 Author: Abhishek Choudhary AuthorDate: Wed Mar 20 11:49:06 2024 +0545 feat: release 3.9.0 (#11061) --- .asf.yaml | 4 CHANGELOG.md | 48 --- apisix/core/version.lua | 2 +- docs/en/latest/building-apisix.md | 2 +- docs/en/latest/config.json| 2 +- docs/zh/latest/building-apisix.md | 2 +- docs/zh/latest/config.json| 2 +- 7 files changed, 54 insertions(+), 8 deletions(-) diff --git a/.asf.yaml b/.asf.yaml index d5fbaa2ab..2fbe3776c 100644 --- a/.asf.yaml +++ b/.asf.yaml @@ -53,6 +53,10 @@ github: dismiss_stale_reviews: true require_code_owner_reviews: true required_approving_review_count: 2 + release/3.9: +required_pull_request_reviews: + require_code_owner_reviews: true + required_approving_review_count: 2 release/3.8: required_pull_request_reviews: require_code_owner_reviews: true diff --git a/CHANGELOG.md b/CHANGELOG.md index eb4d92194..62e13fb88 100644 --- a/CHANGELOG.md +++ b/CHANGELOG.md @@ -23,6 +23,7 @@ title: Changelog ## Table of Contents +- [3.9.0](#390) - [3.8.0](#380) - [3.7.0](#370) - [3.6.0](#360) @@ -75,11 +76,52 @@ title: Changelog - [0.7.0](#070) - [0.6.0](#060) -## Next Release Version +## 3.9.0 -### Breaking Changes +### Change + +- change: use apisix.enable_http2 to enable HTTP/2 in APISIX (#11032) +- change: unify the keyring and key_encrypt_salt fields (#10771) + +### Core + +- :sunrise: Support HTTP3/QUIC + - [#10989](https://github.com/apache/apisix/pull/10989) + - [#11010](https://github.com/apache/apisix/pull/11010) + - [#11027](https://github.com/apache/apisix/pull/11027) +- :sunrise: add plugins/reload to control api [#10905](https://github.com/apache/apisix/pull/10905) + +### Plugins -- Change the configuration of HTTP/2. The original way is no longer supported: [#11032](https://github.com/apache/apisix/pull/11032) +- :sunrise: add session.cookie configuration [#10919](https://github.com/apache/apisix/pull/10919) +- :sunrise: support endpointslices in kubernetes discovery [#10916](https://github.com/apache/apisix/pull/10916) +- :sunrise: add redis and redis-cluster in limit-req [#10874](https://github.com/apache/apisix/pull/10874) +- :sunrise: support expire prometheus metrics [#10869](https://github.com/apache/apisix/pull/10869) +- :sunrise: add redis and redis-cluster in limit-conn [#10866](https://github.com/apache/apisix/pull/10866) +- :sunrise: allow configuring allow-headers in grpc-web plugin [#10904](https://github.com/apache/apisix/pull/10904) +- :sunrise: Add forward-auth plugin exception configuration status_on_error [#10898](https://github.com/apache/apisix/pull/10898) +- :sunrise: add option to include request body and response body in log util [#10888](https://github.com/apache/apisix/pull/10888) +- :sunrise: support compressed responses in loggers [#10884](https://github.com/apache/apisix/pull/10884) +- :sunrise: add http-dubbo plugin [#10703](https://github.com/apache/apisix/pull/10703) +- :sunrise: support built-in variables in response_headers in mocking plugin [#10872](https://github.com/apache/apisix/pull/10872) +- :sunrise: support other data formats without warnings [#10862](https://github.com/apache/apisix/pull/10862) +- :sunrise: add ocsp-stapling plugin [#10817](https://github.com/apache/apisix/pull/10817) + +### Bug Fixes + +- Fix: wrong namespace related endpoint in k8s [#10917](https://github.com/apache/apisix/pull/10917) +- Fix: when delete the secret cause 500 error [#10902](https://github.com/apache/apisix/pull/10902) +- Fix: jwe-decrypt secret length restriction [#10928](https://github.com/apache/apisix/pull/10928) +- Fix: unnecessary YAML Config reloads [#9065](https://github.com/apache/apisix/pull/9065) +- Fix: real_payload was overridden by malicious payload [#10982](https://github.com/apache/apisix/pull/10982) +- Fix: all origins could pass when allow_origins_by_metadata is set [#10948](https://github.com/apache/apisix/pull/10948) +- Fix: add compatibility headers [#10828](https://github.com/apache/apisix/pull/10828) +- Fix: missing trailers issue [#10851](https://github.com/apache/apisix/pull/10851) +- Fix: decryption failure [#10843](https://github.com/apache/apisix/pull/10843) +- Fix: server-side sessions locked by not calling explicit session:close() [#10788](https://github.com/apache/apisix/pull/10788) +- Fix: skip brotli compression for upstream compressed response [#10740](https://github.com/apache/apisix
(apisix) branch release/3.9 created (now 231412d05)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch release/3.9 in repository https://gitbox.apache.org/repos/asf/apisix.git at 231412d05 perf(ssl): reuse array length variable (#11053) No new revisions were added by this update.
(apisix) branch master updated: chore(deps): bump google.golang.org/protobuf (#11034)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new bd091d030 chore(deps): bump google.golang.org/protobuf (#11034) bd091d030 is described below commit bd091d0300ac58daa31df0062662d88017d5f787 Author: dependabot[bot] <49699333+dependabot[bot]@users.noreply.github.com> AuthorDate: Fri Mar 15 13:07:35 2024 +0545 chore(deps): bump google.golang.org/protobuf (#11034) --- ci/pod/openfunction/function-example/test-body/go.mod | 2 +- ci/pod/openfunction/function-example/test-body/go.sum | 3 ++- 2 files changed, 3 insertions(+), 2 deletions(-) diff --git a/ci/pod/openfunction/function-example/test-body/go.mod b/ci/pod/openfunction/function-example/test-body/go.mod index 3e2f61557..bf571e0ba 100644 --- a/ci/pod/openfunction/function-example/test-body/go.mod +++ b/ci/pod/openfunction/function-example/test-body/go.mod @@ -24,7 +24,7 @@ require ( golang.org/x/text v0.3.7 // indirect google.golang.org/genproto v0.0.0-20210831024726-fe130286e0e2 // indirect google.golang.org/grpc v1.40.0 // indirect - google.golang.org/protobuf v1.28.0 // indirect + google.golang.org/protobuf v1.33.0 // indirect gopkg.in/yaml.v3 v3.0.0 // indirect k8s.io/klog/v2 v2.30.0 // indirect skywalking.apache.org/repo/goapi v0.0.0-20220401015832-2c9eee9481eb // indirect diff --git a/ci/pod/openfunction/function-example/test-body/go.sum b/ci/pod/openfunction/function-example/test-body/go.sum index 35f77fd70..f51a5304a 100644 --- a/ci/pod/openfunction/function-example/test-body/go.sum +++ b/ci/pod/openfunction/function-example/test-body/go.sum @@ -1642,8 +1642,9 @@ google.golang.org/protobuf v1.25.0/go.mod h1:9JNX74DMeImyA3h4bdi1ymwjUzf21/xIlba google.golang.org/protobuf v1.26.0-rc.1/go.mod h1:jlhhOSvTdKEhbULTjvd4ARK9grFBp09yW+WbY/TyQbw= google.golang.org/protobuf v1.26.0/go.mod h1:9q0QmTI4eRPtz6boOQmLYwt+qCgq0jsYwAQnmE0givc= google.golang.org/protobuf v1.27.1/go.mod h1:9q0QmTI4eRPtz6boOQmLYwt+qCgq0jsYwAQnmE0givc= -google.golang.org/protobuf v1.28.0 h1:w43yiav+6bVFTBQFZX0r7ipe9JQ1QsbMgHwbBziscLw= google.golang.org/protobuf v1.28.0/go.mod h1:HV8QOd/L58Z+nl8r43ehVNZIU/HEI6OcFqwMG9pJV4I= +google.golang.org/protobuf v1.33.0 h1:uNO2rsAINq/JlFpSdYEKIZ0uKD/R9cpdv0T+yoGwGmI= +google.golang.org/protobuf v1.33.0/go.mod h1:c6P6GXX6sHbq/GpV6MGZEdwhWPcYBgnhAHhKbcUYpos= gopkg.in/alecthomas/kingpin.v2 v2.2.6/go.mod h1:FMv+mEhP44yOT+4EoQTLFTRgOQ1FBLkstjWtayDeSgw= gopkg.in/alexcesaro/quotedprintable.v3 v3.0.0-20150716171945-2caba252f4dc/go.mod h1:m7x9LTH6d71AHyAX77c9yqWCCa3UKHcVEj9y7hAtKDk= gopkg.in/check.v1 v0.0.0-20161208181325-20d25e280405/go.mod h1:Co6ibVJAznAaIkqp8huTwlJQCZ016jof/cbN4VW5Yz0=
(apisix) branch revert-10655-guohao/fix-health-target-leak deleted (was edf57a719)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch revert-10655-guohao/fix-health-target-leak in repository https://gitbox.apache.org/repos/asf/apisix.git was edf57a719 Revert "fix: the leak of prometheus metrics (#10655)" The revisions that were on this branch are still contained in other references; therefore, this change does not discard any commits from the repository.
(apisix) branch master updated: Revert "fix: the leak of prometheus metrics (#10655)" (#11025)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 963207faf Revert "fix: the leak of prometheus metrics (#10655)"
(#11025)
963207faf is described below
commit 963207faf8ec2ab0e240c09d398da4d634a63376
Author: Abhishek Choudhary
AuthorDate: Wed Mar 13 09:49:13 2024 +0545
Revert "fix: the leak of prometheus metrics (#10655)" (#11025)
---
apisix/plugins/prometheus/exporter.lua | 1 -
t/node/healthcheck-metric.t| 508 -
2 files changed, 509 deletions(-)
diff --git a/apisix/plugins/prometheus/exporter.lua
b/apisix/plugins/prometheus/exporter.lua
index d04d9bb79..59da6c670 100644
--- a/apisix/plugins/prometheus/exporter.lua
+++ b/apisix/plugins/prometheus/exporter.lua
@@ -480,7 +480,6 @@ local function collect(ctx, stream_only)
-- update upstream_status metrics
local stats = control.get_health_checkers()
-metrics.upstream_status:reset()
for _, stat in ipairs(stats) do
for _, node in ipairs(stat.nodes) do
metrics.upstream_status:set(
diff --git a/t/node/healthcheck-metric.t b/t/node/healthcheck-metric.t
deleted file mode 100644
index 7a7d2f993..0
--- a/t/node/healthcheck-metric.t
+++ /dev/null
@@ -1,508 +0,0 @@
-#
-# Licensed to the Apache Software Foundation (ASF) under one or more
-# contributor license agreements. See the NOTICE file distributed with
-# this work for additional information regarding copyright ownership.
-# The ASF licenses this file to You under the Apache License, Version 2.0
-# (the "License"); you may not use this file except in compliance with
-# the License. You may obtain a copy of the License at
-#
-# http://www.apache.org/licenses/LICENSE-2.0
-#
-# Unless required by applicable law or agreed to in writing, software
-# distributed under the License is distributed on an "AS IS" BASIS,
-# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
-# See the License for the specific language governing permissions and
-# limitations under the License.
-#
-use t::APISIX 'no_plan';
-
-no_root_location();
-repeat_each(1);
-log_level('debug');
-no_root_location();
-no_shuffle();
-
-add_block_preprocessor(sub {
-my ($block) = @_;
-
-if (!$block->http_config) {
-my $http_config = <<'_EOC_';
-server {
-listen 8765;
-
-location /ping {
-return 200 '8765';
-}
-
-location /healthz {
-return 200 'ok';
-}
-}
-
-server {
-listen 8766;
-
-location /ping {
-return 200 '8766';
-}
-
-location /healthz {
-return 200 'ok';
-}
-}
-
-
-server {
-listen 8767;
-location /ping {
-return 200 '8767';
-}
-
-location /healthz {
-return 200 'ok';
-}
-}
-
-_EOC_
-$block->set_value("http_config", $http_config);
-}
-
-if (!$block->request) {
-$block->set_value("request", "GET /t");
-}
-
-});
-
-run_tests;
-
-__DATA__
-
-=== TEST 1: enable metrics uri
config
-location /t {
-content_by_lua_block {
-local t = require("lib.test_admin")
-local core = require("apisix.core")
-
--- enable prometheus
-local metric_data = {
-uri = "/apisix/prometheus/metrics",
-plugins = {
-["public-api"] = {}
-}
-}
-
-local code, body = t.test('/apisix/admin/routes/metrics',
-ngx.HTTP_PUT, core.json.encode(metric_data))
-ngx.say(body)
-}
-}
request
-GET /t
response_body
-passed
-
-
-
-=== TEST 2: to reduce one upstream node, the metric should also be reduced by
one.
extra_init_worker_by_lua
-local healthcheck = require("resty.healthcheck")
-local new = healthcheck.new
-healthcheck.new = function(...)
-local obj = new(...)
