Obviously, the team over at TAILS would also thoroughly comb through the code
and the Debian package to make sure it's safe for their operating system.
Essentially, that would be four major Internet Privacy Devs looking over this
project to make sure it launches on Tails OS system safely
This would be a big win for privacy and privacy advocates all agree on Monero
being the most private crypto currency there is.
Along with Tails being a very secure operating system and with the Debian team
also looking at the code to make sure everything is transparent, this just
makes sense
We need to get this on TAILS as soon as possible. This is exactly what the
Tails OS needs right now.
Whonix needs to allow The Monero Project to co-sign this Debian package and
also the devs on both sides can collaborate on how to push this into the Tails
OS list of pre-installed programs
](https://tails.boum.org/doc/anonymous_internet/unsafe_browser/index.en.html#security).
An attacker could exploit a security vulnerability in another application in
Tails to start an invisible _Unsafe Browser_ and reveal your IP address, even
if you are not using the _Unsafe Browser_.
For example
to
[68.8.0](https://www.thunderbird.net/en-US/thunderbird/68.8.0/releasenotes/).
# Fixed problems
* Make the installation of Additional Software more robust.
([#17278](https://gitlab.tails.boum.org/tails/tails/-/issues/17278))
* Clarify the error message when entering an incorrect password
This is an automated reminder.
The Tails Code of Conduct applies to this list, as any other space used
by the Tails project:
https://tails.boum.org/contribute/working_together/code_of_conduct/
Like the technical community as a whole, the Tails team and community is
made up of a mixture
Hello, dear Tails community.
We're happy to announce that the Tails GitLab instance is up and
running, and ready for you to use.
Below you'll find:
- Current status of migration
- Logging into GitLab
- SSH access info
- Contact us
- Thanks
Current status of migration
n-desktop:~#
Yep, I got your SOA record back, meaning there is no TXT record for
stigmate._domainkey.boum.org
Maybe you should fix that?
Best regards, Sebastian Nielsen
smime.p7s
Description: S/MIME Cryptographic Signature
_______
Tails-dev m
for [Universal 2nd
Factor](https://en.wikipedia.org/wiki/Universal%202nd%20Factor) USB security
keys.
* Update the list of applications in the _Favorites_ applications submenu.
To make it easier for new users to discover some of the core features of
Tails, we added _Configure persistent volume_
This release fixes [many security
vulnerabilities](https://tails.boum.org/security/Numerous_security_holes_in_4.4.1/).
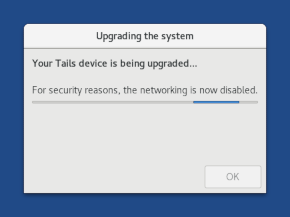
You should upgrade as soon as possible.
# New features
## Secure Boot
Tails now starts on computers with Secure Boot enabled.
If your Mac displays the following error
Tails 4.5, scheduled for April 7, will be the first version of Tails to
support Secure Boot.
You can help Tails by testing the release candidate for Tails 4.5 now.
# Secure Boot
Tails 4.5~rc1 should start on computers in UEFI mode and with Secure Boot
enabled.
# Known issues
If your Mac
://www.thunderbird.net/en-US/thunderbird/68.6.0/releasenotes/).
# Known issues
None specific to this release.
See the list of [long-standing
issues](https://tails.boum.org/support/known_issues/index.en.html).
# Get Tails 4.4.1
## To upgrade your Tails USB stick and keep your persistent storage
. ([#17323](https://redmine.tails.boum.org/code/issues/17323))
If you had a problem with Wi-Fi starting from Tails 4.1, please [let us
know](https://tails.boum.org/support/talk/index.en.html) whether your problem
was fixed or not.
For more details, read our
[changelog](https://git.tails.boum.org
))
For more details, read our
[changelog](https://git.tails.boum.org/tails/plain/debian/changelog).
# Known issues
None specific to this release.