-local clear = obj.delayed_clear
-obj.delayed_clear = obj.clear
-return obj
-end
config
-location /t {
-content_by_lua_block {
-local core = require("apisix.core")
-local t = require("lib.test_admin")
-local http = require("resty.http")
-
-local function find_apisix_upstream_status(multiLineStr)
-local pattern = "(apisix_upstream_status{.-)$"
-local result = {}
-for line in multiLineStr:gmatch("[^\r\n]+") do
-local match = line:match(pattern)
-if match then
(apisix) branch master updated: refactor(http3): use http3 instead of quic (#11010)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 8c4eff25c refactor(http3): use http3 instead of quic (#11010)
8c4eff25c is described below
commit 8c4eff25c61eced64f5486d3e9fbeb2c659e8732
Author: Leigang Zhang <71714656+zll...@users.noreply.github.com>
AuthorDate: Wed Mar 13 12:03:44 2024 +0800
refactor(http3): use http3 instead of quic (#11010)
---
.github/workflows/{quic.yml => http3.yml} | 10 +-
apisix/cli/ngx_tpl.lua| 5 -
apisix/cli/ops.lua| 20 +---
apisix/cli/schema.lua | 2 +-
conf/config-default.yaml | 4 ++--
t/APISIX.pm | 2 +-
t/cli/test_main.sh| 8 +++-
t/{quic => http3}/admin/basic.t | 0
8 files changed, 33 insertions(+), 18 deletions(-)
diff --git a/.github/workflows/quic.yml b/.github/workflows/http3.yml
similarity index 97%
rename from .github/workflows/quic.yml
rename to .github/workflows/http3.yml
index abaf39988..84b450b82 100644
--- a/.github/workflows/quic.yml
+++ b/.github/workflows/http3.yml
@@ -1,4 +1,4 @@
-name: QUIC
+name: HTTP/3
on:
push:
@@ -32,7 +32,7 @@ jobs:
- lua-resty-worker-events
- lua-resty-events
test_dir:
- - t/quic/admin
+ - t/http3/admin
runs-on: ${{ matrix.platform }}
timeout-minutes: 90
@@ -72,13 +72,13 @@ jobs:
id: test_env
run: |
test_dir="${{ matrix.test_dir }}"
- if [[ $test_dir =~ 't/quic/plugin' ]]; then
+ if [[ $test_dir =~ 't/http3/plugin' ]]; then
echo "type=plugin" >>$GITHUB_OUTPUT
fi
- if [[ $test_dir =~ 't/quic/admin' ]]; then
+ if [[ $test_dir =~ 't/http3/admin' ]]; then
echo "type=first" >>$GITHUB_OUTPUT
fi
- if [[ $test_dir =~ ' t/quic/xrpc' ]]; then
+ if [[ $test_dir =~ ' t/http3/xrpc' ]]; then
echo "type=last" >>$GITHUB_OUTPUT
fi
diff --git a/apisix/cli/ngx_tpl.lua b/apisix/cli/ngx_tpl.lua
index 9642a3605..4b7ff4102 100644
--- a/apisix/cli/ngx_tpl.lua
+++ b/apisix/cli/ngx_tpl.lua
@@ -631,12 +631,15 @@ http {
{% if enable_http2 then %}
http2 on;
{% end %}
+{% if enable_http3_in_server_context then %}
+http3 on;
+{% end %}
{% for _, item in ipairs(node_listen) do %}
listen {* item.ip *}:{* item.port *} default_server {% if
enable_reuseport then %} reuseport {% end %};
{% end %}
{% if ssl.enable then %}
{% for _, item in ipairs(ssl.listen) do %}
-{% if item.enable_quic then %}
+{% if item.enable_http3 then %}
listen {* item.ip *}:{* item.port *} quic default_server {% if
enable_reuseport then %} reuseport {% end %};
listen {* item.ip *}:{* item.port *} ssl default_server;
{% else %}
diff --git a/apisix/cli/ops.lua b/apisix/cli/ops.lua
index 73b9c1d13..37c427458 100644
--- a/apisix/cli/ops.lua
+++ b/apisix/cli/ops.lua
@@ -380,7 +380,7 @@ Please modify "admin_key" in conf/config.yaml .
local ip_port_to_check = {}
local function listen_table_insert(listen_table, scheme, ip, port,
-enable_http2, enable_quic, enable_ipv6)
+enable_http2, enable_http3, enable_ipv6)
if type(ip) ~= "string" then
util.die(scheme, " listen ip format error, must be string", "\n")
end
@@ -402,7 +402,7 @@ Please modify "admin_key" in conf/config.yaml .
ip = ip,
port = port,
enable_http2 = enable_http2,
-enable_quic = enable_quic
+enable_http3 = enable_http3
})
ip_port_to_check[addr] = scheme
end
@@ -417,7 +417,7 @@ Please modify "admin_key" in conf/config.yaml .
ip = ip,
port = port,
enable_http2 = enable_http2,
-enable_quic = enable_quic
+enable_http3 = enable_http3
})
ip_port_to_check[addr] = scheme
end
@@ -466,6 +466,7 @@ Please modify "admin_key" in conf/config.yaml .
end
yaml_conf.apisix.node_listen = node_listen
+local enable_http3_in_server_context = false
local ssl_listen = {}
-- listen in https, support multiple ports, support
(apisix) 01/01: Revert "fix: the leak of prometheus metrics (#10655)"
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch
revert-10655-guohao/fix-health-target-leak
in repository https://gitbox.apache.org/repos/asf/apisix.git
commit edf57a719a2a11b734d8754dff1789a61345a105
Author: Abhishek Choudhary
AuthorDate: Mon Mar 11 22:20:06 2024 +0545
Revert "fix: the leak of prometheus metrics (#10655)"
This reverts commit 59a6be41891bcb74acfd41d120ee9a924e2d6e8b.
---
apisix/plugins/prometheus/exporter.lua | 1 -
t/node/healthcheck-metric.t| 508 -
2 files changed, 509 deletions(-)
diff --git a/apisix/plugins/prometheus/exporter.lua
b/apisix/plugins/prometheus/exporter.lua
index d04d9bb79..59da6c670 100644
--- a/apisix/plugins/prometheus/exporter.lua
+++ b/apisix/plugins/prometheus/exporter.lua
@@ -480,7 +480,6 @@ local function collect(ctx, stream_only)
-- update upstream_status metrics
local stats = control.get_health_checkers()
-metrics.upstream_status:reset()
for _, stat in ipairs(stats) do
for _, node in ipairs(stat.nodes) do
metrics.upstream_status:set(
diff --git a/t/node/healthcheck-metric.t b/t/node/healthcheck-metric.t
deleted file mode 100644
index 7a7d2f993..0
--- a/t/node/healthcheck-metric.t
+++ /dev/null
@@ -1,508 +0,0 @@
-#
-# Licensed to the Apache Software Foundation (ASF) under one or more
-# contributor license agreements. See the NOTICE file distributed with
-# this work for additional information regarding copyright ownership.
-# The ASF licenses this file to You under the Apache License, Version 2.0
-# (the "License"); you may not use this file except in compliance with
-# the License. You may obtain a copy of the License at
-#
-# http://www.apache.org/licenses/LICENSE-2.0
-#
-# Unless required by applicable law or agreed to in writing, software
-# distributed under the License is distributed on an "AS IS" BASIS,
-# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
-# See the License for the specific language governing permissions and
-# limitations under the License.
-#
-use t::APISIX 'no_plan';
-
-no_root_location();
-repeat_each(1);
-log_level('debug');
-no_root_location();
-no_shuffle();
-
-add_block_preprocessor(sub {
-my ($block) = @_;
-
-if (!$block->http_config) {
-my $http_config = <<'_EOC_';
-server {
-listen 8765;
-
-location /ping {
-return 200 '8765';
-}
-
-location /healthz {
-return 200 'ok';
-}
-}
-
-server {
-listen 8766;
-
-location /ping {
-return 200 '8766';
-}
-
-location /healthz {
-return 200 'ok';
-}
-}
-
-
-server {
-listen 8767;
-location /ping {
-return 200 '8767';
-}
-
-location /healthz {
-return 200 'ok';
-}
-}
-
-_EOC_
-$block->set_value("http_config", $http_config);
-}
-
-if (!$block->request) {
-$block->set_value("request", "GET /t");
-}
-
-});
-
-run_tests;
-
-__DATA__
-
-=== TEST 1: enable metrics uri
config
-location /t {
-content_by_lua_block {
-local t = require("lib.test_admin")
-local core = require("apisix.core")
-
--- enable prometheus
-local metric_data = {
-uri = "/apisix/prometheus/metrics",
-plugins = {
-["public-api"] = {}
-}
-}
-
-local code, body = t.test('/apisix/admin/routes/metrics',
-ngx.HTTP_PUT, core.json.encode(metric_data))
-ngx.say(body)
-}
-}
request
-GET /t
response_body
-passed
-
-
-
-=== TEST 2: to reduce one upstream node, the metric should also be reduced by
one.
extra_init_worker_by_lua
-local healthcheck = require("resty.healthcheck")
-local new = healthcheck.new
-healthcheck.new = function(...)
-local obj = new(...)
-local clear = obj.delayed_clear
-obj.delayed_clear = obj.clear
-return obj
-end
config
-location /t {
-content_by_lua_block {
-local core = require("apisix.core")
-local t = require("lib.test_admin")
-local http = require("resty.http")
-
-local function find_apisix_upstream_status(multiLineStr)
-local pattern = "(apisix_upstream_status{.-)$"
-local result = {}
-for line in multiLineStr:gmatch("[^\r\n]+") do
-local match = line:match(pattern)
-if match then
-table.insert(result, match)
-end
-
(apisix) branch revert-10655-guohao/fix-health-target-leak created (now edf57a719)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch revert-10655-guohao/fix-health-target-leak in repository https://gitbox.apache.org/repos/asf/apisix.git at edf57a719 Revert "fix: the leak of prometheus metrics (#10655)" This branch includes the following new commits: new edf57a719 Revert "fix: the leak of prometheus metrics (#10655)" The 1 revisions listed above as "new" are entirely new to this repository and will be described in separate emails. The revisions listed as "add" were already present in the repository and have only been added to this reference.
(apisix) branch master updated: feat(openid-connect): add session.cookie configuration (#10919)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 17ad90d06 feat(openid-connect): add session.cookie configuration
(#10919)
17ad90d06 is described below
commit 17ad90d06a63d6620262d096a554be55cecae047
Author: illidan
AuthorDate: Mon Mar 4 23:24:11 2024 +0800
feat(openid-connect): add session.cookie configuration (#10919)
---
apisix/plugins/openid-connect.lua| 9 ++
docs/en/latest/plugins/openid-connect.md | 2 +
docs/zh/latest/plugins/openid-connect.md | 2 +
t/plugin/openid-connect6.t | 157 +++
4 files changed, 170 insertions(+)
diff --git a/apisix/plugins/openid-connect.lua
b/apisix/plugins/openid-connect.lua
index 28af0e933..435cf6363 100644
--- a/apisix/plugins/openid-connect.lua
+++ b/apisix/plugins/openid-connect.lua
@@ -72,6 +72,15 @@ local schema = {
description = "the key used for the encrypt and HMAC
calculation",
minLength = 16,
},
+cookie = {
+type = "object",
+properties = {
+lifetime = {
+type = "integer",
+description = "it holds the cookie lifetime in
seconds in the future",
+}
+}
+}
},
required = {"secret"},
additionalProperties = false,
diff --git a/docs/en/latest/plugins/openid-connect.md
b/docs/en/latest/plugins/openid-connect.md
index 1fcba8811..103c7c026 100644
--- a/docs/en/latest/plugins/openid-connect.md
+++ b/docs/en/latest/plugins/openid-connect.md
@@ -61,6 +61,8 @@ description: OpenID Connect allows the client to obtain user
information from th
| set_refresh_token_header | boolean | False| false
| | When set to true and a refresh token object is
available, sets it in the `X-Refresh-Token` request header.
|
| session | object | False|
| | When bearer_only is set to false, openid-connect will
use Authorization Code flow to authenticate on the IDP, so you need to set the
session-related configuration.
|
| session.secret | string | True | Automatic
generation | 16 or more characters | The key used for session encrypt and HMAC
operation.
|
+| session.cookie | object | False|
| |
|
+| session.cookie.lifetime | integer | False| 3600
| | it holds the cookie lifetime in seconds in the future.
By default this is set to 3,600 seconds. This can be configured with Nginx set
$session_cookie_lifetime 3600;. This does not set cookie's expiration time on
session only (by default) cookies, but it is used if the cookies are configured
persistent with session.cookie.persistent == true. |
| unauth_action| string | False| "auth"
| ["auth","deny","pass"]| Specify the response type on
unauthenticated requests. "auth" redirects to identity provider, "deny" results
in a 401 response, "pass" will allow the request without authentication.
|
| proxy_opts | object | False|
| | HTTP proxy that the OpenID provider
is behind.
|
| proxy_opts.http_proxy | string | False| |
http://proxy-server:port | HTTP proxy server address.
|
diff --git a/docs/zh/latest/plugins/openid-connect.md
b/docs/zh/latest/pl
(apisix) branch master updated (2caa9d88a -> 2e7c13ceb)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git from 2caa9d88a docs: remove misleading information (#10973) add 2e7c13ceb update examples and valid value of message attribute (#10984) No new revisions were added by this update. Summary of changes: docs/en/latest/plugins/ua-restriction.md | 40 docs/zh/latest/plugins/ua-restriction.md | 38 ++ 2 files changed, 17 insertions(+), 61 deletions(-)
(apisix) branch master updated: docs: remove misleading information (#10973)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new 2caa9d88a docs: remove misleading information (#10973) 2caa9d88a is described below commit 2caa9d88abec2e482c6e7f4da4845bbe7f4278ef Author: Abhishek Choudhary AuthorDate: Fri Mar 1 08:29:08 2024 +0545 docs: remove misleading information (#10973) --- docs/en/latest/plugin-develop.md | 2 +- 1 file changed, 1 insertion(+), 1 deletion(-) diff --git a/docs/en/latest/plugin-develop.md b/docs/en/latest/plugin-develop.md index 1b674303e..014939a51 100644 --- a/docs/en/latest/plugin-develop.md +++ b/docs/en/latest/plugin-develop.md @@ -341,7 +341,7 @@ If none of the keys in `keyring` can decrypt the data, the original data is used Determine which phase to run, generally access or rewrite. If you don't know the [OpenResty lifecycle](https://github.com/openresty/lua-nginx-module/blob/master/README.markdown#directives), it's recommended to know it in advance. For example key-auth is an authentication plugin, thus the authentication should be completed before forwarding the request to any upstream service. Therefore, the plugin must be executed in the rewrite phases. -In APISIX, only the authentication logic can be run in the rewrite phase. Other logic needs to run before proxy should be in access phase. +Similarly, if you want to modify or process the response body or headers you can do that in the `body_filter` or in the `header_filter` phases respectively. The following code snippet shows how to implement any logic relevant to the plugin in the OpenResty log phase.
(apisix) branch master updated: feat(plugin): update lua-resty-t1k to 1.1.1 (#10976)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 1c6f7134e feat(plugin): update lua-resty-t1k to 1.1.1 (#10976)
1c6f7134e is described below
commit 1c6f7134e82a000b3ae99fa10971de63eca5fc0f
Author: Blaise Wang
AuthorDate: Thu Feb 29 11:43:28 2024 +0800
feat(plugin): update lua-resty-t1k to 1.1.1 (#10976)
---
apisix-master-0.rockspec | 2 +-
1 file changed, 1 insertion(+), 1 deletion(-)
diff --git a/apisix-master-0.rockspec b/apisix-master-0.rockspec
index 90327d61b..91e6b541c 100644
--- a/apisix-master-0.rockspec
+++ b/apisix-master-0.rockspec
@@ -79,7 +79,7 @@ dependencies = {
"nanoid = 0.1-1",
"lua-resty-mediador = 0.1.2-1",
"lua-resty-ldap = 0.1.0-0",
-"lua-resty-t1k = 1.1.0",
+"lua-resty-t1k = 1.1.1",
"brotli-ffi = 0.3-1",
"lua-ffi-zlib = 0.6-0"
}
(apisix) branch master updated: chore: the error_log level should be when etcd compacts (#10968)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 35020e1cf chore: the error_log level should be when etcd compacts
(#10968)
35020e1cf is described below
commit 35020e1cf5a4c0a7abcf73b70cb0260c9f2656bb
Author: Liu Wei
AuthorDate: Thu Feb 29 11:42:28 2024 +0800
chore: the error_log level should be when etcd compacts (#10968)
---
apisix/core/config_etcd.lua | 4 ++--
1 file changed, 2 insertions(+), 2 deletions(-)
diff --git a/apisix/core/config_etcd.lua b/apisix/core/config_etcd.lua
index eebf74eee..c1ea323db 100644
--- a/apisix/core/config_etcd.lua
+++ b/apisix/core/config_etcd.lua
@@ -227,7 +227,7 @@ local function do_run_watch(premature)
log.warn("watch canceled by etcd, res: ", inspect(res))
if res.result.compact_revision then
watch_ctx.rev = tonumber(res.result.compact_revision)
-log.warn("etcd compacted, compact_revision=", watch_ctx.rev)
+log.error("etcd compacted, compact_revision=", watch_ctx.rev)
produce_res(nil, "compacted")
end
cancel_watch(http_cli)
@@ -629,7 +629,7 @@ local function sync_data(self)
if not dir_res then
if err == "compacted" then
self.need_reload = true
-log.warn("waitdir [", self.key, "] err: ", err,
+log.error("waitdir [", self.key, "] err: ", err,
", will read the configuration again via readdir")
return false
end
(apisix) branch master updated: docs(workflow): fix apisix http port (#10974)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new c9a6139d3 docs(workflow): fix apisix http port (#10974) c9a6139d3 is described below commit c9a6139d323d1ee898dad329832cc5301e86d98e Author: Leigang Zhang <71714656+zll...@users.noreply.github.com> AuthorDate: Wed Feb 28 10:00:58 2024 +0800 docs(workflow): fix apisix http port (#10974) --- docs/en/latest/plugins/workflow.md | 8 docs/zh/latest/plugins/workflow.md | 6 +++--- 2 files changed, 7 insertions(+), 7 deletions(-) diff --git a/docs/en/latest/plugins/workflow.md b/docs/en/latest/plugins/workflow.md index 6448d0224..48fa0963d 100644 --- a/docs/en/latest/plugins/workflow.md +++ b/docs/en/latest/plugins/workflow.md @@ -126,24 +126,24 @@ HTTP/1.1 403 Forbidden **Example 2: if the request uri is `/hello/v2/appid`, the `workflow` plugin would execute the `limit-count` plugin** ```shell -curl http://127.0.0.1:0080/hello/v2/appid -i +curl http://127.0.0.1:9080/hello/v2/appid -i HTTP/1.1 200 OK ``` ```shell -curl http://127.0.0.1:0080/hello/v2/appid -i +curl http://127.0.0.1:9080/hello/v2/appid -i HTTP/1.1 200 OK ``` ```shell -curl http://127.0.0.1:0080/hello/v2/appid -i +curl http://127.0.0.1:9080/hello/v2/appid -i HTTP/1.1 429 Too Many Requests ``` **Example 3: if the request can not match any `case` in the `rules`, the `workflow` plugin would do nothing** ```shell -curl http://127.0.0.1:0080/hello/fake -i +curl http://127.0.0.1:9080/hello/fake -i HTTP/1.1 200 OK ``` diff --git a/docs/zh/latest/plugins/workflow.md b/docs/zh/latest/plugins/workflow.md index 0c7228a9e..51ed1b32a 100644 --- a/docs/zh/latest/plugins/workflow.md +++ b/docs/zh/latest/plugins/workflow.md @@ -126,17 +126,17 @@ HTTP/1.1 403 Forbidden **示例 2: 如果请求的 uri 是 `/hello/v2/appid`,则执行 `limit-count` 插件,限制请求的数量为 2,时间窗口为 60 秒,如果超过限制数量,则返回给客户端状态码 `429`** ```shell -curl http://127.0.0.1:0080/hello/v2/appid -i +curl http://127.0.0.1:9080/hello/v2/appid -i HTTP/1.1 200 OK ``` ```shell -curl http://127.0.0.1:0080/hello/v2/appid -i +curl http://127.0.0.1:9080/hello/v2/appid -i HTTP/1.1 200 OK ``` ```shell -curl http://127.0.0.1:0080/hello/v2/appid -i +curl http://127.0.0.1:9080/hello/v2/appid -i HTTP/1.1 429 Too Many Requests ```
(apisix) branch master updated: fix: add apisix/plugin/limit-req to makefile (#10959)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new 83248215d fix: add apisix/plugin/limit-req to makefile (#10959) 83248215d is described below commit 83248215d877302d231826e00dd93c90b2769682 Author: Leigang Zhang <71714656+zll...@users.noreply.github.com> AuthorDate: Mon Feb 26 15:24:39 2024 +0800 fix: add apisix/plugin/limit-req to makefile (#10959) --- Makefile | 3 +++ 1 file changed, 3 insertions(+) diff --git a/Makefile b/Makefile index 1482198f0..ff50ca881 100644 --- a/Makefile +++ b/Makefile @@ -312,6 +312,9 @@ install: runtime $(ENV_INSTALL) -d $(ENV_INST_LUADIR)/apisix/plugins/limit-conn $(ENV_INSTALL) apisix/plugins/limit-conn/*.lua $(ENV_INST_LUADIR)/apisix/plugins/limit-conn/ + $(ENV_INSTALL) -d $(ENV_INST_LUADIR)/apisix/plugins/limit-req + $(ENV_INSTALL) apisix/plugins/limit-req/*.lua $(ENV_INST_LUADIR)/apisix/plugins/limit-req/ + $(ENV_INSTALL) -d $(ENV_INST_LUADIR)/apisix/plugins/limit-count $(ENV_INSTALL) apisix/plugins/limit-count/*.lua $(ENV_INST_LUADIR)/apisix/plugins/limit-count/
(apisix) branch revert-10874-feat/add_redis_in_limit_req deleted (was 10e32536d)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch revert-10874-feat/add_redis_in_limit_req in repository https://gitbox.apache.org/repos/asf/apisix.git was 10e32536d Revert "feat: add redis and redis-cluster in limit-req (#10874)" This change permanently discards the following revisions: discard 10e32536d Revert "feat: add redis and redis-cluster in limit-req (#10874)"
(apisix) 01/01: Revert "feat: add redis and redis-cluster in limit-req (#10874)"
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch
revert-10874-feat/add_redis_in_limit_req
in repository https://gitbox.apache.org/repos/asf/apisix.git
commit 10e32536d89196be203f5aad5a8665933506ff65
Author: Abhishek Choudhary
AuthorDate: Fri Feb 23 13:54:05 2024 +0545
Revert "feat: add redis and redis-cluster in limit-req (#10874)"
This reverts commit 1439b1325a0409154d1157a23cf390007b9a6023.
---
apisix/cli/ngx_tpl.lua | 1 -
apisix/plugins/limit-req.lua | 61 +-
.../plugins/limit-req/limit-req-redis-cluster.lua | 50 --
apisix/plugins/limit-req/limit-req-redis.lua | 54 --
apisix/plugins/limit-req/util.lua | 78 ---
conf/config-default.yaml | 1 -
docs/en/latest/plugins/limit-req.md| 13 -
docs/zh/latest/plugins/limit-req.md| 13 -
t/APISIX.pm| 1 -
t/plugin/limit-req-redis-cluster.t | 605 ---
t/plugin/limit-req-redis.t | 653 -
11 files changed, 6 insertions(+), 1524 deletions(-)
diff --git a/apisix/cli/ngx_tpl.lua b/apisix/cli/ngx_tpl.lua
index d4d78a219..f1b10499c 100644
--- a/apisix/cli/ngx_tpl.lua
+++ b/apisix/cli/ngx_tpl.lua
@@ -293,7 +293,6 @@ http {
{% end %}
{% if enabled_plugins["limit-req"] then %}
-lua_shared_dict plugin-limit-req-redis-cluster-slot-lock {*
http.lua_shared_dict["plugin-limit-req-redis-cluster-slot-lock"] *};
lua_shared_dict plugin-limit-req {*
http.lua_shared_dict["plugin-limit-req"] *};
{% end %}
diff --git a/apisix/plugins/limit-req.lua b/apisix/plugins/limit-req.lua
index 641eed4bc..536d06176 100644
--- a/apisix/plugins/limit-req.lua
+++ b/apisix/plugins/limit-req.lua
@@ -14,29 +14,16 @@
-- See the License for the specific language governing permissions and
-- limitations under the License.
--
-local limit_req_new = require("resty.limit.req").new
-local core = require("apisix.core")
-local redis_schema = require("apisix.utils.redis-schema")
-local policy_to_additional_properties = redis_schema.schema
-local plugin_name = "limit-req"
+local limit_req_new = require("resty.limit.req").new
+local core = require("apisix.core")
+local plugin_name = "limit-req"
local sleep = core.sleep
-local redis_single_new
-local redis_cluster_new
-do
-local redis_src = "apisix.plugins.limit-req.limit-req-redis"
-redis_single_new = require(redis_src).new
-
-local cluster_src = "apisix.plugins.limit-req.limit-req-redis-cluster"
-redis_cluster_new = require(cluster_src).new
-end
-
local lrucache = core.lrucache.new({
type = "plugin",
})
-
local schema = {
type = "object",
properties = {
@@ -47,11 +34,6 @@ local schema = {
enum = {"var", "var_combination"},
default = "var",
},
-policy = {
-type = "string",
-enum = {"redis", "redis-cluster", "local"},
-default = "local",
-},
rejected_code = {
type = "integer", minimum = 200, maximum = 599, default = 503
},
@@ -63,25 +45,7 @@ local schema = {
},
allow_degradation = {type = "boolean", default = false}
},
-required = {"rate", "burst", "key"},
-["if"] = {
-properties = {
-policy = {
-enum = {"redis"},
-},
-},
-},
-["then"] = policy_to_additional_properties.redis,
-["else"] = {
-["if"] = {
-properties = {
-policy = {
-enum = {"redis-cluster"},
-},
-},
-},
-["then"] = policy_to_additional_properties["redis-cluster"],
-}
+required = {"rate", "burst", "key"}
}
@@ -104,21 +68,8 @@ end
local function create_limit_obj(conf)
-if conf.policy == "local" then
-core.log.info("create new limit-req plugin instance")
-return limit_req_new("plugin-limit-req", conf.rate, conf.burst)
-
-elseif conf.policy == "redis" then
-core.log.info("create new limit-req redis plugin instance")
-return redis_single_new("plugin-limit-req", conf, conf.rate,
conf.burst)
-
-elseif conf.policy == "redis-cluster" then
-core.log.info("create new lim
(apisix) branch revert-10874-feat/add_redis_in_limit_req created (now 10e32536d)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch revert-10874-feat/add_redis_in_limit_req in repository https://gitbox.apache.org/repos/asf/apisix.git at 10e32536d Revert "feat: add redis and redis-cluster in limit-req (#10874)" This branch includes the following new commits: new 10e32536d Revert "feat: add redis and redis-cluster in limit-req (#10874)" The 1 revisions listed above as "new" are entirely new to this repository and will be described in separate emails. The revisions listed as "add" were already present in the repository and have only been added to this reference.