See the list of [long-standing
issues](https://tails.boum.org/support/known_issues/index.en.html
%2FTor_Browser.html)security
level of _Tor Browser_. The _safer_ and _safest_ security levels are not
affected.
# Fixed problems
* Avoid a 2-minutes delay when restarting after doing an automatic upgrade.
(#17026)
For more details, read our
[changelog](https://git.tails.boum.org/tails/plain/debian
major pain points when using Tails:
* Until now, if your version of Tails was several months old, you sometimes
had to do 2 or more automatic upgrades in a row. For example, to upgrade from
Tails 3.12 to Tails 3.16, you first had to upgrade to Tails 3.14.
Starting with 4.2, direct automatic
> Hi, Tails contributors,
>
> - Do you read the changelog at all?
>
If thats the always-broken-in-two-halfs link in the email after an release
then yes sometimes when i am not too lazy to manually put the link together.
- If so, what do you use it for?
In 2019, we are especially proud of celebrating with you the 10 years of
Tails.
The first release of Tails, back then _amnesia_, was announced in 2009. Since
then we released 98 versions of Tails, which were used more than 25 million
times.
Here are some stories about how it all started and some
On October 7, we launched our donation campaign by explaining [why supporting
Tails is more important than
ever](https://tails.boum.org/news/2019-fundraiser/index.en.html). On October
31, we summarized [what we did in 2019 to make Tails easier to adopt by new
users](https://tails.boum.org/news
This is an automated reminder.
The Tails Code of Conduct applies to this list, as any other space used
by the Tails project:
https://tails.boum.org/contribute/working_together/code_of_conduct/
Like the technical community as a whole, the Tails team and community is
made up of a mixture
people away from using tails,
to have a hint on nationality outside the encrypted part produces risks:
- a lost stick may be assigned,
- the stick may undisclose an agents origin,
- it may be easier to decrypt once 'target language' is known,
those points are contrary to each other in what to do
to the user in the Tails subreddit that clarifies that it
is *not* associated with Tails in any official capacity. I don't want
other Reddit users in the sub thinking that advice coming from the account
is some kind of "official" word from the Tails team.
Please let me know if it was any of yo
On October 7, we started our [yearly donation
campaign](https://tails.boum.org/news/2019-fundraiser/index.en.html). Today,
we summarize what we achieved with your help in 2019.
If you liked our work in 2019, please take a minute to donate and make Tails
thrive in 2020!
# Easier adoption by new
On Mon, October 28, 2019 17:23, Mr. Lee Chiffre wrote:
>
> Electrum works again in new Tails version? Does it have Trezor support or
> does Trezor support still needed add to Tails?
>
> --
> lee.chif...@secmail.pro PGP 97F0C3AE985A191DA0556B
We are especially proud to present you Tails 4.0, the first version of Tails
based on Debian 10 (Buster). It brings new versions of most of the software
included in Tails and some important usability and performance improvements.
Tails 4.0 introduces more changes than any other version since years
TAILS BROWSER HAVE vulnerability in its javascript engine which allows full RCE
and infection with malware!!
please fix the vulnerability to protect users
in underground hacker forum it has working exploit (buffer overflow)for sale
which fully can exploit the browser of your OS
and additionaly
Tails 4.0 will be the first version of Tails based on Debian 10 (Buster). It
brings new versions of most of the software included in Tails and some
important usability and performance improvements.
You can help Tails by testing the release candidate for the upcoming version
4.0!
We are very
The mission of Tails is to empower people worldwide by giving out an operating
system that protects from surveillance and censorship.
We build liberating technology to put people in control of their digital
lives, keeping in mind that the most vulnerable and oppressed people are also
the most
Tails, a portable operating system that protects your privacy and avoids
censorship, is looking for a design contractor to create illustrations
explaining Tails.