(apisix) branch master updated: feat: add redis and redis-cluster in limit-req (#10874)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 1439b1325 feat: add redis and redis-cluster in limit-req (#10874)
1439b1325 is described below
commit 1439b1325a0409154d1157a23cf390007b9a6023
Author: theweakgod <1031205...@qq.com>
AuthorDate: Thu Feb 22 23:52:20 2024 +0800
feat: add redis and redis-cluster in limit-req (#10874)
---
apisix/cli/ngx_tpl.lua | 1 +
apisix/plugins/limit-req.lua | 61 +-
.../plugins/limit-req/limit-req-redis-cluster.lua | 50 ++
apisix/plugins/limit-req/limit-req-redis.lua | 54 ++
apisix/plugins/limit-req/util.lua | 78 +++
conf/config-default.yaml | 1 +
docs/en/latest/plugins/limit-req.md| 13 +
docs/zh/latest/plugins/limit-req.md| 13 +
t/APISIX.pm| 1 +
t/plugin/limit-req-redis-cluster.t | 605 +++
t/plugin/limit-req-redis.t | 653 +
11 files changed, 1524 insertions(+), 6 deletions(-)
diff --git a/apisix/cli/ngx_tpl.lua b/apisix/cli/ngx_tpl.lua
index f1b10499c..d4d78a219 100644
--- a/apisix/cli/ngx_tpl.lua
+++ b/apisix/cli/ngx_tpl.lua
@@ -293,6 +293,7 @@ http {
{% end %}
{% if enabled_plugins["limit-req"] then %}
+lua_shared_dict plugin-limit-req-redis-cluster-slot-lock {*
http.lua_shared_dict["plugin-limit-req-redis-cluster-slot-lock"] *};
lua_shared_dict plugin-limit-req {*
http.lua_shared_dict["plugin-limit-req"] *};
{% end %}
diff --git a/apisix/plugins/limit-req.lua b/apisix/plugins/limit-req.lua
index 536d06176..641eed4bc 100644
--- a/apisix/plugins/limit-req.lua
+++ b/apisix/plugins/limit-req.lua
@@ -14,16 +14,29 @@
-- See the License for the specific language governing permissions and
-- limitations under the License.
--
-local limit_req_new = require("resty.limit.req").new
-local core = require("apisix.core")
-local plugin_name = "limit-req"
+local limit_req_new = require("resty.limit.req").new
+local core = require("apisix.core")
+local redis_schema = require("apisix.utils.redis-schema")
+local policy_to_additional_properties = redis_schema.schema
+local plugin_name = "limit-req"
local sleep = core.sleep
+local redis_single_new
+local redis_cluster_new
+do
+local redis_src = "apisix.plugins.limit-req.limit-req-redis"
+redis_single_new = require(redis_src).new
+
+local cluster_src = "apisix.plugins.limit-req.limit-req-redis-cluster"
+redis_cluster_new = require(cluster_src).new
+end
+
local lrucache = core.lrucache.new({
type = "plugin",
})
+
local schema = {
type = "object",
properties = {
@@ -34,6 +47,11 @@ local schema = {
enum = {"var", "var_combination"},
default = "var",
},
+policy = {
+type = "string",
+enum = {"redis", "redis-cluster", "local"},
+default = "local",
+},
rejected_code = {
type = "integer", minimum = 200, maximum = 599, default = 503
},
@@ -45,7 +63,25 @@ local schema = {
},
allow_degradation = {type = "boolean", default = false}
},
-required = {"rate", "burst", "key"}
+required = {"rate", "burst", "key"},
+["if"] = {
+properties = {
+policy = {
+enum = {"redis"},
+},
+},
+},
+["then"] = policy_to_additional_properties.redis,
+["else"] = {
+["if"] = {
+properties = {
+policy = {
+enum = {"redis-cluster"},
+},
+},
+},
+["then"] = policy_to_additional_properties["redis-cluster"],
+}
}
@@ -68,8 +104,21 @@ end
local function create_limit_obj(conf)
-core.log.info("create new limit-req plugin instance")
-return limit_req_new("plugin-limit-req", conf.rate, conf.burst)
+if conf.policy == "local" then
+core.log.info("create new limit-req plugin instance")
+return limit_req_new("plugin-limit-req", conf.rate, conf.burst)
+
+elseif conf.policy == "redis" then
+core.log.info("create new limit-req redis plug
(apisix) branch master updated: fix: when delete the secret cause 500 error (#10902)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 1d57986c5 fix: when delete the secret cause 500 error (#10902)
1d57986c5 is described below
commit 1d57986c5f9c76eebd364c7fe2c0f43e749f52f7
Author: cooper.wu
AuthorDate: Wed Feb 21 22:52:50 2024 +0800
fix: when delete the secret cause 500 error (#10902)
---
apisix/secret.lua | 24 +++--
t/secret/secret_lru.t | 98 +++
2 files changed, 111 insertions(+), 11 deletions(-)
diff --git a/apisix/secret.lua b/apisix/secret.lua
index ca9b09190..90a99d321 100644
--- a/apisix/secret.lua
+++ b/apisix/secret.lua
@@ -58,20 +58,22 @@ local function create_secret_kvs(values)
local secret_managers = {}
for _, v in ipairs(values) do
-local path = v.value.id
-local idx = find(path, "/")
-if not idx then
-core.log.error("no secret id")
-return nil
-end
+if v then
+local path = v.value.id
+local idx = find(path, "/")
+if not idx then
+core.log.error("no secret id")
+return nil
+end
-local manager = sub(path, 1, idx - 1)
-local id = sub(path, idx + 1)
+local manager = sub(path, 1, idx - 1)
+local id = sub(path, idx + 1)
-if not secret_managers[manager] then
-secret_managers[manager] = {}
+if not secret_managers[manager] then
+secret_managers[manager] = {}
+end
+secret_managers[manager][id] = v.value
end
-secret_managers[manager][id] = v.value
end
return secret_managers
diff --git a/t/secret/secret_lru.t b/t/secret/secret_lru.t
new file mode 100644
index 0..3ff3386fc
--- /dev/null
+++ b/t/secret/secret_lru.t
@@ -0,0 +1,98 @@
+#
+# Licensed to the Apache Software Foundation (ASF) under one or more
+# contributor license agreements. See the NOTICE file distributed with
+# this work for additional information regarding copyright ownership.
+# The ASF licenses this file to You under the Apache License, Version 2.0
+# (the "License"); you may not use this file except in compliance with
+# the License. You may obtain a copy of the License at
+#
+# http://www.apache.org/licenses/LICENSE-2.0
+#
+# Unless required by applicable law or agreed to in writing, software
+# distributed under the License is distributed on an "AS IS" BASIS,
+# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+# See the License for the specific language governing permissions and
+# limitations under the License.
+#
+use t::APISIX 'no_plan';
+
+repeat_each(1);
+no_long_string();
+no_root_location();
+log_level("info");
+run_tests;
+
+__DATA__
+
+=== TEST 1: add secret && consumer && check
+--- request
+GET /t
+--- config
+location /t {
+content_by_lua_block {
+local t = require("lib.test_admin").test
+-- put secret vault config
+local code, body = t('/apisix/admin/secrets/vault/mysecret',
+ngx.HTTP_PUT,
+[[{
+"uri": "http://127.0.0.1:8200";,
+"prefix": "kv-v1/apisix",
+"token": "root"
+}]]
+)
+if code >= 300 then
+ngx.status = code
+return ngx.say(body)
+end
+
+-- change consumer with secrets ref: vault
+code, body = t('/apisix/admin/consumers',
+ngx.HTTP_PUT,
+[[{
+"username": "jack",
+"plugins": {
+ "key-auth": {
+"key": "$secret://vault/mysecret/jack/auth-key"
+}
+}
+}]]
+)
+if code >= 300 then
+ngx.status = code
+return ngx.say(body)
+end
+
+
+local secret = require("apisix.secret")
+local value =
secret.fetch_by_uri("$secret://vault/mysecret/jack/auth-key")
+
+
+local code, body = t('/apisix/admin/secrets/vault/mysecret',
ngx.HTTP_DELETE)
+if code >= 300 then
+ngx.status = code
+return ngx.say(body)
+end
+
+code, body = t('/apisix/admin/consumers',
+ngx.HTTP_PUT,
+[[{
+
(apisix) branch master updated: fix: jwe-decrypt secret length restriction (#10928)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new ec3809454 fix: jwe-decrypt secret length restriction (#10928)
ec3809454 is described below
commit ec380945496324c00e7caaf77dd6ec220b12f1fc
Author: Vacant
AuthorDate: Mon Feb 12 11:31:17 2024 +0800
fix: jwe-decrypt secret length restriction (#10928)
---
apisix/plugins/jwe-decrypt.lua| 21 -
docs/en/latest/plugins/jwe-decrypt.md | 6 +++
docs/zh/latest/plugins/jwe-decrypt.md | 6 +++
t/plugin/jwe-decrypt.t| 88 +--
4 files changed, 95 insertions(+), 26 deletions(-)
diff --git a/apisix/plugins/jwe-decrypt.lua b/apisix/plugins/jwe-decrypt.lua
index f163f4034..0e4447e02 100644
--- a/apisix/plugins/jwe-decrypt.lua
+++ b/apisix/plugins/jwe-decrypt.lua
@@ -47,7 +47,7 @@ local consumer_schema = {
type = "object",
properties = {
key = { type = "string" },
-secret = { type = "string", minLength = 32 },
+secret = { type = "string" },
is_base64_encoded = { type = "boolean" },
},
required = { "key", "secret" },
@@ -66,7 +66,24 @@ local _M = {
function _M.check_schema(conf, schema_type)
if schema_type == core.schema.TYPE_CONSUMER then
-return core.schema.check(consumer_schema, conf)
+local ok, err = core.schema.check(consumer_schema, conf)
+if not ok then
+return false, err
+end
+
+-- restrict the length of secret, we use A256GCM for encryption,
+-- so the length should be 32 chars only
+if conf.is_base64_encoded then
+if #base64.decode_base64url(conf.secret) ~= 32 then
+ return false, "the secret length after base64 decode should
be 32 chars"
+end
+else
+if #conf.secret ~= 32 then
+return false, "the secret length should be 32 chars"
+end
+end
+
+return true
end
return core.schema.check(schema, conf)
end
diff --git a/docs/en/latest/plugins/jwe-decrypt.md
b/docs/en/latest/plugins/jwe-decrypt.md
index 9969094af..6da75d2bb 100644
--- a/docs/en/latest/plugins/jwe-decrypt.md
+++ b/docs/en/latest/plugins/jwe-decrypt.md
@@ -44,6 +44,12 @@ For Consumer:
| secret| string | True
| | | The decryption key. Must be 32
characters. The key could be saved in a secret manager using the
[Secret](../terminology/secret.md) resource. |
| is_base64_encoded | boolean | False
| false | | Set to true if the secret is
base64 encoded.
|
+:::note
+
+After enabling `is_base64_encoded`, your `secret` length may exceed 32 chars.
You only need to make sure that the length after decoding is still 32 chars.
+
+:::
+
For Route:
| Name | Type | Required | Default | Description
|
diff --git a/docs/zh/latest/plugins/jwe-decrypt.md
b/docs/zh/latest/plugins/jwe-decrypt.md
index ce5c98fd6..cf7363e27 100644
--- a/docs/zh/latest/plugins/jwe-decrypt.md
+++ b/docs/zh/latest/plugins/jwe-decrypt.md
@@ -44,6 +44,12 @@ Consumer 配置:
| secret| string | True | | | 解密密钥,必须为 32 位。秘钥可以使用
[Secret](../terminology/secret.md) 资源保存在密钥管理服务中 |
| is_base64_encoded | boolean | False | false | | 如果密钥是 Base64 编码,则需要配置为
`true` |
+:::note
+
+注意,在启用 `is_base64_encoded` 后,你的 `secret` 长度可能会超过 32 位,你只需要保证在 Decode 后的长度仍然是
32 位即可。
+
+:::
+
Route 配置:
| 名称 | 类型 | 必选项 | 默认值 | 描述
|
diff --git a/t/plugin/jwe-decrypt.t b/t/plugin/jwe-decrypt.t
index 599fed296..e7fcf7756 100644
--- a/t/plugin/jwe-decrypt.t
+++ b/t/plugin/jwe-decrypt.t
@@ -54,7 +54,7 @@ qr/{"key":"123","secret":"[a-zA-Z0-9+\\\/]+={0,2}"}/
-=== TEST 2: wrong type of string
+=== TEST 2: wrong type of key
--- config
location /t {
content_by_lua_block {
@@ -74,13 +74,13 @@ done
-=== TEST 3: wrong type of string
+=== TEST 3: wrong type of secret
--- config
location /t {
content_by_lua_block {
local core = require("apisix.core")
local plugin = require("apisix.plugins.jwe-decrypt")
-local ok, err = plugin.check_schema({key = "123", secret =
"123456"}, core.schema.TYPE_CONSUMER)
+local ok
(apisix) branch master updated: chore(deps): bump actions/setup-node from 4.0.1 to 4.0.2 (#10923)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git The following commit(s) were added to refs/heads/master by this push: new 212a44e26 chore(deps): bump actions/setup-node from 4.0.1 to 4.0.2 (#10923) 212a44e26 is described below commit 212a44e26d6f78c08cbcd43db68d706854ead459 Author: dependabot[bot] <49699333+dependabot[bot]@users.noreply.github.com> AuthorDate: Fri Feb 9 09:34:21 2024 +0545 chore(deps): bump actions/setup-node from 4.0.1 to 4.0.2 (#10923) --- .github/workflows/doc-lint.yml | 2 +- .github/workflows/lint.yml | 2 +- 2 files changed, 2 insertions(+), 2 deletions(-) diff --git a/.github/workflows/doc-lint.yml b/.github/workflows/doc-lint.yml index a61040eb3..d88474141 100644 --- a/.github/workflows/doc-lint.yml +++ b/.github/workflows/doc-lint.yml @@ -24,7 +24,7 @@ jobs: steps: - uses: actions/checkout@v4 - name: 🚀 Use Node.js -uses: actions/setup-node@v4.0.1 +uses: actions/setup-node@v4.0.2 with: node-version: "12.x" - run: npm install -g markdownlint-cli@0.25.0 diff --git a/.github/workflows/lint.yml b/.github/workflows/lint.yml index c2731f595..781fddff5 100644 --- a/.github/workflows/lint.yml +++ b/.github/workflows/lint.yml @@ -33,7 +33,7 @@ jobs: uses: actions/checkout@v4 - name: Setup Nodejs env -uses: actions/setup-node@v4.0.1 +uses: actions/setup-node@v4.0.2 with: node-version: '12'
(apisix) branch master updated: feat: add redis and redis-cluster in limit-conn (#10866)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 7e907a565 feat: add redis and redis-cluster in limit-conn (#10866)
7e907a565 is described below
commit 7e907a565b9302e70daf294398722377fd64c482
Author: theweakgod <1031205...@qq.com>
AuthorDate: Wed Feb 7 17:48:03 2024 +0800
feat: add redis and redis-cluster in limit-conn (#10866)
---
apisix/cli/ngx_tpl.lua | 1 +
apisix/plugins/limit-conn.lua | 36 +-
apisix/plugins/limit-conn/init.lua | 33 +-
.../limit-conn/limit-conn-redis-cluster.lua| 78 ++
apisix/plugins/limit-conn/limit-conn-redis.lua | 85 +++
apisix/plugins/limit-conn/util.lua | 81 +++
apisix/plugins/limit-count/init.lua| 60 +-
.../limit-count/limit-count-redis-cluster.lua | 38 +-
apisix/plugins/limit-count/limit-count-redis.lua | 48 +-
apisix/utils/redis-schema.lua | 81 +++
.../limit-count-redis.lua => utils/redis.lua} | 73 +-
.../rediscluster.lua} | 73 +-
conf/config-default.yaml | 1 +
docs/en/latest/plugins/limit-conn.md | 35 +-
docs/zh/latest/plugins/limit-conn.md | 35 +-
t/APISIX.pm| 1 +
t/plugin/limit-conn-redis-cluster.t| 339 +
t/plugin/limit-conn-redis.t| 810 +
18 files changed, 1607 insertions(+), 301 deletions(-)
diff --git a/apisix/cli/ngx_tpl.lua b/apisix/cli/ngx_tpl.lua
index 532debe0a..f1b10499c 100644
--- a/apisix/cli/ngx_tpl.lua
+++ b/apisix/cli/ngx_tpl.lua
@@ -289,6 +289,7 @@ http {
{% if enabled_plugins["limit-conn"] then %}
lua_shared_dict plugin-limit-conn {*
http.lua_shared_dict["plugin-limit-conn"] *};
+lua_shared_dict plugin-limit-conn-redis-cluster-slot-lock {*
http.lua_shared_dict["plugin-limit-conn-redis-cluster-slot-lock"] *};
{% end %}
{% if enabled_plugins["limit-req"] then %}
diff --git a/apisix/plugins/limit-conn.lua b/apisix/plugins/limit-conn.lua
index d8389b701..31a29199b 100644
--- a/apisix/plugins/limit-conn.lua
+++ b/apisix/plugins/limit-conn.lua
@@ -14,15 +14,18 @@
-- See the License for the specific language governing permissions and
-- limitations under the License.
--
-local core = require("apisix.core")
-local limit_conn = require("apisix.plugins.limit-conn.init")
+local core = require("apisix.core")
+local limit_conn=
require("apisix.plugins.limit-conn.init")
+local redis_schema = require("apisix.utils.redis-schema")
+local policy_to_additional_properties = redis_schema.schema
+local plugin_name = "limit-conn"
+
-local plugin_name = "limit-conn"
local schema = {
type = "object",
properties = {
-conn = {type = "integer", exclusiveMinimum = 0},
+conn = {type = "integer", exclusiveMinimum = 0}, --
limit.conn max
burst = {type = "integer", minimum = 0},
default_conn_delay = {type = "number", exclusiveMinimum = 0},
only_use_default_delay = {type = "boolean", default = false},
@@ -31,6 +34,11 @@ local schema = {
enum = {"var", "var_combination"},
default = "var",
},
+policy = {
+type = "string",
+enum = {"redis", "redis-cluster", "local"},
+default = "local",
+},
rejected_code = {
type = "integer", minimum = 200, maximum = 599, default = 503
},
@@ -39,7 +47,25 @@ local schema = {
},
allow_degradation = {type = "boolean", default = false}
},
-required = {"conn", "burst", "default_conn_delay", "key"}
+required = {"conn", "burst", "default_conn_delay", "key"},
+["if"] = {
+properties = {
+policy = {
+enum = {"redis"},
+},
+},
+},
+["then"] = policy_to_additional_properties.redis,
+["else"] = {
+["if"] = {
+properties = {
+policy = {
+enum = {"redis-cluster"},
+},
+},
+},
+["then"] = policy_to_additional_properties["redis-cluster"],
+}
(apisix) branch master updated: docs: add docs for building apisix development environment in Docker (#10899)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new abc86a539 docs: add docs for building apisix development environment
in Docker (#10899)
abc86a539 is described below
commit abc86a539eb656210fa6a128a579451735fe98ff
Author: Vacant
AuthorDate: Mon Feb 5 21:46:49 2024 +0800
docs: add docs for building apisix development environment in Docker
(#10899)
---
.../images/update-docker-desktop-file-sharing.png | Bin 0 -> 166679 bytes
.../latest/build-apisix-dev-environment-on-mac.md | 94 +
docs/en/latest/config.json | 4 +
.../latest/build-apisix-dev-environment-on-mac.md | 94 +
docs/zh/latest/config.json | 4 +
example/build-dev-image.dockerfile | 32 +++
6 files changed, 228 insertions(+)
diff --git a/docs/assets/images/update-docker-desktop-file-sharing.png
b/docs/assets/images/update-docker-desktop-file-sharing.png
new file mode 100644
index 0..3ac57
Binary files /dev/null and
b/docs/assets/images/update-docker-desktop-file-sharing.png differ
diff --git a/docs/en/latest/build-apisix-dev-environment-on-mac.md
b/docs/en/latest/build-apisix-dev-environment-on-mac.md
new file mode 100644
index 0..fb31e5adf
--- /dev/null
+++ b/docs/en/latest/build-apisix-dev-environment-on-mac.md
@@ -0,0 +1,94 @@
+---
+id: build-apisix-dev-environment-on-mac
+title: Build development environment on Mac
+description: This paper introduces how to use Docker to quickly build the
development environment of API gateway Apache APISIX on Mac.
+---
+
+
+
+If you want to quickly build and develop APISIX on your Mac platform, you can
refer to this tutorial.
+
+:::note
+
+This tutorial is suitable for situations where you need to quickly start
development on the Mac platform, if you want to go further and have a better
development experience, the better choice is the Linux-based virtual machine,
or directly use this kind of system as your development environment.
+
+You can see the specific supported systems
[here](install-dependencies.md#install).
+
+:::
+
+## Quick Setup of Apache APISIX Development Environment
+
+### Implementation Idea
+
+We use Docker to build the test environment of Apache APISIX. When the
container starts, we can mount the source code of Apache APISIX into the
container, and then we can build and run test cases in the container.
+
+### Implementation Steps
+
+First, clone the APISIX source code, build an image that can run test cases,
and compile the Apache APISIX.
+
+```shell
+git clone https://github.com/apache/apisix.git
+cd apisix
+docker build -t apisix-dev-env -f example/build-dev-image.dockerfile .
+```
+
+Next, start Etcd:
+
+```shell
+docker run -d --name etcd-apisix --net=host pachyderm/etcd:v3.5.2
+```
+
+Mount the APISIX directory and start the development environment container:
+
+```shell
+docker run -d --name apisix-dev-env --net=host -v $(pwd):/apisix:rw
apisix-dev-env:latest
+```
+
+Finally, enter the container, build the Apache APISIX runtime, and configure
the test environment:
+
+```shell
+docker exec -it apisix-dev-env make deps
+docker exec -it apisix-dev-env ln -s /usr/bin/openresty /usr/bin/nginx
+```
+
+### Run and Stop APISIX
+
+```shell
+docker exec -it apisix-dev-env make run
+docker exec -it apisix-dev-env make stop
+```
+
+:::note
+
+If you encounter an error message like `nginx: [emerg] bind() to
unix:/apisix/logs/worker_events.sock failed (95: Operation not supported)`
while running `make run`, please use this solution.
+
+Change the `File Sharing` settings of your Docker-Desktop:
+
+
+
+Changing to either `gRPC FUSE` or `osxfs` can resolve this issue.