The contractor will create illustrations to aid in communicating:
- On the homepage: what is Tails and what are its main benefits
6
SPF records for tails dev return this error:
X-SPF-Signature: permerror sebbe.eu: error in processing during lookup of
domain of boum.org: Multiple SPF or TXT records for domain.
Apparently, you have multiple SPF records:
C:\Users\Sebastian Nielsen>nslookup -type=TXT boum.org
Ser
of the Spectre
vulnerability](https://access.redhat.com/articles/4329821).
* Update most firmware packages. This should improve the support for newer
hardware (graphics, Wi-Fi, etc.).
# Fixed problems
* Fix opening the persistent storage of another Tails USB stick from the
_Files_ browser
You can help Tails by testing the second beta for the upcoming version 4.0!
We are very excited about it and cannot wait to hear your feedback :)
# What's new in 4.0~beta2?
Tails 4.0 will be the first version of Tails based on Debian 10 (Buster). As
such, it upgrades essentially all included
This is an automated reminder.
The Tails Code of Conduct applies to this list, as any other space used
by the Tails project:
https://tails.boum.org/contribute/working_together/code_of_conduct/
Like the technical community as a whole, the Tails team and community is
made up of a mixture
mobile___
Tails-dev mailing list
Tails-dev@boum.org
https://www.autistici.org/mailman/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
You can help Tails by testing the first beta for the upcoming version 4.0!
We are very excited about it and cannot wait to hear your feedback :)
# What's new in 4.0~beta1?
Tails 4.0 will be the first version of Tails based on Debian 10 (Buster). As
such, it upgrades essentially all included
This release fixes [many security
vulnerabilities](https://tails.boum.org/security/Numerous_security_holes_in_3.14.2/).
You should upgrade as soon as possible.
# Changes and upgrades
* Update _Tor Browser_ to 8.5.4.
* Update _Thunderbird_ to 60.7.2.
# Fixed problems
* Fix Tails failing
in _Tor Browser_, a [_sandbox
escape_](https://tails.boum.org/news/version_3.14.1/index.en.html#sandbox-escape),
that we couldn't fix in time for 3.14.1.
# Fixed problems
For more details, read our [changelog](https://git-
tails.immerda.ch/tails/plain/debian/changelog).
# Known issues
## Tails
/index.en.html#security_level)
are not affected because the feature of JavaScript that is affected (the
_[just-in-time
compilation](https://en.wikipedia.org/wiki/just%2Din%2Dtime%20compilation)_)
is disabled in these security levels.
Because _Tor Browser_ in Tails is [confined using
_AppArmor_](https
First of all, I love Tails. Thank you for developing this operating system, and
I want to contribute when I'm in a situation in which I can.
I have a question/suggestion regarding persistence. My ideal setup is to have a
flashdrive with Tails on it, with Tails unaware of its persistence files
This is an automated reminder.
The Tails Code of Conduct applies to this list, as any other space used
by the Tails project:
https://tails.boum.org/contribute/working_together/code_of_conduct/
Like the technical community as a whole, the Tails team and community is
made up of a mixture
Hello,
I am a long-time user of DuckDuckGo and I think this engine is great.
However, I don't understand why Tails doesn't use the default .onion version of
duckduckgo?
You propose it well in Tor Browser:
https://3g2upl4pq6kufc4m.onion/
I don't understand the logic of taking us out
___
Tails-dev mailing list
Tails-dev@boum.org
https://www.autistici.org/mailman/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
/index.en.html)_
feature.
Thanks to the removal of these less popular applications 3.14 and the removal
of some language packs in 3.13.2, Tails 3.14 is 39 MB smaller than 3.13.
## Fixed problems
* Add back the _OpenPGP Applet_ and _Pidgin_ notification icons to the top
navigation bar.

To reactivate _NoScript_ without restarting Tails, do the following:
1. Open the address about:config in _Tor Browser_.

2. Click the **I accept the risk!** button.
3. At the top of the page, search
We've been discussing possible Monero implementation into Debian and not sure
how we can proceed. AppImage, maybe?