+
+:::
+
+### Run Specific Test Cases
+
+```shell
+docker exec -it apisix-dev-env prove t/admin/routes.t
+```
diff --git a/docs/en/latest/config.json b/docs/en/latest/config.json
index 480f63489..fd9a43f2f 100644
--- a/docs/en/latest/config.json
+++ b/docs/en/latest/config.json
@@ -243,6 +243,10 @@
"type": "doc",
"id": "building-apisix"
},
+{
+ "type": "doc",
+ "id": "build-apisix-dev-environment-on-mac"
+},
{
"type": "doc",
"id": "support-fips-in-apisix"
diff --git a/docs/zh/latest/build-apisix-dev-environment-on-mac.md
b/docs/zh/latest/build-apisix-dev-environment-on-mac.md
new file mode 100644
index 0..e38c0b391
--- /dev/null
+++ b/docs/zh/latest/build-apisix-dev-environment-on-mac.md
@@ -0,0 +1,94 @@
+---
+id: build-apisix-dev-environment-on
(apisix) branch master updated: feat: allow configuring allow-headers in grpc-web plugin (#10904)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new d68c2438c feat: allow configuring allow-headers in grpc-web plugin
(#10904)
d68c2438c is described below
commit d68c2438cba0fe66edc4e05cb02fb5691ced3cf4
Author: baiyun <337531...@qq.com>
AuthorDate: Mon Feb 5 21:45:00 2024 +0800
feat: allow configuring allow-headers in grpc-web plugin (#10904)
---
apisix/plugins/grpc-web.lua| 14 --
docs/en/latest/plugins/grpc-web.md | 6 +++
docs/zh/latest/plugins/grpc-web.md | 6 +++
t/plugin/grpc-web.t| 94 ++
4 files changed, 117 insertions(+), 3 deletions(-)
diff --git a/apisix/plugins/grpc-web.lua b/apisix/plugins/grpc-web.lua
index 5771604e7..260e84c4e 100644
--- a/apisix/plugins/grpc-web.lua
+++ b/apisix/plugins/grpc-web.lua
@@ -32,6 +32,7 @@ local CONTENT_ENCODING_BINARY = "binary"
local DEFAULT_CORS_ALLOW_ORIGIN = "*"
local DEFAULT_CORS_ALLOW_METHODS = ALLOW_METHOD_POST
local DEFAULT_CORS_ALLOW_HEADERS = "content-type,x-grpc-web,x-user-agent"
+local DEFAULT_CORS_EXPOSE_HEADERS = "grpc-message,grpc-status"
local DEFAULT_PROXY_CONTENT_TYPE = "application/grpc"
@@ -39,7 +40,14 @@ local plugin_name = "grpc-web"
local schema = {
type = "object",
-properties = {},
+properties = {
+cors_allow_headers = {
+description =
+"multiple header use ',' to split. default:
content-type,x-grpc-web,x-user-agent.",
+type = "string",
+default = DEFAULT_CORS_ALLOW_HEADERS
+}
+}
}
local grpc_web_content_encoding = {
@@ -125,14 +133,14 @@ function _M.header_filter(conf, ctx)
local method = core.request.get_method()
if method == ALLOW_METHOD_OPTIONS then
core.response.set_header("Access-Control-Allow-Methods",
DEFAULT_CORS_ALLOW_METHODS)
-core.response.set_header("Access-Control-Allow-Headers",
DEFAULT_CORS_ALLOW_HEADERS)
+core.response.set_header("Access-Control-Allow-Headers",
conf.cors_allow_headers)
end
if not ctx.cors_allow_origins then
core.response.set_header("Access-Control-Allow-Origin",
DEFAULT_CORS_ALLOW_ORIGIN)
end
core.response.set_header("Content-Type", ctx.grpc_web_mime)
-core.response.set_header("Access-Control-Expose-Headers",
"grpc-message,grpc-status")
+core.response.set_header("Access-Control-Expose-Headers",
DEFAULT_CORS_EXPOSE_HEADERS)
end
function _M.body_filter(conf, ctx)
diff --git a/docs/en/latest/plugins/grpc-web.md
b/docs/en/latest/plugins/grpc-web.md
index a834e0e95..a43ef64c1 100644
--- a/docs/en/latest/plugins/grpc-web.md
+++ b/docs/en/latest/plugins/grpc-web.md
@@ -32,6 +32,12 @@ description: This document contains information about the
Apache APISIX grpc-web
The `grpc-web` Plugin is a proxy Plugin that can process [gRPC
Web](https://github.com/grpc/grpc-web) requests from JavaScript clients to a
gRPC service.
+## Attributes
+
+| Name| Type| Required | Default
| Description
|
+|-|-|--|-|--|
+| cors_allow_headers | string | False|
"content-type,x-grpc-web,x-user-agent" | Headers in the request allowed when
accessing a cross-origin resource. Use `,` to add multiple headers. |
+
## Enable Plugin
You can enable the `grpc-web` Plugin on a specific Route as shown below:
diff --git a/docs/zh/latest/plugins/grpc-web.md
b/docs/zh/latest/plugins/grpc-web.md
index 48077a1c2..76f4d3dcf 100644
--- a/docs/zh/latest/plugins/grpc-web.md
+++ b/docs/zh/latest/plugins/grpc-web.md
@@ -32,6 +32,12 @@ description: 本文介绍了关于 Apache APISIX `grpc-web` 插件的基本信
`grpc-web` 插件是一个代理插件,可以处理从 JavaScript 客户端到 gRPC Service 的 [gRPC
Web](https://github.com/grpc/grpc-web) 请求。
+## 属性
+
+| 名称 | 类型| 必选项 | 默认值
| 描述 |
+|-| ---
||-||
+| cors_allow_headers | string | 否 | "content-type,x-grpc-web,x-user-agent"
| 允许跨域访问时请求方携带哪些非 `CORS 规范` 以外的 Header。如果你有多个 Header,请使用 `,` 分割。 |
+
## 启用插件
你可以通过如下命令在指定路由上启用 `gRPC-web` 插件:
diff --git a/t/plugin/grpc-web.t b/t/plugin/grpc-we
(apisix) branch master updated: feat: Add forward-auth plugin exception configuration status_on_error (#10898)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 3faeff617 feat: Add forward-auth plugin exception configuration
status_on_error (#10898)
3faeff617 is described below
commit 3faeff6178bb7b24aa79da19878ba9607af37eb0
Author: baiyun <337531...@qq.com>
AuthorDate: Fri Feb 2 13:56:21 2024 +0800
feat: Add forward-auth plugin exception configuration status_on_error
(#10898)
---
apisix/plugins/forward-auth.lua| 5 +++--
docs/en/latest/plugins/forward-auth.md | 1 +
docs/zh/latest/plugins/forward-auth.md | 1 +
t/plugin/forward-auth.t| 33 +++--
4 files changed, 36 insertions(+), 4 deletions(-)
diff --git a/apisix/plugins/forward-auth.lua b/apisix/plugins/forward-auth.lua
index 6d4454a58..69dc48de6 100644
--- a/apisix/plugins/forward-auth.lua
+++ b/apisix/plugins/forward-auth.lua
@@ -24,6 +24,7 @@ local schema = {
properties = {
uri = {type = "string"},
allow_degradation = {type = "boolean", default = false},
+status_on_error = {type = "integer", minimum = 200, maximum = 599,
default = 403},
ssl_verify = {
type = "boolean",
default = true,
@@ -131,8 +132,8 @@ function _M.access(conf, ctx)
if not res and conf.allow_degradation then
return
elseif not res then
-core.log.error("failed to process forward auth, err: ", err)
-return 403
+core.log.warn("failed to process forward auth, err: ", err)
+return conf.status_on_error
end
if res.status >= 300 then
diff --git a/docs/en/latest/plugins/forward-auth.md
b/docs/en/latest/plugins/forward-auth.md
index 2fe89d39b..4b8d138c9 100644
--- a/docs/en/latest/plugins/forward-auth.md
+++ b/docs/en/latest/plugins/forward-auth.md
@@ -49,6 +49,7 @@ This Plugin moves the authentication and authorization logic
to a dedicated exte
| keepalive_timeout | integer | False| 6ms | [1000, ...]ms |
Idle time after which the connection is closed.
|
| keepalive_pool| integer | False| 5 | [1, ...]ms |
Connection pool limit.
|
| allow_degradation | boolean | False| false ||
When set to `true`, allows authentication to be skipped when authentication
server is unavailable. |
+| status_on_error | integer | False| 403 | [200,...,599] |
Sets the HTTP status that is returned to the client when there is a network
error to the authorization service. The default status is “403” (HTTP
Forbidden). |
## Data definition
diff --git a/docs/zh/latest/plugins/forward-auth.md
b/docs/zh/latest/plugins/forward-auth.md
index a7babfe46..82aa5f4c1 100644
--- a/docs/zh/latest/plugins/forward-auth.md
+++ b/docs/zh/latest/plugins/forward-auth.md
@@ -48,6 +48,7 @@ description: 本文介绍了关于 Apache APISIX `forward-auth` 插件的基本
| keepalive_timeout | integer | 否| 6ms | [1000, ...]ms |
长连接超时时间。
|
| keepalive_pool| integer | 否| 5 | [1, ...]ms |
长连接池大小。
|
| allow_degradation | boolean | 否| false || 当设置为
`true` 时,允许在身份验证服务器不可用时跳过身份验证。 |
+| status_on_error | boolean | 否| 403 | [200,...,599] |
设置授权服务出现网络错误时返回给客户端的 HTTP 状态。默认状态为“403”。 |
## 数据定义
diff --git a/t/plugin/forward-auth.t b/t/plugin/forward-auth.t
index 25e4fe652..b22260c5f 100644
--- a/t/plugin/forward-auth.t
+++ b/t/plugin/forward-auth.t
@@ -285,6 +285,26 @@ property "request_method" validation failed: matches none
of the enum values
"upstream_id": "u1",
"uri": "/large-body"
}]],
+},
+{
+url = "/apisix/admin/routes/8",
+data = [[{
+"plugins": {
+"forward-auth": {
+"uri": "http://127.39.40.1:/auth";,
+"request_headers": ["Authorization"],
+"upstream_headers": ["X-User-ID"],
+"client_headers": ["Location"],
+
(apisix) branch master updated: chore: remove create-ssl.py (#10889)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 40a4f8a19 chore: remove create-ssl.py (#10889)
40a4f8a19 is described below
commit 40a4f8a19dc9a34feb97b0c3a47285bbdc3ccdc9
Author: baiyun <337531...@qq.com>
AuthorDate: Wed Jan 31 23:54:16 2024 +0800
chore: remove create-ssl.py (#10889)
---
t/cli/test_tls_over_tcp.sh | 8 +++-
utils/create-ssl.py| 41 -
2 files changed, 7 insertions(+), 42 deletions(-)
diff --git a/t/cli/test_tls_over_tcp.sh b/t/cli/test_tls_over_tcp.sh
index 5d378ce6a..5f95f29db 100755
--- a/t/cli/test_tls_over_tcp.sh
+++ b/t/cli/test_tls_over_tcp.sh
@@ -39,7 +39,13 @@ nginx_config:
make run
sleep 0.1
- ./utils/create-ssl.py t/certs/mtls_server.crt t/certs/mtls_server.key test.com
+curl http://127.0.0.1:9180/apisix/admin/ssls/1 \
+-H 'X-API-KEY: edd1c9f034335f136f87ad84b625c8f1' -X PUT -d '
+{
+ "cert" : "'"$(cat t/certs/mtls_server.crt)"'",
+ "key": "'"$(cat t/certs/mtls_server.key)"'",
+ "snis": ["test.com"]
+}'
curl -k -i http://127.0.0.1:9180/apisix/admin/stream_routes/1 \
-H 'X-API-KEY: edd1c9f034335f136f87ad84b625c8f1' -X PUT -d \
diff --git a/utils/create-ssl.py b/utils/create-ssl.py
deleted file mode 100755
index e8a3daa33..0
--- a/utils/create-ssl.py
+++ /dev/null
@@ -1,41 +0,0 @@
-#!/usr/bin/env python
-# coding: utf-8
-#
-# Licensed to the Apache Software Foundation (ASF) under one or more
-# contributor license agreements. See the NOTICE file distributed with
-# this work for additional information regarding copyright ownership.
-# The ASF licenses this file to You under the Apache License, Version 2.0
-# (the "License"); you may not use this file except in compliance with
-# the License. You may obtain a copy of the License at
-#
-# http://www.apache.org/licenses/LICENSE-2.0
-#
-# Unless required by applicable law or agreed to in writing, software
-# distributed under the License is distributed on an "AS IS" BASIS,
-# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
-# See the License for the specific language governing permissions and
-# limitations under the License.
-#
-import sys
-# sudo pip install requests
-import requests
-
-# Usage: ./create-ssl.py t.crt t.key test.com
-if len(sys.argv) <= 3:
-print("bad argument")
-sys.exit(1)
-with open(sys.argv[1]) as f:
-cert = f.read()
-with open(sys.argv[2]) as f:
-key = f.read()
-sni = sys.argv[3]
-api_key = "edd1c9f034335f136f87ad84b625c8f1"
-resp = requests.put("http://127.0.0.1:9180/apisix/admin/ssls/1";, json={
-"cert": cert,
-"key": key,
-"snis": [sni],
-}, headers={
-"X-API-KEY": api_key,
-})
-print(resp.status_code)
-print(resp.text)
(apisix) branch master updated (9ed823e29 -> 43a567cc2)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a change to branch master in repository https://gitbox.apache.org/repos/asf/apisix.git from 9ed823e29 chore: hi 2024 (#10881) add 43a567cc2 feat: support built-in variables in response_headers in mocking plugin (#10872) No new revisions were added by this update. Summary of changes: apisix/plugins/mocking.lua | 1 + t/plugin/mocking.t | 39 +++ 2 files changed, 40 insertions(+)
(apisix) branch master updated: docs: jwe-decrypt secret length must be 32 chars (#10883)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 6bb6069f6 docs: jwe-decrypt secret length must be 32 chars (#10883)
6bb6069f6 is described below
commit 6bb6069f6b305110c10823fe776502ef71cc401e
Author: Vacant
AuthorDate: Wed Jan 31 17:25:07 2024 +0800
docs: jwe-decrypt secret length must be 32 chars (#10883)
---
docs/en/latest/plugins/jwe-decrypt.md | 12 ++--
docs/zh/latest/plugins/jwe-decrypt.md | 12 ++--
2 files changed, 12 insertions(+), 12 deletions(-)
diff --git a/docs/en/latest/plugins/jwe-decrypt.md
b/docs/en/latest/plugins/jwe-decrypt.md
index 155b793e4..9969094af 100644
--- a/docs/en/latest/plugins/jwe-decrypt.md
+++ b/docs/en/latest/plugins/jwe-decrypt.md
@@ -38,11 +38,11 @@ This Plugin adds an endpoint `/apisix/plugin/jwe/encrypt`
for JWE encryption. Fo
For Consumer:
-| Name | Type| Required
| Default | Valid values| Description
|
-|---|-|---|-|-|-|
-| key | string | True
| | | Unique key for a Consumer.
|
-| secret| string | True
| | | The decryption key. The key could
be saved in a secret manager using the [Secret](../terminology/secret.md)
resource. |
-| is_base64_encoded | boolean | False
| false | | Set to true if the secret is
base64 encoded.
|
+| Name | Type| Required
| Default | Valid values| Description
|
+|---|-|---|-|-|--|
+| key | string | True
| | | Unique key for a Consumer.
|
+| secret| string | True
| | | The decryption key. Must be 32
characters. The key could be saved in a secret manager using the
[Secret](../terminology/secret.md) resource. |
+| is_base64_encoded | boolean | False
| false | | Set to true if the secret is
base64 encoded.
|
For Route:
@@ -63,7 +63,7 @@ curl http://127.0.0.1:9180/apisix/admin/consumers -H
'X-API-KEY: edd1c9f034335f1
"plugins": {
"jwe-decrypt": {
"key": "user-key",
-"secret": "key-length-must-be-at-least-32-chars"
+"secret": "-secret-length-must-be-32-chars-"
}
}
}'
diff --git a/docs/zh/latest/plugins/jwe-decrypt.md
b/docs/zh/latest/plugins/jwe-decrypt.md
index 7ef1f295b..ce5c98fd6 100644
--- a/docs/zh/latest/plugins/jwe-decrypt.md
+++ b/docs/zh/latest/plugins/jwe-decrypt.md
@@ -38,11 +38,11 @@ description: 本文档包含了关于 APISIX jwe-decrypt 插件的相关信息
Consumer 配置:
-| 名称 | 类型 | 必选项 | 默认值 | 有效值 | 描述
|
-|---|-|---|---|-|--|
-| key | string | True | | | Consumer 的唯一 key
(apisix) branch master updated: ci: new test case for https health check (#10575)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new fc5a9b0d7 ci: new test case for https health check (#10575)
fc5a9b0d7 is described below
commit fc5a9b0d7395aee2fe45d9a28427ac1f2179a3ab
Author: Sn0rt
AuthorDate: Tue Dec 5 12:50:43 2023 +0800
ci: new test case for https health check (#10575)
---
t/node/healthcheck-https.t | 341 +
1 file changed, 341 insertions(+)
diff --git a/t/node/healthcheck-https.t b/t/node/healthcheck-https.t
new file mode 100644
index 0..b1f7b7ba0
--- /dev/null
+++ b/t/node/healthcheck-https.t
@@ -0,0 +1,341 @@
+#
+# Licensed to the Apache Software Foundation (ASF) under one or more
+# contributor license agreements. See the NOTICE file distributed with
+# this work for additional information regarding copyright ownership.
+# The ASF licenses this file to You under the Apache License, Version 2.0
+# (the "License"); you may not use this file except in compliance with
+# the License. You may obtain a copy of the License at
+#
+# http://www.apache.org/licenses/LICENSE-2.0
+#
+# Unless required by applicable law or agreed to in writing, software
+# distributed under the License is distributed on an "AS IS" BASIS,
+# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+# See the License for the specific language governing permissions and
+# limitations under the License.
+#
+use t::APISIX 'no_plan';
+
+no_root_location();
+repeat_each(1);
+log_level('info');
+no_root_location();
+no_shuffle();
+
+add_block_preprocessor(sub {
+my ($block) = @_;
+
+if (!$block->http_config) {
+my $http_config = <<'_EOC_';
+server {
+listen 8765 ssl;
+ssl_certificate ../../certs/mtls_server.crt;
+ssl_certificate_key ../../certs/mtls_server.key;
+ssl_client_certificate ../../certs/mtls_ca.crt;
+
+location /ping {
+return 200 '8765';
+}
+
+location /healthz {
+return 200 'ok';
+}
+}
+
+server {
+listen 8766 ssl;
+ssl_certificate ../../certs/mtls_server.crt;
+ssl_certificate_key ../../certs/mtls_server.key;
+ssl_client_certificate ../../certs/mtls_ca.crt;
+
+location /ping {
+return 200 '8766';
+}
+
+location /healthz {
+return 500;
+}
+}
+
+
+server {
+listen 8767 ssl;
+ssl_certificate ../../certs/mtls_server.crt;
+ssl_certificate_key ../../certs/mtls_server.key;
+ssl_client_certificate ../../certs/mtls_ca.crt;
+
+location /ping {
+return 200 '8766';
+}
+
+location /healthz {
+return 200 'ok';
+}
+}
+
+server {
+listen 8768 ssl;
+ssl_certificate ../../certs/mtls_server.crt;
+ssl_certificate_key ../../certs/mtls_server.key;
+ssl_client_certificate ../../certs/mtls_ca.crt;
+
+location /ping {
+return 200 '8766';
+}
+
+location /healthz {
+return 500;
+}
+}
+
+_EOC_
+$block->set_value("http_config", $http_config);
+}
+
+if (!$block->request) {
+$block->set_value("request", "GET /t");
+}
+
+});
+
+run_tests;
+
+__DATA__
+
+=== TEST 1: https health check (two health nodes)
+--- config
+location /t {
+lua_ssl_trusted_certificate ../../certs/mtls_ca.crt;
+content_by_lua_block {
+local t = require("lib.test_admin")
+local core = require("apisix.core")
+local cert = t.read_file("t/certs/mtls_client.crt")
+local key = t.read_file("t/certs/mtls_client.key")
+local data = {
+uri = "/ping",
+upstream = {
+scheme = "https",
+nodes = {
+["127.0.0.1:8765"] = 1,
+["127.0.0.1:8767"] = 1
+},
+tls = {
+client_cert = cert,
+client_key = key
+},
+retries = 2,
+checks = {
+active = {
+type = "https",
+http_path = "/healthz",
+https_verify_certificate = false,
+healthy = {
+interval = 1,
+successes = 1
+},
+unhealthy = {
+interval = 1,
+http_failures = 1
+},
+
[apisix-website] branch master updated: blog: Add Down the rabbit hole of an Apache APISIX plugin post (#1692)
This is an automated email from the ASF dual-hosted git repository. shreemaanabhishek pushed a commit to branch master in repository https://gitbox.apache.org/repos/asf/apisix-website.git The following commit(s) were added to refs/heads/master by this push: new b81007409bd blog: Add Down the rabbit hole of an Apache APISIX plugin post (#1692) b81007409bd is described below commit b81007409bd22a21a6d00df8661a788b525a8a24 Author: Nicolas Fränkel AuthorDate: Thu Oct 5 12:12:15 2023 +0200 blog: Add Down the rabbit hole of an Apache APISIX plugin post (#1692) --- .../blog/2023/09/28/rabbit-hole-apisix-plugin.md | 130 + 1 file changed, 130 insertions(+) diff --git a/blog/en/blog/2023/09/28/rabbit-hole-apisix-plugin.md b/blog/en/blog/2023/09/28/rabbit-hole-apisix-plugin.md new file mode 100644 index 000..396afa83de7 --- /dev/null +++ b/blog/en/blog/2023/09/28/rabbit-hole-apisix-plugin.md @@ -0,0 +1,130 @@ +--- +title: Down the rabbit hole of an Apache APISIX plugin +authors: + - name: Nicolas Fränkel +title: Author +url: https://github.com/nfrankel +image_url: https://avatars.githubusercontent.com/u/752258 +keywords: + - DevOps + - Analysis + - plugin + - Lua +description: > + My demo, Evolving your APIs, features a custom Apache APISIX plugin. + I believe that the process of creating a custom plugin is relatively well-documented. + However, I wanted to check the parameters of the `_M.access(conf, ctx)` function, especially the `ctx` one. +tags: [Ecosystem] +image: https://static.apiseven.com/uploads/2023/09/22/7BPpDQyu_falling-5472195.jpg +--- + +>My demo, Evolving your APIs, features a custom Apache APISIX plugin. I believe that the process of [creating a custom plugin](https://apisix.apache.org/docs/apisix/plugin-develop/) is relatively well-documented. However, I wanted to check the parameters of the `_M.access(conf, ctx)` function, especially the `ctx` one. + + + + +https://blog.frankel.ch/rabbit-hole-apisix-plugin/"; /> + + +The documentation states: + +>The `ctx` parameter caches data information related to the request. You can use `core.log.warn(core.json.encode(ctx, true))` to output it to `error.log` for viewing. + +Unfortunately, `core.log` ultimately depends on nginx's logging, and its buffer is limited in size. Thanks to my colleague [Abhishek](https://twitter.com/shreemaan_abhi) for finding [the info](http://nginx.org/en/docs/dev/development_guide.html#logging). For this reason, the `ctx` display is (heavily) truncated. I had to log data bit by bit; however, it was instructive. + +## The context + +The `ctx` parameter is a Lua table. In Lua, table data structures are used for regular indexed access (akin to arrays) and key access (like hash maps). A single `ctx` instance is used for each _request_. + +The Apache APISIX engine reads and writes data in the `ctx` table. It's responsible for forwarding the latter from plugin to plugin. In turn, each plugin can also read and write data. + +I resorted to a custom plugin to conditionally apply rate-limiting in the demo. The custom plugin is a copy-paste of the [limit-count](https://apisix.apache.org/docs/apisix/plugins/limit-count/) plugin. Note that the analysis is done in a specific context. Refrain from assuming the same data is available in your own. However, it should be a good starting point. + +## Overview of the `ctx` parameter + +The data available in the `ctx` parameter is overwhelming. To better understand it, we shall go from the more general to the more particular. Let's start from the overview. + + + +* `_plugin_name`: self-explanatory +* `conf_id`: either route ID or service ID +* `proxy_rewrite_regex_uri_capture`: data set by the [proxy-rewrite](https://github.com/apache/apisix/blob/a82a2f3c439119ade45b4afffb5a251cd7bb65d2/apisix/plugins/proxy-rewrite.lua#L46C2) plugin. +* `route_id`: route ID the plugin is applied to +* `route_name`: route name the plugin is applied to +* `real_current_req_matched_path`: URI for which matching was done +* `conf_version`: etcd-related revision - see below +* `var`: references the `ctx` object and a cache of data about the request, _e.g._, URI, method, etc. +* `matched_route`: the route that was matched based on host header/URI and/or `remote_addr`; see below +* `plugins`: pairs of plugin/data - see below + +## Matched route + +The `matched_route` row is a complex data tree that deserves a detailed description. + + + +* `key`: access key in the `etcd` datastore +* `created_index`, `modifiedIndex` and `orig_modifiedIndex`: these attributes are related to etcd and how it stores metadata associated with revisions. Different revisions of a single key are logged in the `cre
[apisix] branch master updated: docs: Update admin-api.md (#10056)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 9a11b9025 docs: Update admin-api.md (#10056)
9a11b9025 is described below
commit 9a11b902556b681b138d4aba23fe0a0855db2840
Author: jaw163 <134787269+jaw...@users.noreply.github.com>
AuthorDate: Mon Aug 21 16:53:16 2023 +0100
docs: Update admin-api.md (#10056)
* Update admin-api.md
Added note on ID syntax
* docs: Update admin-api.md
* Update admin-api.md
Periods can be added as special characters too
---
docs/en/latest/admin-api.md | 8
1 file changed, 8 insertions(+)
diff --git a/docs/en/latest/admin-api.md b/docs/en/latest/admin-api.md
index 787a61e98..e34468eac 100644
--- a/docs/en/latest/admin-api.md
+++ b/docs/en/latest/admin-api.md
@@ -277,6 +277,10 @@ curl
'http://127.0.0.1:9180/apisix/admin/routes?name=test&uri=foo&label=' \
Route resource request address: /apisix/admin/routes/{id}?ttl=0
+### Quick Note on ID Syntax
+
+ID's as a text string must be of a length between 1 and 64 characters and they
should only contain uppercase, lowercase, numbers and no special characters
apart from dashes ( - ), periods ( . ) and underscores ( _ ). For integer
values they simply must have a minimum character count of 1.
+
### Request Methods
| Method | Request URI | Request Body | Description
|
@@ -871,6 +875,8 @@ An Upstream configuration can be directly bound to a Route
or a Service, but the
Upstream resource request address: /apisix/admin/upstreams/{id}
+For notes on ID syntax please refer to: [ID Syntax](#quick-note-on-id-syntax)
+
### Request Methods
| Method | Request URI | Request Body | Description
|
@@ -1180,6 +1186,8 @@ Currently, the response is returned from etcd.