It would be very beneficial to all three communities (Debian, Tails and Monero)
for a Monero client, either lightweight or full client to be developed for
Debian but we need some
.
There's a lot of options and commands to really lock down firefox with
firejail, it's much better than a chroot.
I looked at the applications that Tails comes with and saw that there
really was no screen recorder in there. Yes, there are a lot of tools to
work with audio and to edit videos, but what
and changes
* Update _Tor Browser_ to 8.0.8.
For more details, read our [changelog](https://git-
tails.immerda.ch/tails/plain/debian/changelog).
# Known issues
### Electrum is outdated and cannot connect to servers
**Electrum in Tails cannot connect anymore to Electrum servers.**
The version
support for the Pinyin input method.
([#11292](https://redmine.tails.boum.org/code/issues/11292))
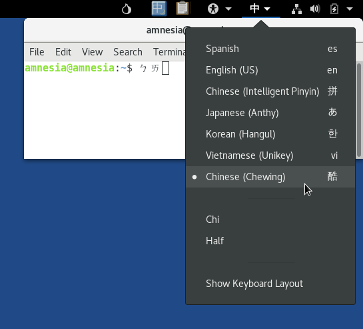
If you still have problems typing in Bopomofo or Pinyin, please let us know on
[tails-test...@boum.org](mailto:tails-test...@boum.org) (public
Hey,
Thanks for all the work you put into Tails. It is an amazing system and I
find it very useful.
I would like to report one issue however. Every second time I boot Tails,
it fails. It either displays some errors in the command line booting
screen or the letters on the normal booting screen
](https://googleprojectzero.blogspot.com/2019/02/the-curious-case-of-
convexity-confusion.html) by Google Project Zero.
# Known issues
See the list of [long-standing
issues](https://tails.boum.org/support/known_issues/index.en.html).
### Tails fails to start a second time on some computers
completely changed the installation
methods for Tails.
In short, instead of downloading an ISO image (a format originally designed
for CDs), you now download Tails as a **USB image**: an image of the data as
it needs to be written to the USB stick.
* [For macOS](https://tails.boum.org/install
You can help Tails! The first release candidate for the upcoming version 3.12
is out. We are very excited and cannot wait to hear what you think about it,
especially the new simplified USB installation method (see below). :)
# Changes
## Upgrades and changes
* Make the USB image the main
# USB images instead of ISO images
We need your help to test the simplified installation methods of Tails that we
will release with 3.12 on January 29.
The method will be much simpler and faster, especially for macOS users, but
for Windows users as well. Debian and Ubuntu users won't have
Has the Tails development considered pre-installing the full Monero client onto
the TAILS OS?
Electrum is already pre-installed, but that is only good for bitcoin, which is
not exactly anonymous.
Monero has proven to be the most private and secure cryptocurrency out there
right now.
It would
Tails needs to come pre-installed with one of the Encrypted Instant Messaging
applications for instant communication through the Tails operating system.
A few of the good programs that I would consider implementing are:
1. WickrMe
(partially open-source, Electronic Frontier Foundation has gave
is an excellent sign that Tails is important
for more people and that we are doing a good job at helping them.
We are extremely grateful to all of you who not only want to improve your
safety online, but also understand that we need your help to sustain Tails.
Being backed by a large number of people making
Hello,
I would like to help translate Tails to Portuguese, but I can't seem to
subscribe to the mailing list at
https://tails.boum.org/contribute/how/translate/#follow-up ("Erreur Liste
tails-l10n inexistante"). What should I do?
Thanks.
Sent from [ProtonMail](https://protonmail.c
[changelog](https://git-
tails.immerda.ch/tails/plain/debian/changelog).
# Known issues
None specific to this release.
See the list of [long-standing
issues](https://tails.boum.org/support/known_issues/index.en.html).