SSL resource request address: /apisix/admin/ssls/{id}
+For notes on ID syntax please refer to: [ID Syntax](#quick-note-on-id-syntax)
+
### Request Methods
| Method | Request URI| Request Body | Description
|
[apisix] branch master updated: ci: fix a bug that can not open nginx.pid (#10061)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 1fd261319 ci: fix a bug that can not open nginx.pid (#10061)
1fd261319 is described below
commit 1fd2613198e7640018ea5576d9935b828e25fb9f
Author: Ruidong-X
AuthorDate: Mon Aug 21 13:18:46 2023 +0800
ci: fix a bug that can not open nginx.pid (#10061)
---
ci/linux_apisix_master_luarocks_runner.sh | 7 +++
1 file changed, 7 insertions(+)
diff --git a/ci/linux_apisix_master_luarocks_runner.sh
b/ci/linux_apisix_master_luarocks_runner.sh
index 8931ad82c..3e99baf34 100755
--- a/ci/linux_apisix_master_luarocks_runner.sh
+++ b/ci/linux_apisix_master_luarocks_runner.sh
@@ -52,6 +52,13 @@ script() {
sudo PATH=$PATH apisix init
sudo PATH=$PATH apisix start
sudo PATH=$PATH apisix quit
+for i in {1..10}
+do
+if [ ! -f /usr/local/apisix/logs/nginx.pid ];then
+break
+fi
+sleep 0.3
+done
sudo PATH=$PATH apisix start
sudo PATH=$PATH apisix stop
[apisix] branch master updated: feat: remove rust dependency by rollback lua-resty-ldap on master (#9936)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new ac3992f55 feat: remove rust dependency by rollback lua-resty-ldap on
master (#9936)
ac3992f55 is described below
commit ac3992f55c5e2e93f685a4295149faa6eef48284
Author: Ashish Tiwari
AuthorDate: Mon Aug 21 09:09:13 2023 +0530
feat: remove rust dependency by rollback lua-resty-ldap on master (#9936)
* feat: remove rust dependency by rollback lua-resty-ldap on master
Signed-off-by: revolyssup
* fix comma in rockspec
Signed-off-by: revolyssup
* refactor apisix for ldap0.1
Signed-off-by: Ashish Tiwari
-
Signed-off-by: revolyssup
Signed-off-by: Ashish Tiwari
---
Makefile | 2 +-
apisix/plugins/ldap-auth.lua | 38 +++---
rockspec/apisix-master-0.rockspec | 2 +-
3 files changed, 21 insertions(+), 21 deletions(-)
diff --git a/Makefile b/Makefile
index 52dd4b826..c6979cd6f 100644
--- a/Makefile
+++ b/Makefile
@@ -158,7 +158,7 @@ check-rust:
### deps : Installing dependencies
.PHONY: deps
-deps: check-rust runtime
+deps: runtime
$(eval ENV_LUAROCKS_VER := $(shell $(ENV_LUAROCKS) --version | grep -E
-o "luarocks [0-9]+."))
@if [ '$(ENV_LUAROCKS_VER)' = 'luarocks 3.' ]; then \
mkdir -p ~/.luarocks; \
diff --git a/apisix/plugins/ldap-auth.lua b/apisix/plugins/ldap-auth.lua
index 41156c1bf..11f205c6b 100644
--- a/apisix/plugins/ldap-auth.lua
+++ b/apisix/plugins/ldap-auth.lua
@@ -18,7 +18,7 @@ local core = require("apisix.core")
local ngx = ngx
local ngx_re = require("ngx.re")
local consumer_mod = require("apisix.consumer")
-local ok, ldap_cli = pcall(require, "resty.ldap.client")
+local ldap = require("resty.ldap")
local schema = {
type = "object",
@@ -100,11 +100,6 @@ local function extract_auth_header(authorization)
end
function _M.rewrite(conf, ctx)
-if not ok then -- ensure rasn library loaded
-core.log.error("failed to load lua-resty-ldap lib: ", ldap_cli)
-return 501
-end
-
core.log.info("plugin rewrite phase, conf: ", core.json.delay_encode(conf))
-- 1. extract authorization from header
@@ -115,31 +110,36 @@ function _M.rewrite(conf, ctx)
end
local user, err = extract_auth_header(auth_header)
-if err then
-core.log.warn(err)
+if err or not user then
+if err then
+ core.log.warn(err)
+else
+ core.log.warn("nil user")
+end
return 401, { message = "Invalid authorization in request" }
end
-- 2. try authenticate the user against the ldap server
local ldap_host, ldap_port = core.utils.parse_addr(conf.ldap_uri)
-local ldap_client = ldap_cli:new(ldap_host, ldap_port, {
+local ldapconf = {
+timeout = 1,
start_tls = false,
+ldap_host = ldap_host,
+ldap_port = ldap_port or 389,
ldaps = conf.use_tls,
-ssl_verify = conf.tls_verify,
-socket_timeout = 1,
-keepalive_pool_name = ldap_host .. ":" .. ldap_port .. "_ldapauth"
-.. (conf.use_tls and "_tls" or ""),
-keepalive_pool_size = 5,
-keepalive_timeout = 6,
-})
-
-local user_dn = conf.uid .. "=" .. user.username .. "," .. conf.base_dn
-local res, err = ldap_client:simple_bind(user_dn, user.password)
+tls_verify = conf.tls_verify,
+base_dn = conf.base_dn,
+attribute = conf.uid,
+keepalive = 6,
+}
+local res, err = ldap.ldap_authenticate(user.username, user.password,
ldapconf)
if not res then
core.log.warn("ldap-auth failed: ", err)
return 401, { message = "Invalid user authorization" }
end
+local user_dn = conf.uid .. "=" .. user.username .. "," .. conf.base_dn
+
-- 3. Retrieve consumer for authorization plugin
local consumer_conf = consumer_mod.plugin(plugin_name)
if not consumer_conf then
diff --git a/rockspec/apisix-master-0.rockspec
b/rockspec/apisix-master-0.rockspec
index 577375082..00c67f7bc 100644
--- a/rockspec/apisix-master-0.rockspec
+++ b/rockspec/apisix-master-0.rockspec
@@ -77,7 +77,7 @@ dependencies = {
"xml2lua = 1.5-2",
"nanoid = 0.1-1",
"lua-resty-mediador = 0.1.2-1",
-"lua-resty-ldap = 0.2.2-0",
+"lua-resty-ldap = 0.1.0-0",
"lua-resty-t1k = 1.1.0"
}
[apisix] branch master updated: feat: upgrade lua dependencies (#10051)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new d424ae11e feat: upgrade lua dependencies (#10051)
d424ae11e is described below
commit d424ae11e9800ce0fca41577e78b5cba9dffd982
Author: Sn0rt
AuthorDate: Fri Aug 18 11:48:31 2023 +0800
feat: upgrade lua dependencies (#10051)
* feat: upgrade lua-resty-kafka from 0.20-0->0.22-0
Signed-off-by: Sn0rt
* feat: upgrade nginx-lua-prometheus from 0.20221218->0.20230607-1
Signed-off-by: Sn0rt
* feat: upgrade lua-protobuf from 0.4.1->0.5.0-1
Signed-off-by: Sn0rt
* feat: upgrade casbin from 1.41.5->1.41.8-1
Signed-off-by: Sn0rt
-
Signed-off-by: Sn0rt
---
rockspec/apisix-master-0.rockspec | 8
1 file changed, 4 insertions(+), 4 deletions(-)
diff --git a/rockspec/apisix-master-0.rockspec
b/rockspec/apisix-master-0.rockspec
index 0c1864765..577375082 100644
--- a/rockspec/apisix-master-0.rockspec
+++ b/rockspec/apisix-master-0.rockspec
@@ -46,14 +46,14 @@ dependencies = {
"lua-resty-session = 3.10",
"opentracing-openresty = 0.1",
"lua-resty-radixtree = 2.8.2",
-"lua-protobuf = 0.4.1",
+"lua-protobuf = 0.5.0-1",
"lua-resty-openidc = 1.7.6-3",
"luafilesystem = 1.7.0-2",
"api7-lua-tinyyaml = 0.4.2",
-"nginx-lua-prometheus = 0.20221218",
+"nginx-lua-prometheus = 0.20230607-1",
"jsonschema = 0.9.8",
"lua-resty-ipmatcher = 0.6.1",
-"lua-resty-kafka = 0.20-0",
+"lua-resty-kafka = 0.22-0",
"lua-resty-logger-socket = 2.0.1-0",
"skywalking-nginx-lua = 0.6.0",
"base64 = 1.5-2",
@@ -68,7 +68,7 @@ dependencies = {
"lua-resty-consul = 0.3-2",
"penlight = 1.13.1",
"ext-plugin-proto = 0.6.0",
-"casbin = 1.41.5",
+"casbin = 1.41.8-1",
"inspect == 3.1.1",
"lualdap = 1.2.6-1",
"lua-resty-rocketmq = 0.3.0-0",
[apisix] branch master updated: feat: upgrade resty-redis-cluster from 1.02-4->1.05-1 (#10041)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new 20bb6b27f feat: upgrade resty-redis-cluster from 1.02-4->1.05-1
(#10041)
20bb6b27f is described below
commit 20bb6b27f742e05e129490ee3da4d1eb49e58fe5
Author: Sn0rt
AuthorDate: Thu Aug 17 14:54:58 2023 +0800
feat: upgrade resty-redis-cluster from 1.02-4->1.05-1 (#10041)
Signed-off-by: Sn0rt
---
rockspec/apisix-master-0.rockspec | 2 +-
1 file changed, 1 insertion(+), 1 deletion(-)
diff --git a/rockspec/apisix-master-0.rockspec
b/rockspec/apisix-master-0.rockspec
index de763d37e..54a238a1b 100644
--- a/rockspec/apisix-master-0.rockspec
+++ b/rockspec/apisix-master-0.rockspec
@@ -59,7 +59,7 @@ dependencies = {
"base64 = 1.5-2",
"binaryheap = 0.4",
"api7-dkjson = 0.1.1",
-"resty-redis-cluster = 1.02-4",
+"resty-redis-cluster = 1.05-1",
"lua-resty-expr = 1.3.2",
"graphql = 0.0.2",
"argparse = 0.7.1-1",
[apisix] branch master updated: feat(openid-connect): add proxy_opts attribute (#9948)
This is an automated email from the ASF dual-hosted git repository.
shreemaanabhishek pushed a commit to branch master
in repository https://gitbox.apache.org/repos/asf/apisix.git
The following commit(s) were added to refs/heads/master by this push:
new b9dc8b8c0 feat(openid-connect): add proxy_opts attribute (#9948)
b9dc8b8c0 is described below
commit b9dc8b8c0c9c2d65bf8612cb848632ee1a38e40c
Author: darkSheep <49020899+darksheep...@users.noreply.github.com>
AuthorDate: Wed Aug 16 11:46:14 2023 +0800
feat(openid-connect): add proxy_opts attribute (#9948)
* docs: add proxy_opts attribute for openid-connect.md (#9922)
* test: add proxy_opts attribute for openid-connect.md (#9922)
* feat: add proxy_opts attribute for openid-connect (#9922)
* fix: openid-connect support http(s) proxy
Signed-off-by: Sn0rt
* fix: update openid-connect doc by autocorrect
Signed-off-by: Sn0rt
* fix: new response of the 24th test case of openid-connect.t
Signed-off-by: Sn0rt
* fix: reindex: t/plugin/openid-connect.t
Signed-off-by: Sn0rt
* feat(openid-connect): add proxy_opts attribute
* feat: add proxy_opts attribute for openid-connect
* feat: add proxy_opts attribute for openid-connect
* fix: resolve doc lint
-
Signed-off-by: Sn0rt
Co-authored-by: darksheep404
Co-authored-by: Sn0rt
Co-authored-by: monkeyDluffy6017
---
apisix/plugins/openid-connect.lua| 26
docs/en/latest/plugins/openid-connect.md | 6 ++
docs/zh/latest/plugins/openid-connect.md | 7 ++
t/plugin/openid-connect3.t | 111 +++
4 files changed, 150 insertions(+)
diff --git a/apisix/plugins/openid-connect.lua
b/apisix/plugins/openid-connect.lua
index 5058eba47..927e4ddbd 100644
--- a/apisix/plugins/openid-connect.lua
+++ b/apisix/plugins/openid-connect.lua
@@ -130,6 +130,32 @@ local schema = {
"header to the request for downstream.",
type = "boolean",
default = false
+},
+proxy_opts = {
+description = "HTTP proxy server be used to access identity
server.",
+type = "object",
+properties = {
+http_proxy = {
+type = "string",
+description = "HTTP proxy like: http://proxy-server:80.";,
+},
+https_proxy = {
+type = "string",
+description = "HTTPS proxy like: http://proxy-server:80.";,
+},
+http_proxy_authorization = {
+type = "string",
+description = "Basic [base64 username:password].",
+},
+https_proxy_authorization = {
+type = "string",
+description = "Basic [base64 username:password].",
+},
+no_proxy = {
+type = "string",
+description = "Comma separated list of hosts that should
not be proxied.",
+}
+},
}
},
encrypt_fields = {"client_secret"},
diff --git a/docs/en/latest/plugins/openid-connect.md
b/docs/en/latest/plugins/openid-connect.md
index a5e015089..493370240 100644
--- a/docs/en/latest/plugins/openid-connect.md
+++ b/docs/en/latest/plugins/openid-connect.md
@@ -61,6 +61,12 @@ description: OpenID Connect allows the client to obtain user
information from th
| session | object | False|
| | When bearer_only is set to false, openid-connect will use
Authorization Code flow to authenticate on the IDP, so you need to set the
session-related configuration. |
| session.secret | string | True | Automatic
generation | 16 or more characters | The key used for session encrypt and HMAC
operation. |
| unauth_action| string | False| "auth"
| | Specify the response type on unauthenticated requests.
"auth" redirects to identity provider, "deny" results in a 401 response, "pass"
will allow the request without authentication. |
+| proxy_opts | object | False|
| | HTTP proxy server be used to access
identity server.