# Get Tails 3.11
* To install, follow our [installation
instructions](https
Users of cryptocurrencies have been huge supporters of Tails in all our
previous donation campaigns and we are extremely thankful to them!
As part of our on-going
[donation](https://tails.boum.org/news/2018-fundraiser/index.en.html)
[campaign](https://tails.boum.org/news/achievements_in_2018
with
encrypted files across different operating systems (Windows, Linux, and macOS).

This work was done upstream in GNOME and will be available outside of Tails in
Debian 10 (Buster
/veracrypt/index.en.html#parameters)
when unlocking _VeraCrypt_ volumes because _PIM_ won't be supported until
Tails 4.0. ([#16031](https://labs.riseup.net/code/issues/16031))
* Rename the buttons in the confirmation dialog of _Tails Installer_ to
**Install** (or **Upgrade**) and **Cancel
Every day, Tails helps thousands of people to safely use their computers
online and offline.
Tails is available for free because we believe that nobody should have to pay
to be protected from surveillance and censorship.
Tails is free software because if our source code was closed, there would
://labs.riseup.net/code/issues/15917))
* Fix displaying the help of _GNOME Videos_.
([#15841](https://labs.riseup.net/code/issues/15841))
* Uninstall _mutt_. ([#15904](https://labs.riseup.net/code/issues/15904))
For more details, read our [changelog](https://git-
tails.immerda.ch/tails/plain
Tails 3.9 is the biggest update of Tails this year!
It includes two new features on which we have been working for more than a
year:
* _Additional Software_
* _VeraCrypt_ integration
This release also fixes [many security issues](https://tails.boum.org/security
You can help Tails! The first release candidate for the upcoming version 3.9
is out. We are very excited and cannot wait to hear what you think about it :)
# Changes
## Upgrades and changes
* Integrate the _Additional Software Packages_ feature into the desktop and
revamp the interface
You can help Tails! The beta version for the [VeraCrypt support in
Tails](https://tails.boum.org/blueprint/veracrypt/) is ready for testing. We
are very excited.
# What's new in the Beta?
We worked to integrate VeraCrypt support into the existing GNOME workflow for
unlocking encrypted volumes
donations.
During the search, computers, storage media, personal items, bank account
records, and paper receipts have been confiscated. This unfortunately means
that if you have donated to Tails before October 18th 2017 using our European
bank account, your data is now in the hands of the German
](https://labs.riseup.net/code/issues/15461))
For more details, read our [changelog](https://git-
tails.immerda.ch/tails/plain/debian/changelog).
# Known issues
None specific to this release.
See the list of [long-standing
issues](https://tails.boum.org/support/known_issues/index.en.html).
# Get
log](https://git-
tails.immerda.ch/tails/plain/debian/changelog).
# Known issues
None specific to this release.
See the list of [long-standing
issues](https://tails.boum.org/support/known_issues/index.en.html).
# Get Tails 3.7.1
* To install, follow our [installation
instructions](https://tail
Hi,
Is there a way I can create and mount a persistent volume that isn't on a USB
stick? I understand that this comes with security risks - My main aim here is
develop and test tails features using virtual box or similar.
Thanks!!
Sent with [ProtonMail](https://protonmail.com) Secure Email
://www.mozilla.org/en-
US/security/advisories/mfsa2018-12/) announced on May 9.
## Fixed problems
* Allow removing the optional OpenPGP key in _WhisperBack_, in case you
specified one.
For more details, read our [changelog](https://git-
tails.immerda.ch/tails/plain/debian/changelog).
# Known issues
Hi
I live in an occupied area where we use Tails a lot.
I wonder if there is a method to verify a running live sytem?
The case is:
How to verify an USB key to be sure the installation is safe (=conform)
in an unfriendly context?
Another think:
It should be great to have checksums in the offline
, such as Tails
Verification.
For more details, read our [changelog](https://git-
tails.immerda.ch/tails/plain/debian/changelog).
See the list of [long-standing
issues](https://tails.boum.org/support/known_issues/index.en.html).
# Get Tails 3.6.2
* To install, follow our [installation
Hi !
since there was a release a few days ago, I thought you'd like a quick report
about what users complained about.
- a lot of non english users complained about tails installer not letting them
click on install [1].
- some electrum users that were freaking out about the vulnerability
Hi !
there was two issues that were reported by several users this week,
first, we had a few (less than 5) reports (some with log and bridge
list) about obfs4 not working, so I updated #9268 and sent the logs to
intrigeri
and multiple (5 or more) reports about tails installer silently failing
Hi !
>
> and several users reported that installing by cloning "didn't worked"
> (the window shut down and tails is not installed), apparently on devices
> made with UUI. I lack information so I'll try to reproduce before
> opening a ticket
>
I couldn't reproduce
Hi !
a lot of users were affected by
https://tails.boum.org/news/version_3.0/#known-issues
we've got a few reports of users having trouble with nividia (mostly
geforce 970) workarounded by adding nouveau.modeset=0 (likely #11831,
but they didn't seem affected with tails 2.*)
2 users affected
Mike,
good idea to hide the target ...
> I've only used Tails a handful of times. I had my browser crash while
> researching a bit ago, and I'm assuming it was from an exploit. Firefox is
> full of holes,
If you boot tails from a cd and if you do not use persistence, an
exploit fr
onally (to better understand what is working, and what's still
> not supported), and to allow us to update the known issues pages.
I asked the users to report back on redmine, but it seems they usually
don't, anyway, I'll take some time to dig into my mailbox.
cheers.
pgpVRLc3pokv0.pgp
Description
Tor Browser isn't built on ARM yet)
No. I still couldn't build all tails packages (and the tor browser is
not a tails package)
--
Best Regards!
n9iu7pk
PGP pool.sks-keyservers.net 0x4D12FFCB
7426 4598 B5AD 4D12 1699 C710 D602 E331 4D12 FFCB
redm...@labs.riseup.net:
> Issue #10972 h
26 4598 B5AD 4D12 1699 C710 D602 E331 4D12 FFCB
intrigeri:
> I think it's much simpler.
>
> Basically, the only custom APT suite we'll be using in next Tails
> major release is the 'devel' one ⇒ just rebuild the packages that are
> currently in there. What are these packages?
>
Hi developers,
intrigeri asked:
> I don't understand: why are you rebuilding all packages, instead of
> just the Tails -specific ones (that are not in Debian)?
I tried to build only the packages from repository
http://deb.tails.boum.org/.
Am I on the wrong route (or repository)? Or could a
not haven been build during the package build.
Yes, booring job but I'll investigate ... package for package.
>> > But isn't there a tails test repro, where I can upload arm packages to
>> > test?
> Not quite at the moment, however, you should be able to run the test
>
Hi Dr_Whax
> Hey, if you have any issues with the development environment, feel
free to send an e-mail to the tails-dev list :)
THANKS! Off course, I have a lot of, just take look into attached
statePackages.txt and search for "FAILED.deb" extended with comments.
Some examples:
- ./
See
https://jenkins.tails.boum.org/job/build_Tails_ISO_feature-jessie/594/changes
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr
(Engine.java:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
(Engine.java:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
(Engine.java:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
(Engine.java:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
(Engine.java:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
See
https://jenkins.tails.boum.org/job/build_Tails_ISO_feature-jessie/586/changes
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr
(Engine.java:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
(Engine.java:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
(Engine.java:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
(Engine.java:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
(Engine.java:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
(Engine.java:63)
at java.lang.Thread.run(Thread.java:701)
___
Tails-dev mailing list
Tails-dev@boum.org
https://mailman.boum.org/listinfo/tails-dev
To unsubscribe from this list, send an empty email to
tails-dev-unsubscr...@boum.org.
201 - 300 of 508 matches
Mail list logo
